
Create a new database named “company”.
Answer: CREATE DATABASE company;
Create a table named “employees” with columns for id (integer, primary key), name (varchar), age (integer), and department (varchar).
Answer: CREATE TABLE employees (id INT PRIMARY KEY, name VARCHAR(255), age INT, department VARCHAR(255));
Create a table named “products” in the “company” database with columns for id (integer, primary key), name (varchar), price (decimal), and quantity (integer).
Answer: CREATE TABLE company.products (id INT PRIMARY KEY, name VARCHAR(255), price DECIMAL(10, 2), quantity INT);
Alter the “employees” table to add a new column named “salary” (integer).
Answer: ALTER TABLE employees ADD COLUMN salary INT;
Alter the “products” table to add a new column named “description” (text).
Answer: ALTER TABLE company.products ADD COLUMN description TEXT;
Alter the “products” table to modify the data type of the “price” column to FLOAT.
Answer: ALTER TABLE company.products MODIFY COLUMN price FLOAT;
Alter the “products” table to rename the column “quantity” to “stock”.
Answer: ALTER TABLE company.products RENAME COLUMN quantity TO stock;
Drop the “salary” column from the “employees” table.
Answer: ALTER TABLE employees DROP COLUMN salary;
Insert a new record into the “products” table in the “company” database with values for id, name, price, and stock.
Answer: INSERT INTO company.products (id, name, price, stock) VALUES (1, 'Laptop', 999.99, 50);
Insert multiple records into the “products” table in the “company” database with values for id, name, price, and stock.
Answer: INSERT INTO company.products (id, name, price, stock) VALUES (2, 'Smartphone', 499.99, 100), (3, 'Tablet', 299.99, 75), (4, 'Headphones', 99.99, 200);
Insert a new record into the “employees” table with values for id, name, age, and department.
Answer: INSERT INTO employees (id, name, age, department) VALUES (1, 'John', 35, 'HR');
Insert a new record into the “employees” table with values for id, name, age, department, and salary.
Answer: INSERT INTO employees (id, name, age, department, salary) VALUES (4, 'Alice', 28, 'Marketing', 50000);
Update the price of the product with id 2 to 549.99 in the “products” table.
Answer: UPDATE company.products SET price = 549.99 WHERE id = 2;
Update the stock of the product with id 1 to 40 and its price to 899.99 in the “products” table.
Answer: UPDATE company.products SET stock = 40, price = 899.99 WHERE id = 1;
Update the age of the employee with id 1 to 30 in the “employees” table.
Answer: UPDATE employees SET age = 30 WHERE id = 1;
Update the department of the employee with id 2 to ‘Finance’ in the “employees” table.
Answer: UPDATE employees SET department = 'Finance' WHERE id = 2;
Delete the record with id 3 from the “products” table in the “company” database.
Answer: DELETE FROM company.products WHERE id = 3;
Delete all records from the “products” table where the price is less than 100.
Answer: DELETE FROM company.products WHERE price < 100;
Delete all records from the “products” table.
Answer: DELETE FROM company.products;
Delete all records from the “employees” table where the age is greater than 50.
Answer: DELETE FROM employees WHERE age > 50;
Delete the employee with id 3 from the “employees” table.
Answer: DELETE FROM employees WHERE id = 3;
Select all columns from the “employees” table.
Answer: SELECT * FROM employees;
Select only the “name” and “age” columns from the “employees” table.
Answer: SELECT name, age FROM employees;
Select all employees from the “employees” table where the department is ‘IT’.
Answer: SELECT * FROM employees WHERE department = 'IT';
Select all employees from the “employees” table where the age is between 25 and 35.
Answer: SELECT * FROM employees WHERE age BETWEEN 25 AND 35;
Select all employees from the “employees” table sorted by age in ascending order.
Answer: SELECT * FROM employees ORDER BY age ASC;
Select the oldest employee from the “employees” table.
Answer: SELECT * FROM employees ORDER BY age DESC LIMIT 1;
Retrieve unique values from the “department” column in the “employees” table.
Answer: SELECT DISTINCT department FROM employees;
What is the difference between Data and Information?
What do you mean by Field, Attribute, Record, Table, and Database?
What is a Database Management System?
What are the types of keys in DBMS?
What are the advantages of DBMS over Excel?
Differentiate between DDL and DML.
What is SQL?
What is the purpose of SQL?
What is the purpose of the SELECT statement in SQL?
What is the meaning of * in Select Statement in SQL?
What is the difference between DELETE and Drop commands?
What is the difference between DELETE and TRUNCATE commands?
What is the purpose of the WHERE clause in SQL?
What is the purpose of the INSERT statement in SQL?
What is the purpose of the UPDATE statement in SQL?
What is the purpose of the DELETE statement in SQL?
What is the purpose of the ORDER BY clause in SQL?
What is client-side scripting, and how does it differ from server-side scripting?
Name some popular client-side scripting languages.
How do we create comments in JavaScript?
In JavaScript, you can create comments using two different methods:
// and continue until the end of the line. They are used for brief explanations or annotations.
// This is a single-line comment
/* and end with */. They can span multiple lines and are typically used for longer explanations or commenting out blocks of code.
/*
This is a multi-line comment.
It can span multiple lines and is useful for longer explanations.
*/Explain about Global and Local Variable.
Global Variables:
var globalVar = 10;
function myFunction() {
console.log(globalVar);
}
Local Variables:
function myFunction() {
var localVar = 20;
console.log(localVar);
}Differentiate between null and undefined.
null:
null is a primitive data type.var x = null;
undefined:
undefined is a primitive data type.var y;How do you create an array in JavaScript?
Explain the concept of event handling in client-side scripting.
What is JavaScript, and how does it enhance web development?
Explain the various methods to include JavaScript code in an HTML page.
What are the different attributes of the <script> tag, and how do they affect script execution?
Discuss the placement of <script> tags within an HTML document and its implications.
<head> delays rendering, while placing them at the end of the <body> improves page loading.Explain the concept of inline JavaScript and its advantages and disadvantages.
Explain how to use JavaScript to manipulate HTML elements and modify the content and style of a web page.
getElementById, querySelector, and properties like innerHTML and style.Explain the difference between JavaScript and Java.
What are the basic building blocks of JavaScript programs?
What are data types in JavaScript?
Discuss the role of type coercion in JavaScript and provide examples.
5 + '5' results in the string '55' due to implicit type coercion.What is a variable in JavaScript, and how do you declare one?
var, let, or const keyword, followed by the variable name.Explain the rules for naming variables in JavaScript.
$, or underscore _, followed by letters, digits, dollar signs, or underscores. They cannot be reserved words.Discuss the difference between var, let, and const for declaring variables.
var declares a variable with function scope, let declares a variable with block scope, and const declares a constant variable that cannot be reassigned.Explain the concept of hoisting in JavaScript variable declaration.
What are operators in JavaScript, and what categories do they fall into?
Discuss the difference between unary, binary, and ternary operators, providing examples of each.
++x), binary operators operate on two operands (e.g., x + y), and ternary operators operate on three operands (e.g., condition ? value1 : value2).Explain the use of arithmetic operators in JavaScript with examples.
+, subtraction -, multiplication *, division /, and remainder %.Discuss the importance of operator precedence and associativity in JavaScript expressions.
Explain the use of comparison operators and logical operators in JavaScript with examples.
true or false). Logical operators perform logical operations and return a Boolean result.What are the various pop-ups in JavaScript?
In JavaScript, you can create various types of pop-ups to interact with users.
alert("Message");
var result = prompt("Enter your name:", "");
var result = confirm("Are you sure?");Differentiate between console.log() and document.write()?
console.log() are visible only to developers in the browser’s console and are not displayed on the webpage itself.console.log("Hello, world!");
document.write() is added directly to the document and is visible to users on the webpage.document.write("<h1>Hello, world!</h1>");
How do we convert a string with numeric value to integer data type?
parseInt() and Number() are both functions in JavaScript used for converting values to numbers.
What is a function in JavaScript?
How do you declare a function in JavaScript?
function keyword followed by the function name, parameters (if any), and function body enclosed in curly braces.Explain the difference between function declarations and function expressions.
function keyword followed by a name, while function expressions are created by assigning a function to a variable.What are the parameters and arguments in a function?
Explain the concept of return values in functions.
return keyword.What is the if-else statement, and how is it used in JavaScript?
Explain the syntax and usage of the if-else-if statement in JavaScript.
How do you use the switch-case statement in JavaScript?
What are the types of loops in JavaScript?
Discuss the syntax and usage of the for loop in JavaScript.
Explain the syntax and usage of the while loop in JavaScript.
How do we create exception handling in JavaScript?
In JavaScript, you can perform exception handling using try, catch, and finally blocks.
try {
var result = 10 / 0; // This will throw a division by zero error
console.log(result); // This line won’t be executed }
catch (error) {
console.error(“An error occurred:”, error); }
finally {
console.log(“Execution completed.”); // This line will always be executed
}
Explain the concept of objects in JavaScript.
How do you create objects in JavaScript?
{}, constructor functions with the new keyword, or Object.create() method.What are events in JavaScript, and how are they triggered?
How do you handle events in JavaScript?
addEventListener().What is the Image object in JavaScript?
<img> element, allowing manipulation of images dynamically within JavaScript.How do you create an Image object in JavaScript?
new Image() constructor or by assigning a new image element to a variable.What properties and methods does the Image object provide?
src, width, height, alt, and methods include addEventListener(), removeEventListener(), complete, onload, and onerror.What is the Form object in JavaScript?
<form> element, providing access to its properties and methods for form manipulation.How do you access a Form object in JavaScript?
document.forms collection or by using the getElementById() or querySelector() methods.What properties and methods does the Form object provide?
action, method, elements, and methods include submit(), reset(), and addEventListener().What is form validation, and why is it important in web development?
Explain the difference between client-side and server-side form validation.
What are some common techniques for client-side form validation in JavaScript?
required, minlength, etc.What is jQuery, and how does it simplify DOM manipulation and event handling?
How do you include jQuery in a web page, and what is the jQuery syntax for selecting elements?
<script> tag referencing the jQuery library. Syntax for selecting elements: $(selector).What is a function in C programming?
What is the purpose of using functions in C?
How do you define a function in C?
What is the difference between a function declaration and a function definition?
What is a function prototype in C?
What is the difference between a library function and a user-defined function?
What are the advantages of using functions in programming?
What are function parameters?
How are function parameters passed in C?
What is the difference between call by value and call by reference?
How do you specify the return type of a function in C?
Can a function return multiple values in C?
What is recursion in C?
What are the necessary conditions for recursion?
How does recursion work in C?
What is a structure in C programming?
How do you define a structure in C?
struct keyword followed by the structure name and a list of member variables enclosed in curly braces.What is the difference between structure definition and declaration?
How do you initialize a structure in C?
How is the size of a structure calculated in C?
How do you access members of a structure in C?
.) operator followed by the member name.What is an array of structures in C?
What is a union in C programming?
How do you define a union in C?
union keyword followed by the union name and a list of member variables enclosed in curly braces.What is the difference between a union and a structure in C?
What is a pointer in C programming?
What is a data file in C programming?
What is the purpose of using data files in programming?
What is a sequential file?
What is a random file?
What is the purpose of putw() and getw() functions in C?
Explain the usage of putc() and getc() functions in C.
What are fscanf() and fprintf() functions used for in C?
How do you open a file in C for reading?
What is the difference between writing and appending to a file?
How do you close a file in C after reading or writing?
What is server-side scripting, and how does it differ from client-side scripting?
Name some popular server-side scripting languages.
How does a server-side script interact with a web server?
Explain the typical workflow of a server-side script.
What are the advantages of server-side scripting?
What are the hardware and software requirements for running PHP?
Explain the concept of object-oriented programming in PHP.
What is the basic syntax of PHP?
What are the various data types supported by PHP?
Discuss the different types of operators in PHP.
How do you manipulate variables in PHP?
Explain database connectivity in PHP.
What are the steps involved in connecting a server-side script to a database in PHP?
How do you make SQL queries in PHP?
What does fetching data sets mean in PHP?
How do you create an SQL database using server-side scripting in PHP?
Discuss the process of displaying queries in tables using PHP.
How do you define a class in PHP?
What is the significance of the ‘new’ keyword in PHP?
Explain the difference between == and === operators in PHP.
How do you declare and initialize variables in PHP?
What is SQL injection, and how can it be prevented in PHP?
Discuss the role of the mysqli and PDO extensions in PHP.
How do you handle errors during database connectivity in PHP?
Explain the concept of inheritance in object-oriented programming with PHP.
What are the different types of loops supported in PHP?
Discuss the role of constructor and destructor methods in PHP classes.
How do you execute conditional statements in PHP?
Explain the concept of method overloading in PHP.
What is the purpose of the php.ini file in PHP?
How do you retrieve data from a form submitted via POST method in PHP?
Explain the process of handling file uploads in PHP.
What are the different types of errors that can occur in PHP scripts?
How do you include external PHP files within a script?
What is the purpose of the ‘use’ keyword in PHP namespaces?
Discuss the concept of autoloading classes in PHP.
Explain the difference between GET and POST methods in form submissions.
What is the purpose of the global keyword in PHP?
How do you handle sessions in PHP?
Explain the concept of method chaining in PHP.
What is the purpose of the header() function in PHP?
Discuss the significance of sanitizing user input in PHP.
What is the purpose of the empty() function in PHP?
Explain the concept of method visibility in PHP classes.
How do you define constants in PHP?
Discuss the role of namespaces in PHP.
What is the purpose of the setcookie() function in PHP?
Explain the difference between require and include statements in PHP.
AI stands for Artificial Intelligence. It is a concept of giving human-like intelligence to the machines. Though the computers do their work faster and better than the human beings, the intelligence of them is zero because they just follow the set of instructions given by the user. In case of wrong instruction, they do wrong processing. It is because they do not have intelligence of their own. So, the scientists are in research of giving them artificial intelligence, so that they can understand the natural languages of the human beings and interact. They can express their feelings and many more.

Components of AI
Different disciplines contributed their ideas, viewpoint, and techniques to plan the foundation of Al that acts as components of Al. Some of the major contributions of various disciplines an given below:
Uses/Applications of Al
The potential applications of Artificial Intelligence are abundant (plentiful). They stretch from the military for autonomous control and target identification, to the entertainment industry for computer games and robotic pets. Let’s also not forget big establishments dealing with huge amounts of information such as hospitals, banks, industries, and insurances, which can use Al to predict customer behavior and detect trends.
General game playing (GGP) and General video game playing (GVGP) is the concept and designs for artificial intelligence programs to successfully play plenty of games. For video games, game rules have to be either learned over multiple repetitions by artificial players or are predefined manually in a domain-specific language and sent in advance to artificial players. For instance, the GGP of chess, computers are programmed to play these games using a specially designed algorithm. It was considered a necessary landmark on the way to Artificial General Intelligence. The first commercial practice of general game-playing technology was Zillions of Games in 1998.
In speech recognition, the input is given to the computer in the form of vibrations produced by the sound. This is done with the help of an analog to digital converter that converts the vibrations produced by the sound into digital format.
Then, a set of complex algorithms runs on that data to recognize the speech and return a text as a result. Depending upon the goal, the end result may vary to some extent. For example, Google Voice typing converts spoken words into suitable text format while personal assistants like Siri and Google Assistant take the sound as input and convert it into both voice and text format, giving output as per the user’s requirement.
Natural language understanding is a branch of artificial intelligence that uses computer software to take the input in the form of sentences using text or speech. It simply reduces the gap between humans and computers allowing them to interact easily with each other.
Computer vision is a field of artificial intelligence (AI), which enables the computer and its systems to get input in the form of digital images and videos and take action based on the provided input.
An expert system is a computer system that mimics or even surpasses the decision-making ability of a human expert. It is generally designed to solve complex problems by surfing through bodies of knowledge. It is further divided into two subsystems; the knowledge base (which represents facts and rules) and inference engine (which applies the rules to the known facts to deduce new facts).
Artificial intelligence (AI) in robotics is the ability of the computer or the robot to perform multiple tasks performed by humans, which require human intelligence and discernment. It gives robots a computer vision to navigate, sense, and calculate their reaction accordingly For example: Robotic packaging uses various forms of Al for quicker and accurate packaging at a lower price. Likewise, Sophia which is also marked as a “social robot” is successfully able to mimic social behavior and induce feelings of love in humans.
Proving theorems requires high intelligence as many of the practical problems can be cast in terms of theorems. If knowledge is expressed by logic, proving theorem is reasoning. It uses various AI techniques such as heuristic search.
Symbolic mathematics refers to the manipulation of formulas, rather than doing arithmetic on numeric values. It is often used in conjunction with ordinary scientific computation as a generator of programs, used to actually do the calculations.
Artificial intelligence (AI) in robotics is the ability of the computer or the robot to perform multiple tasks performed by humans, which require human intelligence and discernment. It gives robots a computer vision to navigate, sense, and calculate their reaction accordingly For example: Robotic packaging uses various forms of Al for quicker and accurate packaging at a lower price. Likewise, Sophia which is also marked as a “social robot” is successfully able to mimic social behavior and induce feelings of love in humans.
Proving theorems requires high intelligence as many of the practical problems can be cast in terms of theorems. If knowledge is expressed by logic, proving theorem is reasoning. It uses various AI techniques such as heuristic search.
Symbolic mathematics refers to the manipulation of formulas, rather than doing arithmetic on numeric values. It is often used in conjunction with ordinary scientific computation as a generator of programs, used to actually do the calculations.
Cloud computing is the use of various services, such as software development platforms, servers, storage, and software, over the Internet, often referred to as the “cloud”. It is defined as a type of computing that relies on sharing computing resources rather than having handle applications. In cloud computing, the word cloud is used to represent “the Internet,” so the phrase cloud computing means “a type of Internet-based computing,” where different services – such as servers, storage, and applications are delivered to an organization’s computers and devices through the Internet. Cloud computing allows application software to be operated using internet-enabled devices.

Types of Clouds
Clouds can be classified as public, private, and hybrid. Public cloud is made available to the general public or a large industry group. Private cloud computing environment resides within the boundaries of an organization and is used exclusively for the organizational benefits Hybrid cloud is the combination of both public and private cloud. Sensitive With this cloud organizations might run non-core applications in a public cloud, while maintaining core applications and data in a private cloud.
Service Models of Cloud Computing

Advantages of Cloud Computing:
Some of the advantages of this technology are:
Disadvantages of Cloud Computing:
Despite its many benefits, as mentioned above, cloud computing also has its disadvantages.
Big Data refers to complex and large data sets that have to be processed and analyzed to uncover valuable information that can benefit businesses and organizations. It has features like:
According to Gartner, the definition of Big Data- “Big data is high-volume, velocity, and information assets that demand cost-effective, innovative forms of information processing for enhanced insight and decision making.”
Types of Big Data
Big data can be classified as Structured, unstructured, and semi-structured.
Characteristics of Big Data
The main characteristics of big data are:
Application Areas of Big Data
Major application of big is data is:
Advantages of Big Data Processing:
Some of the advantages of big data processing are:
Disadvantages of Big Data Processing:
Despite its many benefits, big data processing has the following disadvantages.
Virtual reality (VR) is a term that expresses computer-based simulated environments. Which can perceive as in the real world, as well as in unreal worlds. The virtual reality environments are primarily concerned with the visual experiences, displayed either on a computer screen or through special stereoscopic displays, but some simulations include additional sensory information, such as sound through speakers or headphones.
Virtual reality creates such a realistic artificial environment that the s/he should feel as in the real world. Today the Virtual reality (VR) technology is applied to advance fields of medicine, engineering, education, design, training, and entertainment.

Some of the application areas of virtual reality are:
Advantages of Virtual Reality:
Some of the advantages of virtual reality are:
Disadvantages of Virtual Reality:
Some of the disadvantages of virtual reality are:
Electronic commerce (e-Commerce) is a process of buying and selling or exchanging products, services, and information using electronic media. There are many definitions for electronic commerce that include elements of electronic transactions and the buying and selling of goods and services online.
e-Commerce is a modern business methodology that addresses the needs of organizations, merchants, and consumers to cut costs while improving the quality of manufactured goods, services and increasing the speed of service delivery. More commonly, e-commerce is associated with the buying and selling of products, and services via computer networks. The main platforms of e-commerce remain the Internet, e-mail, fax, telephone orders.

Classification of e-Commerce
Advantage of e-Commerce
Some of the advantages of e-commerce are:
Disadvantage of e-Commerce
e-Medicine is an online clinical medical knowledge database, which is an approach to providing health care service to a large number of people spread in different locations. It is mainly beneficial for the people of rural areas with limited or no medical facilities. e Medicine is targeted to provide high-quality healthcare service. It minimizes the time and cost required for treatment.
e-Medicine usually contains up-to-date, searchable, peer-reviewed medical journals, online physician reference textbooks, and a complete article database on medical specialties. This Internet medical library and clinical knowledge base are available to physicians, medical students, nurses, other health professionals, and patients.
With the use of e-Medicine, doctors and patients who are physically apart can connect so that patients can share his/her problem with the doctor, and the doctor can suggest treatment or any test required.
e-Governance is the use of information and communication technology (ICT) to enhance the access and delivery of government services to benefit citizens, business partners, and employees. It transforms the traditional government using ICT to make it clear, effective, and accountable. However, it doesn’t mean that putting more computers on the desks of government officials is e governance.

Governance is more than just a government website on the Internet. Political, social, economic, and technological aspects determine e-governance. It establishes a relationship between government officials and citizens, providing greater access to government information and services by making the government accessible online, promoting citizen participation by enabling citizens to interact more conveniently with government officials, such as by requesting government service and filing required documents through the website, increasing government accountability by making its operations more transparent, thereby reducing the opportunities for corruption, and supporting development goals by providing business, rural and traditionally underserved communities with information, opportunities, and communications capabilities.
For example,
https://www.nepal.gov.np/, https://www.moe.gov.np/, https://www.moha.gov.np/
Objectives of e-Governance
Some of the objectives of e-Governance are:
⮚ E-Governance refers to the provision of online public services to citizens and businesses.
⮚ Services for citizens include the registration to government services such as health care, education, or employment benefits.
⮚ For businesses, E-Governance services can take the form of online alerts for public procurements or funding opportunities as well as information and support on applicable legislation in a given sector.
⮚ E-Governance helps to cut down their administrative costs, speed up procedures and therefore increase efficiency and reactivity.
⮚ It could improve and accelerate administrative efficiency.
Challenges of implementing e-Governance
The key challenges of implementing E-Governance mainly in developing countries like Nepal are
⮚ High-speed infrastructure to access the Internet is required.
⮚ Creating trust and transparency of successful delivery of E-Governance service.
⮚ The digital divide exists in developing countries. All the citizens may not have ICT knowledge.
⮚ Network security and protection against viruses, spam, unwanted attacks, etc.
⮚ Online privacy.
⮚ All the citizens may not have access to computing resources.
Mobile computing is a generic term describing one’s ability to use technology while moving as opposed to portable which is only practical for use while deployed in a stationary configuration. A mobile computing device is created using mobile components, such as mobile hardware and software. Mobile computing devices are portable devices capable of operating executing, providing services and applications like a computing device. It is a computing device used in transit. Users can access data and information from wherever they are.
Many types of mobile computers have been introduced since the 1990s, including a wearable computer, PDA, enterprise digital assistant, smartphone, UMPC (Ultra-mobile PC), Tablet PC.

Features of Mobile Computing Device
Features of Mobile Computing devices are
⮚ It is a portable device that can be used during mobility.
⮚ It has limited processing and storage capability.
⮚ It includes mobile communication, mobile hardware, and mobile software.
⮚ It usually contains a touch screen for providing input.
⮚ It contains an on-screen or virtual keyboard for proving text inputs. However, an external keyboard can be connected by using the USB port, infrared, or Bluetooth.
⮚ It contains a camera, speaker, and microphone.
⮚ It contains handwriting recognizing software.
⮚ Most mobile computing devices contain a memory card slot to expand the storage capacity.
⮚ It has wireless connectivity such as Bluetooth, Wi-Fi to connect the Internet or with other computing devices as well as a wired connection through the USB port connectivity services like need either Wi-Fi.
⮚ The most mobile computing device can synchronize their data with applications on users’ computers.
⮚ It can be used for cloud computing and remote access.
⮚ It uses a mobile computing operating system such as Android, iOS, Windows Mobile OS, Palm OS.
⮚ It can include GPS (Global Positioning System) receiver for navigation.
Advantages of Mobile Computing
Advantages of mobile technology are:
⮚ It enables users to work from any location at any time.
⮚ It saves time for accessing data and information.
⮚ It helps to increase the productivity of users reducing the time and cost.
⮚ It has made research easier.
⮚ It is one of the major handheld sources of entertainment of users at present.
⮚ Nowadays, Business processes are easily available through secured mobile connections.
⮚ It is portable.
⮚ It supports cloud computing.
⮚ It provides remote access to the organizational data from any location.
⮚ It is an independent platform. It can be accessed from any hardware or software.
Disadvantages of Mobile Technology
⮚ Mobile technology requires faster and quality or GPRS or 3G or 4G connectivity.
⮚ It has security concerns; most wireless connectivity is unsafe.
⮚ Large power consumption is due to the use of batteries continuously and they do not tend to last long.
⮚ The danger of misrepresentation i.e., credential
⮚ Extensive use of mobile devices results in health problems.
Internet of things (IoT) is the network of physical devices, vehicles, home appliances, and other items embedded with electronics, software, sensors, actuators, and connectivity, which enables these things to connect, collect and exchange data.
The Internet of Things (IoT) is a system of interrelated computing devices, mechanical and digital machines, objects, animals, or people that are provided with unique identifiers (UIDs) and the ability to transfer data over a network without requiring human-to-human or human to-computer interaction.
By combining these connected devices with automated systems, it is possible to “gather information, analyse it and create an action” to help someone with a particular task or learn from a process. A thing in the internet of things can be a person with a heart monitor implant, an animal with a biochip transponder, an automobile that has built-in sensors to alert the driver when tire pressure is low, or any other natural or man-made object that can be assigned an Internet Protocol (IP) address and can transfer data over a network.

Advantages of IoT:
⮚ It automates tasks and helps to improve the quality of a business’s services and reduces.
⮚ It helps to operate the business operations more efficiently, better understand customers to deliver enhanced customer service.
⮚ It supports to improve decision-making and increases the value of the business.
⮚ It has the ability to access information from anywhere at any time on any device.
⮚ It provides improved communication between connected electronic devices.
⮚ Transferring data packets over a connected network saves time, effort, and money.
Disadvantages of IoT:
⮚ As the number of connected devices increases and more information is shared between devices, the chances of the system being attacked also increases.
⮚ Organizations may eventually have to deal with massive numbers (maybe even millions) of IoT devices, and collecting and managing the data from all those devices will be challenging.
⮚ If there’s a bug in the system, every connected device will likely become corrupted.
⮚ Since there’s no international standard of compatibility for IoT, it’s difficult for devices from different manufacturers to communicate with each other.
e-Learning applies to a learning/teaching or understanding about a topic with the help of Information and Communication Technology. e-Learning allows us to learn anywhere and usually at any time, as long as we have a properly configured computer, networks, devices, etc. e-Learning can be CD ROM-based, Network-based, Intranet-based, or Internet-based.

It can include text, video, audio, animation, and virtual environments. It can be a very rich learning experience that can even go beyond the lecture-based crowded classroom. It’s a self paced, hands-on learning experience. The quality of the electronic-based training, as in every form of training, is in its content and its delivery. However, e-learning can suffer from many of the same pitfalls (drawbacks) as classroom training, such as boring slides, monotonous speech, and little opportunity for interaction. The beauty of e-learning is that new software that allows the creation of very effective learning environments that can overcome the classic material being used in traditional learning. For example, http://www.howstuffworks.com/
The concept of e-learning has become more popular throughout the globe because of the Covid 19 pandemic. The tools like Zoom, Microsoft Teams, Cisco Webex Meetings, Google Meet are also used for learning purposes.
m-Commerce (mobile commerce) is the buying and selling of goods and services through wireless technology i.e., handheld devices such as cellular telephones and personal digital assistants (PDAs).

Industries affected by m-commerce include:
⮚ Financial services, including mobile banking (when customers use their handheld devices to access their accounts and pay their bills), as well as brokerage services (in which stock quotes can be displayed and trading conducted from the same handheld device).
⮚ Telecommunications, in which service changes, bill payment, and account reviews can all be conducted from the same handheld device.
⮚ Service/retail as consumers is given the ability to place and pay for orders on the fly.
⮚ Information services, which include the delivery of entertainment, financial news, sports figures, and traffic updates to a single mobile device.
Social Media is a computer-based technology that is used for the creation and sharing of information, ideas, interests, and other forms of expression via virtual communities and networks. Facebook, Twitter, YouTube are popular social media tools.

Advantages of Social Media:
⮚ It provides easier and faster way to communicate.
⮚ It provides worldwide real-time sharing of news and educational content.
⮚ It is one of the effective marketing/advertising tools at present.
⮚ It is the major source of entertainment at present.
⮚ It helps to understand better the latest trends and events.
Disadvantages of Social Media:
⮚ It has increased cyber-crime.
⮚ Productive times is lost due to time waster in social media.
⮚ It is a common tool at present for spreading rumours and fake news/updates.
⮚ It has a high risk of fraud.
⮚ It has decreased privacy.
The program is a sequence of instructions. It is the set or collection of instructions.
An instruction is a command given to the computer to perform a certain specified operation on given data.
A set of programs written for a computer to perform a particular task is called software or the logical components or set of procedures to routines or instructions are called software is the interface between the computer and the user. It is a group of commands that tells the computer what to do and how to do it.
A project is a well-defined task, which is a collection of several operations done in order to achieve a goal (for example, software development and delivery).
A software project is the complete procedure of software development from requirement identification to testing and maintenance, carried out according to the execution methodologies, in a specified period of time and budget in order to achieve intended software product.
⮚ Software development process defines a sequence of tasks that must be carried out to build new software.
⮚ It groups the development activities into a sequence of phases.
⮚ A phase in sequence can only commence on the previous phase has been completed.
⮚ A report is produced at the end of each phase, describing what has been achieved and outlining the plan for the next phase.

Fundamental activities for the software development process are
System:
System is a set of interacting or interdependent components forming an integrated whole. A system can be described as a set of objects joined together for a common objective.
Development:
It is the process of step by step changing or growing of any program and system.
Information System:
Information system is a system which processes supplied/collected data and generates information that can be used for decision making at different levels.
SDLC (Software/System Development Life Cycle) is an organized way to develop a software/system. System Development Phase or System Development Life Cycle or Software Development Life Cycle (SDLC) is a methodology used to develop, maintain, and replace software/information systems.
⮚ It is a systematic process of developing any software. It helps in establishing a system, or software or project, or plan. It gives an overall list of processes and sub-processes required for developing a system.
⮚ SDLC consists of a set of development activities that have a prescribed order. It is the development of software in chronological order.
System Development Life Cycle (SDLC), which is also known as Application Development Life Cycle, is a term used in system that describes the process of planning, creating, testing and deploying an information system.
Importance and the necessity of SDLC
The different phases of SDLC are as follows:

A system is intended to meet the needs of an organization. Thus the first step in the design is to specify these needs or requirements. The top manager of the organization takes the basic decision to use a computer based (information) system for managing the organization.
During this phase, the development team focuses on completing three tasks:
– Survey the system by collecting the inputs from various sources.
– Analyzing the current system (manual or automated) in depth and developing possible solutions to the problem.
– Selecting to the best solution and defining its function with a feasibility study.
System analysis is the dissection of a system into its component pieces to study how those component pieces interact and work.
⮚ System analysis is a term that collectively describes the early phases of development.
⮚ It is defined as those phases and activities that focus on the business problem, independent of technology.
In this stage, the development team once again goes to the organization and studies very minutely to collect all the drawbacks and details of information from the users, management and data processing personnel.
Then the system analyst analyzes the information and proposes the following specifications.
Feasibility study is the most important activity in the system analysis phase. It analyses the proposed system from different aspects so that it makes us clear that how practical or beneficial the system will be to the organization. So it tells us whether the system is feasible to design nor not.
Need of feasibility study
⮚ It determines whether the system meets the goal of the clients or not.
⮚ It determines the strength and limitations before starting to develop the system.
⮚ It focuses on the boundary of the system’s outline.
⮚ It suggests new opportunities through the investigations process.
⮚ It provide quality information for decision making.
⮚ To provide documentation of the investigated system.
The different levels of feasibility study are as:
1) Economic feasibility: it concerns with cost effectiveness of the system. The main objective of economic feasibility is to calculate approximate cost-both the development cost and the operational cost and the benefits from the system.
2) Technical feasibility: it concerns with the availability of the hardware, software and the support equipment for the complete development of the system.
3) Operational feasibility: it concerns with smooth operation of the system. It is all about the problems that may occur during operation of the system after its development.
4) Behavior feasibility: it concerns with behavior of the users and the society towards the new system. Generally, most of the traditional employees are not easily ready to upgrade them with the new system.
5) Social Feasibility: It is a determination of whether a proposed system will be acceptable to the people or not.
6) Management Feasibility: It is a determination of whether a proposed system will be acceptable to management or not.
7) Schedule(Time) feasibility: it is the process of splitting project into tasks and estimate time and resources required to complete each task. It determines the deadline to complete a system and schedule the task accordingly.
8) Legal feasibility: it concerns with legal issue of the system. If the system is illegal then the system designing is meaningless. Everything is measured whether it is legal or illegal. It considers copyright law, foreign law, foreign trade, tax, etc.
The next step is to develop the logical design of the system. During this phase, the logic of the system, namely, the information requirement of users, and use this to find the necessary database.
System design is concerned with the design of new system. It involves designing of various things such as output design, input design, files design, processing and general program design etc.
Logical Design: Theoretically designing of the system is called logical design. The system could be designed on the basis of the requirements.
Physical Design: The conversion of logical design into designing tools and techniques is called physical design. It is more detail and complex jobs describing the solution of the problem. It uses algorithms, flowcharts, pseudo codes, decision table, decision tree, E-R diagram, Data flow diagram etc.
Theoretically designing of the system is called logical design. The system could be designed on the basis of the requirements.
The conversion of logical design into designing tools and techniques is called physical design. It is more detail and complex jobs describing the solution of the problem.
To create the logical design different kinds of tools are used.
⮚ Algorithm ⮚ Decision Table
⮚ Flowchart ⮚ Decision Tree
⮚ Pseudo codes ⮚ Data flow diagram
⮚ Structured English ⮚ E-R diagram
System analyst is person who is involved in analyzing, designing, implementing and evaluating computer based information systems to support the decision making activities and operations of an organization.
A good system analyst is:
⮚ A system analyst is information specialist. To be a system analyst, one must be knowledgeable about the technical aspects of analyzing, designing and implementing computer-based systems.
⮚ A system analyst is a person who conducts a study, identifies activities and objectives and determines a procedure to achieve the objectives.
Designing and implementing systems to suit organizational needs are the functions of the systems analyst. One plays a major role in seeing the business benefits from computer technology. An analyst is a person with unique skills. One uses these skills to coordinate the efforts of different types of persons in an organization to achieve business goals.
The characteristics (attributes) of system analyst are as follows:
➔ Defining the problem
➔ Analyzing the problem
➔ Evaluating many alternatives
➔ Choosing the best alternatives
➔ System analysis and Design skills
The roles of system analyst area as follows:
Duties and Responsibilities of System Analyst
Describes in Details:
In this stage, the development team studies the present and identifies the drawbacks. They interact with the users and gathers information from different sources to recognize the problems of present system.
In this stage, the development team once again goes to the organization and studies very minutely to collect all the drawbacks and details of information from the users, management and data processing personnel.
Then the system analyst analyzes the information and proposes the following specifications.
Feasibility study is the most important activity in the system analysis phase. It analyses the proposed system from different aspects so that it makes us clear that how practical or beneficial the system will be to the organization. So it tells us whether the system is feasible to design nor not. Thus it is necessary before system design.
The different levels of feasibility study are as:
System design is concerned with the design of new system. It involves designing of various things such as output design, input design, files design, processing and general program design etc. This state consists of logical design and physical design of the system.
a. Logical Design: Theoretically designing of the system is called logical design. The system could be designed on the basis of the requirements.
b. Physical Design: The conversion of logical design into designing tools and techniques is called physical design. It is more detail and complex jobs describing the solution of the problem. It uses algorithms, flowcharts, pseudo codes, decision table, decision tree, E-R diagram, Data flow diagram etc.
System Design Tools:
The tools which are used to design the system in known as system design tools. They are used during system analysis and design phase of the system development
a. Algorithm: An algorithm is defined as the finite sequences of instructions for solving a problem
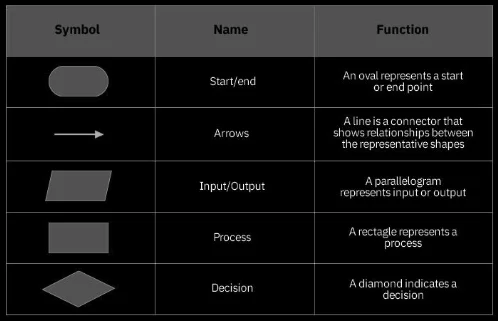
b. Flowchart: A flowchart is the pictorial representation of an algorithm which is classified into two types’ system flowchart and program flowchart. The different symbols used in system flowchart are defined below:
I) System flowchart:
System flowchart describes the internal architecture of a system that describes how data are moved inside the internal components of a system.
II) Program flowchart:
Program flowchart describes to solve the application types of real world problem.
c. DFD (Data flow diagram):
DFD is the logical diagram to describe the flow of data inside the components of system. It is easier to understand or grasp when being explained and most important to all, it is much more precise and less ambiguous than a narrative one. The main components are: process, data store, data flow, external entities.

d. Context Diagram:
It is combination of many other DFD. It is the highest level of DFD. It contains only one process, representing the entire system, the process is given the symbol circle. The external entities are denoted by rectangle. The flow of data is described by arrow.

e. ER (Entity Relationship) diagram:
The E-R diagram is an overall logical structure of a database that can be expressed graphically. It was developed to facilitated database design and the simplicity and pictorial clarity of this diagramming technique have done great help in the designing part of database. The main components are attributes, entities and relationship.
The diagrammatic representation of entities attributes and their relationship is described by E-R diagram.

E-R diagram

f. Case diagram:
Computer aided software engineering tool is automatic computer based program that helps for software engineering and SDLC process. It is very fast and effective tools for the development of big scale software. It helps in analysis, design, implementation, testing and maintenance.
g. UML:
Unified Modeling Language is a standardized general purpose modeling language in the field of object-oriented software engineering. The standard is managed, and was created by, the object management group. UML includes a set of graphic notation techniques to create visual models of object-oriented software.
h. Decision Table:
A table allows us to identify the exact course of actions for given conditions in tabular form. Decision table is a tabular representation of the logic of a decision, which specifies the possible conditions for the decision and the resulting actions.
Parts of Decision Table.

i. Decision Tree:
Decision tree is also a technique to represent condition and actions in a diagrammatic form in computer. A decision tree allows us to identify the exact course of actions for given conditions in tree structures.
j. Pseudo Code:
It is a kind algorithm for solving a problem and the instructions of pseudo code are written by using English phrase and mathematical expressions.
Programmers begin to develop the program by using a suitable High Level Language. In System developments following processes are done.
It is an investigation conducted to provide stakeholders with information about the quality of the product or service under test. System testing also provides an objective, independent view of the software to allow the business to appreciate and understand the risks of software implementation.
Implementation involves testing the installed system, converting from the old system to the new one and training the users. This phase consists of implementation of the system into a production environment, and resolution of the problem identified in testing phase.
Types of Implementation:
It begins after the system is implemented. Like any system, there is an ageing process that requires periodic maintenance of hardware and software. The content of the review will include objectives met, cost, performance, standards and recommendation.
Types of Maintenance
During software development or system development for organizations, a common process framework is established, defining a small number of framework activities that are applicable to all software projects, regardless of their size complexity. For a better paradigm of a software process, several models are designed and implemented. It is the choice of system analyst which model is used to achieve the goal. The different models are:
Waterfall model is a systematic and sequential model to develop software that begins with requirements analysis to operation and maintenance. It describes a development method that is linear and sequential. It is an oldest type of model for software engineering. The fundamental processes of waterfall model are as follows:

Advantages:
Disadvantages:
It is the iterative process of system development which is more appropriate for developing new system where there is no clear idea of requirements, inputs and outputs. These systems are then continuously modified until the user is satisfied.

Advantages:
Disadvantages:
In this model, process is represented as a spiral rather than as a sequence of activities with backtracking. It is a software development process combining the elements of both waterfall and prototyping model. The spiral model is intended for large, expensive and complicated projects. This is the most realistic model because it uses multidimensional approach for software development. The activities in SDLC are organized in a spiral structure that has many cycles which starts from the center of the spiral and goes out as it program and becomes matured. Each of the complete spiral segment is divided into four different attributes knows as:

Advantages:
Disadvantages:
It is a software development method based on iterative and incremental development in which requirement and solutions evolve through collaboration between self-organizing, cross functional teams.

Documentation is the process of collecting, organizing, storing and maintaining a complete record of system and other documents used or prepared during the different phases of the life cycle of the system. It consists of the detail description about software requirements specification, feasibility report, and software designing report, description about input-output and processing mechanism, source code, comments, manuals, guides and effective help desk.
Types of Documentation
There are two approaches of program development. They are Procedure Oriented Programming and Object-Oriented Programming. Procedure Oriented Programming is a conventional method of programming and the Object-Oriented Programming is a modern or latest programming method.
It is a conventional or old method of programming, in which the program is written into many small parts and combined together. In this approach, the functions are created and the data is not very crucial. Variables are created for the data handling and they are treated as the global and local variables. Creation of the variables inside of the sub programs is known as local variable and the creation of the variables in the main module is called the global variable. Global variables can be accessed from any modules but the local variables can be accessed only within the local modules. The alteration of data is very high.
The characteristics or features are as follow:
a) A large program is broken down into small programs or procedures.
b) It focuses on the functions rather than the data.
c) Variables are created as local and global.
d) The possibility of data alteration is very high, which is the main disadvantage of this approach.
e) It follows top down method.
It is a modern approach of programming. It is highly known as OOP in short form. In this method, all the real world entities are treated as the objects and objects are collected in a class. Even the classes are controlled by the Superclass. And by the inheritance feature, the changes on the superclass are easily passed to its subclasses. Similarly, it was developed to overcome procedure oriented programming method and the data is given high priority rather than the functions. Data can be hidden, so that the possibility of data alteration is very less.
a) Emphasis is given to the data.
b) Program are divided into multiple objects.
c) Functions and data are tied together in a single unit.
d) Data can be hidden to prevent accidental alteration.
e) It follows the bottom up approach.
| Procedure Oriented | Object Oriented |
| 1. Emphasis is given to procedures. | 1. Emphasis is given to data. |
| 2. Programs are divided into multiple modules. | 2. Programs are divided into multiple objects. |
| 3. It follows top-down method. | 3. It follows bottom-up method. |
| 4. Generally data cannot be hidden. | 4. Data can be hidden. |
| 5. It does not model the real world perfectly. | 5. It models the real world perfectly. |
| 6. Maintenance is difficult. | 6. Maintenance is easy. |
| 7. Code reusability is difficult. | 7. Code reusability is easy. |
| 8. Examples: FORTRAN, COBOL, Pascal, C, etc. | 8. Examples: C++, JAVA, Smalltalk, etc. |
a) Object
All the entities of a program used in OOP method are called objects. Here entities represent a group of people, teachers, students, books, cars, etc. Each entity or object does have an attribute called characteristics and the behavior or functions. For example, a car can be an object. The colour like blue, black, size, weight, etc. are the attributes or the characteristics, which distinguishes to it with other objects and move, turn, etc. can be the functions.
b) Class
Class is a user defined data type in OOP, which defines the data types for all the objects, which run under it. Or it collects the objects of its similar data types. For example, a class vehicle can have the objects like car, bus, truck, etc. Similarly a class school can have students, teachers, staff, etc.
c) Abstraction
It is a feature of hiding internal detail of any object. It provides only the interface to the user, which makes them easy to use but does not show the details of that object, how that works and how that is made. Due to this feature, OOP has become very secure platform for its data from being accidental alteration.
d) Encapsulation
It is a process of combining the data and functions together. OOP gives more emphasis on the data rather than the functions or procedures. Many functions can use the same data but the instruction given to the function to use any particular data and combining them together is the encapsulation. Due to its unrelated functions cannot use unnecessary data in the program.
e) Inheritance
Inheritance is the process of creating new classes based on the existing class. The new classes require the features of the main class called the Super class and it is provided through the feature called Inheritance. By the Inheritance feature Super class can coordinate with its subclasses. It models the real world. It allows the extension and reuse of existing code without having to rewrite for the new created classes.
f) Polymorphism
It is a feature of OOP, which refers to the way of operating the same operator in different ways and different method or purpose. Operator overloading and the operation overloading are the examples or Polymorphism. For example ‘+’ operator can be used for arithmetic operation and string concatenation both. This facility or feature is an example of Polymorphism. It reduces the number or keywords or operators.
Advantages:
a) Code repetition is reduced by the various techniques like inheritance.
b) Data is more secure due to the data hiding feature called abstraction.
c) Existing classes can serve as library class for further enhancements.
d) Division of a program into multiple objects makes the software development easier. e) Software complexity is less.
f) Upgrading and maintenance of software is easy.
g) It perfectly models the real world system.
h) Code reusability is much easier than the conventional programming system.
Disadvantages:
a) Compiler and runtime overhead is high.
b) Software developer should analyze the problem in object oriented way.
c) Requires the mastery in software engineering and programming methodology.
d) Useful only for the large and complex projects.
Application of OOP
C is a high level language because no need for any architecture knowledge in normal English form. C is a compiler because it can translate the whole program at a time so we can call compiler. C is structured programming language. It is called also procedural oriented programming language, function oriented language, module programming language. It is simple, reliable and easy to use.
C is a computer language and a programming tool which has grown popular because programmers preferred it. It is a tricky language but a masterful one.
The C programming languages has the following features:
Advantage of C language:
⮚ It is machine independent programming language.
⮚ It is easy to learn and implement C language.
⮚ It can be implemented from mobile device to mainframe computers.
⮚ It is the mother of all modern programming language.
Disadvantage of C Language:
⮚ There is no runtime checking.
⮚ It has poor error detection systems.
⮚ On large programs, it is hard to fix errors.
⮚ It does not support modern programming methodologies oriented programming language.
The compiler of C has a preprocessor built into it. Lines that begin with # are called pre-processor directives. Each C program must start with proper header files (i.e.<stdio.h>) starting with ‘#’, sign, ‘include’ and a header file name enclosed within triangle brackets.
A file that is defined to be included at the beginning of a program in C language that contains the definitions of data types and declarations of variables used by the functions in the program is called header file.
Some of the frequent used header files are explain below:
| S.N. | Header File | Description | Main Functions |
| 1. | stdio.h | Standard input and output | fpen(), fclose(), rename(), gets(), puts(), getchar(), scanf(), printf() etc. |
| 2. | conio.h | Old MS-DOS compiler header file, used for console input & output. | getch(), getche() |
| 3. | math.h | Mathematical calculation in C program. | sin(x), cos(x), log(x), pow(x,2), sqrt(x), cbrt(x), ceil(x), floor(x) etc. |
| 4. | complex.h | Complex arithmetic | cpow(x,p), csqrt(x), ctan(x), ctanh(x), cabs(x) |
| 5. | string.h | String / Words manipulation function | strlen(y), strcpy(z,y), strcmp(z,y), strcat(z,y), strupr(y), strlwr(y) etc. |
| 6. | ctype.h | Character manipulation type header file | toupper(y), tolower(y), isupr(y), isspace(),
isalnu(y), toascii(y) etc. |
| 7. | stdlib.h | General purpose standard library. | rand(), malloc(), calloc(), abort(), exit() abs(), free() etc. |

A group of alphabetic, numeric and other characters that have some relationship with C programming language and recognized by compiler is called Character set. A character set can also contain additional characters with other code values.
The keywords, identifiers and other variables are constructed by using character set. The character set consists of following elements.

Identifiers:- Identifiers can be defined as the name of the variables, functions, arrays, structures etc created by the programmer. They are the fundamentals requirement of any language. The identifiers are defined according to the following rules:
⮚ Identifiers consists letters and digits.
⮚ First character must be an alphabet or underscore.
⮚ Uppercase and lowercase are allowed but not same, i.e. Text not same as text.
⮚ Only one special character underscores (_) will used.
For example, int a_b; Where a and _b are valid identifiers.
Keywords:-Keywords are the reserved words which have standard, predefined meaning in C language. Keywords cannot be used as names for the variables or other user defined program elements. There are 32 keywords available in C.
Common examples are as follows.

Tokens:
In a C source code, the basic element recognized by the compiler is known as tokens. A token is source program text that the compiler does not break down into components elements.
⮚ The keywords like int, float, if, for etc.
⮚ Identifiers like main, printf, void etc.
⮚ Constants like a,b,c etc.
⮚ String literals like name, address, phone etc.,and
⮚ Operators like &&, ! etc.
⮚ Punctuation characters such as [ , ] , { , } , ( , ) , ; , : are also tokens.
Data types:
It is the set of keywords to declare variables. A set of data that specifies the possible range of values in a program and stored in memory are called data types. Data types are used to define variables before use it.
Types of data types in C
1) Primary data types
2) Secondary data types
Primary Data Types: The basic fundamental of data having unit feature on C programming is called Primary Data Type.
Example :
| Data Type | Type | Memory Require |
Format Specifies |
| Char | Character | 1 byte | % C |
| Int | Integer | 4/2 byte | %d |
| Float | Floating point number | 4 byte | %f |
| Long | Floating number | 4 byte | %ld |
| Double | Large floating point number | 8 byte | %lf |
| long double | Very large floating number | 12 byte | %lf |
Variable are simply names that can change the value while executing a program. It allocates memory space inside a memory of computer. A variable can have only one value assigned to it in every time of execution of the program. Its value can change in different executions.
✔ They must always begin with a letter, although some systems permit underscore as the first character.
✔ White space is not allowed.
✔ A variable should not be a keyword.
✔ It should not contain any special characters.
Types of variable
Constant variable:
A constant is fixed entity. It does not change its value during the entire program execution. Constants can be classified as:
The input and output data are formatted by specific pattern. These Patterns are generated by using specific tokens in C programs. These tokens used to format data are called specifier. Most of the specifier used by printf and scanf functions. Types of mostly used specifier are explained below.
❖ Escape Sequence: They are a type of specifier. These non printable characters are used to format text on the output screen. These escape sequence character are place after backslash \.
| Escape sequence | Name | Meaning |
| \’ | Single quote | It prints ‘ in output |
| \” | Double quote | It prints ” in output |
| \n | New line | It creates new line in output display |
| \t | Tab | It creates tab or 8 spaces in place of \t |
❖ Format Specifier: The output and input data are display and receive in specific pattern. Format specifier uses the token % and character(s) after it. It is used to format for all types of data i.e. integer, float, character and string.
| Format Specifier | Used by scanf() function |
| %d , % i | Signed integer + or – number o to 9 |
| %f | Scans floating point numbers. |
| %s | String, Collection of character i.e. word |
| %c | Character, one single key stroke. |
An operator is a symbol that operates on a certain data type. The operator generally remains between the two operands. An expression is a combination of variables, constants, and operators written according to the syntax of the language. The data items that operators act upon are called operands.
Types of operator:
The arithmetic operators perform arithmetic operations and can be classified into unary and binary arithmetic operations. The arithmetic operators can operate on any built-in data type. A list of arithmetic operators and their meanings are given below:
| Operator | Meaning |
| +
– * / % |
additional or unary plus
subtraction or unary minus multiplication division modulo division (returns remainder after division) |
The relational operators help to compare two similar quantities and depending on their relation, take some decisions. If the condition is true, it evaluates to an integer 1 and zero if the condition is false. The basic types of relational operator are:
| Operator | Meaning |
| <
> <= >= == != |
less than
greater than less than or equal to greater than or equal to equal to not equal to |
The logical operators are used to give logical value either true or false. They compare or evaluate logical and relational expressions. There are three logical operators.
| Operator | Meaning | Examples |
| && | Logical AND | (a>b) && (a>c) |
| || | Logical OR | (a>b) || (a>c) |
| ! | Logical NOT | !(a==b) |
The increment and decrement operators are very commonly used in C language. The increment operators and decrement operators are extensively used in the loops using structures such as for, while, do, etc. The syntax of the operators is given below:
| ++<variable name>
–<variable name> <variable name>++ <variable name)– |
Pre increment
Pre decrement Post increment Post decrement |
The pre increment operator increases the value of the variable by 1 and then the processing does whereas post increment first processes and increase the value of it by 1.
A conditional operator is very rarely used. This can be carried out with the conditional operator (? : ) An expression that makes use of the conditional operator is called a conditional expression. This can replace the if-else statement. The syntax of conditional operator is:
Expression_1 ? expression_2: expression_3
During evaluating the conditional expression, expression_1 is evaluated at the first step. If expression_1 is true (nonzero), then expression_2 is evaluated and this becomes the value of the conditional expression.
The special functions that are well defined in C programming languages are called library functions such as printf(), scanf(),strlen(), sqrt(), tolower(), toupper(), getchar(), putchar() etc.
Control structures are those programming constructs which control the flow of program statements execution in a program. Types of Control Structure
i) Branching / Decision ( Selective Control Structure)
ii) Looping (Repetitive Control Structure)
iii) Jumping (Unconditional Control Structure)
It is mainly used for decision making. It is also called conditional statements. Selection is made on the basis of condition. We have options to go when the given condition is true or false. The flow of program statements execution is totally directed by the result obtained from checking condition. Types
a) Conditional Statements:
i. if statements:
It is used to execute an instruction or block of instructions only if a condition is fulfilled. Syntax,
if(condition)
{
Statements;
}
E.g. Write a program to read a number and find even or odd by using if().

Output:

ii. if else statements:
If the condition is true then the if() portion statements are evaluated otherwise else part of the statements are evaluated.
Syntax,
if( condition)
{
Block of statements;
}
else
{
Block of statements;
}
E.g. Write a program to input any two numbers and display the largest one.

Output:

iii. if() else if() statements
When we have two or more condition to be checked in a series we can use if else if statement. It is also known as multiple conditional statement or multipath conditional statement /if else ladder. Syntax,

e.g. Write a program to find the largest number among three input number .


Output:

iv. Nested if else statements
An entire if else statement written within the body of if part or else part of another if else statement is called nested if else statement. It is used when a condition is to be checked inside another condition at a time in the same program to make decision.
Syntax,

E.g. Write a program that reads marks of five subject and calculate total mark and percentage. Also awards the division on the basis of following criteria.
Percentage division
p>=75 distinction
p>=60 and <75 first
p>=45 and <60 second
p>=35 and <45 third
otherwise failed


Output:

b) Switch case statements:
The switch statement can be used instead of multiple if() else conditional statements. The switch control statement is mainly used to generate menu based programs.
E.g. Write a program which reads any two integer values from the user and calculates sum, difference and product using switch case statements.


Output:

The looping statement is also called repetitive or iterative control structure. Looping statements are the conditional control flow statements that repeats a certain portion of the program either a specified number of times or until a particular condition is satisfied or true.
Types of loop
i) For Loop
ii) While Loop
ii) Do while Loop
i. For Loop:-
The execution of for loop until the condition is true. The for loop is a entry control loop because it checks the condition at entry point.
Syntax,



2. Write a program to display even numbers from 1 to 20 and display their sum also.

Output:

3. Write a program to find out sum of the cubes of first 10 numbers.

Output:

Nested for loop:
When for loop is declared inside another for loop is called nested for loop. The life of the inner for loop is depending over the outer for loop. If the outer for loop condition is true then inner for loop is evaluated. And will executes all the statements until condition is true if the inner for loop to be false then the outer for loop condition is reevaluated and so on.
For example:

10 20 30 40 50
10 20 30 40 50
10 20 30 40 50
10 20 30 40 50
10 20 30 40 50
Program:

Output:

2. Write a program to display following output:
55555
4444
333
22
1
Program:

Output:

While Loop:-
The while loop is also a entry control loop. While loop first checks whether the initial condition is true or false and finding it to be true, it will enter the loop and execute the statement.
Syntax,

1. Write a program to print even number from 1 to 100.

Output:

Do while loop:-
This loop is an exit control loop. This loop runs at least the once even though the termination condition is set to false. This loop test the condition at exit point hence it is called exit control loop. The syntax of the loop is similar to while loop.

1. Write a program to display odd numbers from 100 to 1.

Output:

2. Write a program to read the employee name, address for the N employee and display by using while loops.

Output:

| S.N. | While loop | S.N. | Do while loop |
| 1 | It is an entry controlled loop. | 1 | It is an exit controlled loop. |
| 2 | Testing starting in top | 2 | Testing started at the bottom. |
| 3 | It has keyword while | 3 | It has the keywords do and while. |
| 4 | If the first condition is true then the statement is executed otherwise no. | 4 | But in case at least one time executed statement if the condition is false. |
| 5 | Loop is not terminated with a semicolon. | 5 | Loop is terminated with a semicolon. |
| 6 | Syntax,
while (expression) { //statements } |
6 | Syntax,
do { //statements } while (expression); |
1) break statements:
The break statement is used to terminate a loop or to exit from a switch. it can be used within a for, while, do while switch statement.

Output:

2) The continue Statement :
It skips the remaining statements in the body a while, for or do ……while structure proceeds with the next iteration of the loop. The continue statement is used to bypass the execution of the further statements.

Output:

3) Go to statement:
The goto statement is used to send the pointer to the specified label. If the label is not defined then the goto statement will not work.

Output:

1. Write a program to input any value and display that value in reverse order.

Output:

2. Write a program to input a positive number and find its factorial number.


Output:

3. Write a program to display the Fibonacci series. 1 1 2 3 5 8 13 …………………n.


Output:

4.Write a program to read a number and to check the number is prime or not.


Output:

5.Write a program to find out even numbers from 1 to 100 and find their sum also.

Output:


6.Write a program to input a number and find out if the number is palindrome or not.


Output:

7.Write a program to input a positive number and find out the sum of its individual digits.


Output:

8.Write a program to input a number and check if it is an Armstrong number or not.


Output:

9.Write a program to display the multiplication table of a given number.

Output:

10.Write a program to display all prime numbers upto 1000.


Output:

11.Write a program to display all perfect square numbers from 100 to 500.

Output:

An array is a collection of data of the similar type all of which are referred by a single variable name. For example, instead of using 50 individual variables to store the names of 50 students, we can use an array to store the names of 50 students.
Advantage of arrays:
Disadvantages of arrays:
There are two types :
Syntax: type array_name[max. size];
Example int n[10];
int age[]= {18,12,19,20,16,16,17};
Syntax: type array_name[No.Rows] [No.Cols];
Example int n[10][5];
int matrix[3][3]= {{0,1,2},{3,4,5},{6,7,8}};
Program: Write a program to read 50 students’ marks and display them.

Output:

Program: Write a program to input 5 numbers with constant values initialization in array to display the sum.

Output:

Program: Write a program to input the age of 20 students and count the number of students having age in between 20 to 25.

Output:

Program: Write a program to find the largest number among ‘n’ numbers.

Output:

Program: Write a program to read a matrix, store it in an array and display it.


Output:

Program: Write a program to calculate the average age of 10 students.


Output:

Program: Write a program to accept the age of 10 different employees and count the no. of employees.
i) Whose age is more than or equal to 60
ii) Whose age is less than 35


Output:

Program: Write a program to store N numbers in array and print out the sum with the entire array variable.

 Output:
Output:

Program: Write a program to accept 10 different numbers in array and sort in descending order.



Output:


Program: Write a program to store twelve numbers in a double dimensional array and print out the values in table with row wise addition.

Output:

Program: Write a program to enter elements for 2×2 matrix and display its transpose.


Output:

Program: Write a program to enter elements for 3×3 matrix and display its sum.



Output:

The strings are manipulated by specific string function. These are inbuilt functions and defined within string.h header file.
Syntax: strlen(string);
Program: Write a program to store string in array variable and find the length.
Output:

2. strrev( ): It helps to reverse the character of the string.
Syntax: strrev(string);
3. strupr( ): It converts lowercase letters in string to uppercase.
Syntax: strupr(string);
4. strlwr( ): It converts uppercase letters in string to lowercase.
Syntax: strlwr(string);
5. strcpy( ): It is used to copy the content of one string to another.
Syntax: strcpy(target,source);
6. strcat( ): It is used to concatenate source string to the target string.
Syntax: strcat(target,source); or strcat(source,target);
7. strcmp( ): It compares two strings on the following basis.
Syntax: strcmp(string1,string2);
Program: Write a program to show use of trcpy,strrev,strupr and strlwr.



Output:

Program: Write a program to read two strings in an array and concatenate strings.

Output:

Program: Write a program to read two strings in an array and compare two strings and check that string is palindrome or not.


Output:

Functions are the building block of statements, which take some data, manipulate them and can return a value. Bug free functions can be used repeatedly from other parts of the program. There are two types of functions:
2. User Defined functions (Defined by user according to need): users can create their own function for performing this type of function called user defined function.
Syntax of user defined functions;


 Output:
Output:

2. Write a program to calculate the area of a rectangle using function.

 Output:
Output:

Advantage:
Program: Write a program to find out the area of a circle through a given radius as an argument using a function.


Output:

Program: Write a program in C to create a function to pass two numbers as an argument and to return a sum to the calling function.

Output:

Program: Write a program to find out the sum and square of two input number without passing arguments function.

 Output:
Output:

The function which performs recursion is called a recursive function. Recursion is a process by which a function calls itself repeatedly until some specified condition has been satisfied.
The function which calls itself is known as recursive function and the concept of using recursive functions to repeat the execution of statements as per the requirement is known as recursion. The criteria for recursive functions are:
Program: Write a program to calculate factorials by using a recursion process.

Output:

Program: Write a program to read a number and make the sum of individual digits & print using recursion technique.

 Output:
Output:

Program: Write a program to calculate sum of n-natural numbers using recursion/recursive function.

Output:

There are two types of accessing a function.
1. Call by value: Only the values of arguments are the same to the function and any change made to the formal arguments does not change the actual arguments.
Program: Write a C program trying to exchange two values by using a call by value accessing function.

Output:

2. Call by reference: When we pass an address to a function the parameters receiving the address should be pointers. The process of calling a function by using a pointer to pass the address of the variable is known as call by reference.
Program: Write a C program to exchange two values by using call by reference accessing function.

Output:

Structure:
Structure is a collection of variables under a single name. As an example, if we want to store data with multiple data types like roll number, student name, address, phone number and class of a student then C supports a structure which allows us to wrap one or more variables with different data types. Each variable in a structure is called a structure member. To define a structure, we use the struct keyword. Syntax;

We can also declare a structure ,

We can also declare array of variables at a time of declaring a structure as:

Union:
Unions like structure contain members whose individual data types may differ from one another. However the members that compose a union all share the same storage area within the computer memory where as each member within a structure is assigned its own unique storage area. Syntax;
Union union_name
{
Union_member (s);
}
| S.N. | Structure | S.N. | Union |
| 1. | Structure is designed by using the ‘struct’ keyword. | 1. | Union is designed by using ‘union’ keyword. |
| 2. | Syntax: struct structure_name
{ Data_type member1; Data_type member1; } |
2. | Syntax: union union_name
{ Data_type member1; Data_type member1; } |
| 3. | All the members of the structure variable can be processed at a given time. | 3. | Only one member of the union variable can be processed at a time because only one member of the union variable can be active at a time. |
| 4. | We use structure variables if memory is large and have to store values of all of the variables. | 4. | We use union variables if memory is less and have to store one variable in one of the declared variables or members. |
| 5. | Structures are broadly used in
programming. |
5. | Unions are not used broadly as much as structures. |
| 6. | Structure declaration takes a large amount of spaces to store data and values. | 6. | Union declaration shares the same area of memory to save storage space. |
Example 1: Write a C program to read different structure variables and display them.


Output:

Program: Write a program to input the employee name and their basic salary of n employees and display the record in proper format.

 Output:
Output:


Program: Write a program that reads different names and addresses into the computer and rearrange the names into alphabetical order using the structure variables.



Output:


A pointer is a variable that points to a memory location where data is stored. Each memory cell in the computer has an address which can be used to access its location. A pointer variable points to a memory location rather than a value.
– We can access and change the contents of the memory location.
– A pointer variable contains the memory location of another variable.
– The asterisk tells the compiler that you are creating a pointer variable.
The pointer declaration syntax is as shown below.
Pointer_type *pointer_variable_name;
For e.g. int *p;
Address (&) and indirection (*) operator
The address (&) operator and immediately preceding variable returns the address of the variable associated with it. Hence, the address of (&) operator returns the address of memory location in which the variable is stored.
The indirection (*) operator is used to extract value from the memory location stored in the particular memory location whose address is stored in a pointer variable.
The syntax of declaring address operator to pointer variable is as follows.
Pointer_variable = &variable_name;
For Example;
int *ptr, num=25;
ptr = #
Program: Write a complete program to display address and value of the pointer variable.

Output:

Pointer to Arithmetic

Output:

Write a C program to increment a pointer.

Output:

Program: Write a program to pass pointer variables to function sum them and display after returning it.

Output:

Program: Write a C program to assign an array, place these arrays in a pointer variable and display array value along with its address.

Output:

Program: Write a program to demonstrate the use of pointer to pointers:

Output:

Advantage of Pointer
Data file requires that information be written and stored on the memory device in the form of a data file. Thus, data file access and alter that information whenever information in C.

Sequential Access File:
The sequential access files allow reading the data from the file in one after another i.e. in sequence. There is no predefined order for accessing data file. All the processes are declare and assigned by the compiler during run time of the program.
Random Access File:
The random access files allow reading data from any location in the file. Sometimes, we need to read data file from reverse, middle and from specific location. To achieve this, C defines a set of functions to manipulate the position of the file. The inbuilt function fseek( ), lseek( ), rewind( ) and ftell( ) are the some of the common examples of random access files.
Opening, Reading, Writing and Appending on/from Data File:
Once the file pointer has been declared, the next step is to open file. There is an inbuilt function to open a file. The function fopen( ) is used to create a steam for use and links of new open file. This function return a file pointer and takes two parameter one for name of file and other for mode for the file. The syntax is as follows;
FILE *f;
f = fopen (“file_name.extension”, “mode_of_open”);
The modes of the data file are as follows:
| S.N. | Mode | Description |
| 1 | “r” / “rt” | It opens a text file to read only mode. |
| 2 | “w” / “wt” | It creates a text file to write only mode. |
| 3 | “a” / “at” | It appends text to already data containing file. |
| 4 | “r+t” | It opens a text file for read and write mode. |
| 5 | “w+t” | It creates a text file for read and write mode. |
| 6 | “a+t” | It opens or creates a text file and read mode. |
| 7 | “rb” | It opens a binary file for read only mode. |
| 8 | “wb” | It creates a binary file for write only mode. |
| 9 | “ab” | It opens or create a binary file for append mode. |
| 10 | “r+b” | It opens a binary file for read and write mode. |
| 11 | “w+b” | It creates a binary file for read and write mode. |
| 12 | “a+b” | It opens or creates a binary file for append mode. |
Functions;
Opening a data file
Syntax:
FILE *fptr
fptr = fopen (“filename” , ”mode”)
Where, File name can be “library.txt”, “student.dat” ..etc
Mode:
“w” to write/store data in a data file.
“r” to display/read/retrieve/access data from a datafile.
“a” to add/append data in existing datafile.
Store/write data
Syntax:
fprintf(fptr , ”format specifiers” ,variables);
Eg; suppose if we want to store name, disease, age and bed number of a patient then, it is written as
fprintf(fptr , ”%s %s %d %d”, n, d, a, b);
Where, variable are initialized as:
char n[10], d[10];
int a, b;
Program example
1) Create a datafile “patient.txt” and store name, disease, age and bed number of a patient.

Output:

[Note: This program will store only a single record. To store multiple records we have to use a loop as following programs.]
2) Create a datafile “student.txt” and store name, class and marks obtained in 3 different subject for few students/n-students.

Output:

3) Create a datafile “student.txt” and store name, class and marks obtained in 3 different subject until user press “y” / as per user requirement.


Output:

1) A datafile “student.txt” contains name, class and marks obtained in 3 different subjects of a few students. Write a C program to add 200 more records.

Output:
After 200 iterations, the program will stop and close the file “student.txt”. The file will contain the entered student records, each on a separate line, formatted as:

You can verify the contents of the “student.txt” file after running the program to see the recorded student information.
2) A datafile “student.txt” contains name, class and marks obtained in 3 different subjects of a few students. Write a C program to add more records until the user presses “y” / as per user requirement.

Output:

After the user enters the data, the program writes it to the file “student.txt”.
Syntax:
fscanf(fptr , ”format specifiers” ,variables);
Eg; Suppose if we want to display/read name, disease, age and bed number of a patient from data file then, it is written as
fscanf(fptr , ”%s %s %d %d”, n, d, &a, &b);
Where, variable are initialized as:
char n[10], d[10];
int a,b;
EOF: End of file

Output:

2) A datafile “student.txt” contains name, class and marks obtained in 3 different subjects of a few students. Write a C program to read and display only records whose name is Ram.


3) A datafile “student.txt” contains name, class and marks obtained in 3 different subjects of a few students. Write a C program to read and display only records who pass in all subjects.

4) A datafile “student.txt” contains name, class and marks obtained in 3 different subjects of a few students. Write a C program to read and display only records who fail in any one subject.

5) A datafile “student.txt” contains name, class and marks obtained in 3 different subjects of a few students. Write a C program to read and display only name and percentage of all students.

6) A datafile “student.txt” contains name, class and marks obtained in 3 different subjects of a few students. Write a C program to read and display only records of all students who secure distinction.


Program: Write a program to read a line and store it in a data file and display the contents.


Output:

Program: Write a C program to read N students, record, store them in data file and display the content in appropriate format by using fprintf and fscanf function.


Output:

Program: Write a program using C language that reads successive records from the new data file and display each record on the screen in an appropriate format.


Output:


Program: Write a C program to read sentences until the enter key is pressed. Put every word in the data file by using the fputs( ) fucnction and display the content of the file by using fgets( ) function.



Output:

Program: Write a C program to read ages of N students, store them in age.txt file and find out the average age after reading from the data file.



Output:

Program: Write C program to read already created data file student.txt and display its contents if it opens otherwise print message “The file ……does not exists”.

Output:

| Fwrite | S.N. | fprintf |
| Binary format writing | 1. | No binary format. |
| Size of data. | 2. | Size of data is not fix |
| Number of records. | 3. | No number of records. |
| We store the data in block form so not in format form. | 4. | Format string used to store the data in the format form. |
| Fixed block size. | 5. | No block size. |
| S.N. | Structure | S.N. | Pointer |
| 1. | Structure is use to store the difference type of data member like as char, int, float etc. | 1. | Where is pointer is use to store the address of another location (variable). |
| 2. | Structure is use to maintain the records. | 2. | Whereas pointer is use to create link list. |
| 3. | Structure can’t be use to access the hardware. | 3. | Pointer can be use to access the hardware. |
| 4. | Structure can’t be use to create memory run time. | 4. | But pointer are use to create the memory runtime. |
| 5. | Structure can be declared as pointer variable. | 5. | Pointer can be declared inside the structure. |
| S.N. | Break Keywords (Statement) | S.N. | Continue Keywords (Statement) |
| 1. | The break statement is use to terminate the loop unconditionally. | 1. | The continue statement is used return the pointer at the beginning of the loop. |
| 2. | The break statement can also be use inside the switch statement. | 2. | But the continue can be use inside the switch statement. |
| 3. | The break statement is use to terminate the loop. | 3. | The continue statement is use to repeat set of statements. |
| 4. | Example
void main( ) { int i; for (i=1; i<=10; i++) { If (i==5) { break; } printf(“%d”,i); } } Output= 1,2,3,4. |
4. | Example
void main( ) { int num; for (num=1; num!=10; num+1) { If(num==7) { continue; } printf(“%d”,num); } } Output= 1,2,3,4,5,6,8,9. |
| S.N. | Array | S.N. | Pointer |
| 1. | Array is create continue memory location with same type. | 1. | Pointer creates only one block of memory but access all memory of another variable. |
| 2. | Array takes huge of memory. | 2. | Pointer takes less and less memory. |
| 3. | Array is to be fixed at the time of declaration. | 3. | Whereas pointer size can be change at the run time. |
| 4. | In array we can free the memory run time. | 4. | But using pointer the dynamic allocated memory can be make free at run time. |
| 5. | If we allocated huge sized of array and we get few information then unnecessary memory will be occupied. | 5. | But this problem can resolved by using the pointer. |
| 6. | Using array technique to accessing the array elements is more different comparison to pointer. | 6. | It is easier than array. |
Web Technology is the tools and techniques which enables two or more computing devices to communicate over a network i.e. Internet.
Web Technology consist of two words, the web refers to the World Wide Web.
WWW is the cyber space containing webpages, documents, and any other resources which are identified and located with the help of their URLs.
Technology refers to the tools and techniques that makes these resources available on the Web such as, web browsers to view content of web, Programming languages and frameworks for the development of websites, Database to store data at back end, protocols for communicating on the web, multimedia elements etc.
It is the process of designing and developing website which are hosted through internet or intranet. The process of developing web can range from developing static page to a complex such as web based application social media sites, E-commerce.
Web development includes web design, web content development, client side scripting, server side scripting, web engineering etc. Since, web development consists of several interrelated task which can be accomplish by different types of developer who focuses on different aspect of web creation.

Scripting Language:
A scripting language is a programming language designed for integrating and communicating with other programming language. It is used in server side as well as client side. Some of the most widely used scripting language are JavaScript, VBScript, PHP, Perl, Python, Ruby etc.
JavaScript is a scripting language. A scripting language is a lightweight programming language. JavaScript code can be inserted into any HTML page, and it can be executed by all types of web browsers.
JavaScript is used to make web pages interactive. It runs on your visitor’s computer and doesn’t require constant downloads from your website. JavaScript and Java are completely different language, both in concept and design.
Unlike HTML, JavaScript is case sensitive-therefore watch your capitalization closely when you write JavaScript statements, create or call variables, objects and functions.
Application Areas of Scripting Language
⮚ Dynamic web applications.
⮚ Game application and Multimedia.
⮚ Scripting like Ruby and Python are used in statistics and research.
⮚ To automate the process.
⮚ Used to create plugins and extensions for existing applications.

Some of the popular Language are:

| S.N. | Scripting Language | S.N. | Programming Language |
| 1. | Scripting language are platform-specific. | 1. | Programming language are platform independent. |
| 2. | Most of the scripting languages are interpreted. | 2. | Most of the programming language are complied. |
| 3. | Scripting language runs slower than programming language. | 3. | Programming languages runs faster than scripting language. |
| 4. | Developer has to write less code compared to programming language. | 4. | Developer has to write much code
compared to scripting language. |
| 5. | We cannot create standalone application with scripting language only. | 5. | We can create standalone application with programming language only. |
| 6. | Examples, JavaScript, VBScript, Python, Perl, ASP etc. | 6. | Examples, C, C++, Java etc. |
| 7. | Scripting languages run inside other programs. It is dependent on other programming language. | 7. | It is not dependent on other programs to run. It is independent. |
Client-side scripting is performed to generate a code that can run on the client side i.e (front end) browser without needing the server-side (back end) processing. Basically, client-side scripts are placed inside an HTML document.
The client-side scripting can be used to layout the content of the web. For example, when a user makes a request through web browser for a web page to the server, it just sent the HTML and CSS as plain text, and the browser interprets and renders the content of web in the client end (user).
Client-side scripting is designed to run as a scripting language which can be executed by web browser. Front end developer is someone who design and develop client side of a website. Generally he or she works in user interface (UI) of a website. Front end developer must be at least fluent in three different languages i.e. HTML, CSS, JavaScript whereas, there are several other libraries which can be used for front end development.
Advantages of Client Side Scripting:
Disadvantages of Client Side Scripting:
Server-side scripting also known as back-end runs on the server where the application is hosted. Server side is used to serve content depending upon the user request. Back end helps to create dynamic web based application that allows user to interact and communicate with the application. Back end language also helps to connect front end with database. So that, user can store and retrieve data as per the requirement. Back-end developer is responsible for server-side programming. Some of the popular server-side (back-end) scripting language are ASP, JavaScript (using SSJS (Server-side JavaScript e.g. node.js), Perl, PHP, Ruby, Python etc.
The client-side scripting emphasizes making the interface of the web application or website (UI) more appealing and functional. Whereas, server-side scripting emphasizes on data accessing methods, error handling and fast processing etc.
Advantages of Server Side Scripting:
Disadvantages of Server Side Scripting:
Note: Full-stack developer understand both Front end and back end development process. They can accomplish entire project. Full stack developer must have expertise in client site and server side Scripting language. Moreover, he/she has a great knowledge of integrating database with the application.
This section elaborates the fundamental differences between client-side and server-side scripts:
| S.N. | Server Side Scripting | S.N. | Client Side Scripting |
| 1. | The Server executes the server side scripting. | 1. | The client (web browser) executes the client side scripting. |
| 2. | It can be used to connect database on the web server. | 2. | It cannot be used to connect to the database on the web server. |
| 3. | Server side scripting response is slower. | 3. | Client side scripting response is faster. |
| 4. | Source code is not visible to the user so it is secure. | 4. | Source code is visible to user so it is relatively insecure. |
| 5. | Users can not block server side scripting. | 5. | Users can block client side scripting |
| 6. | Examples: PHP, ASP.NET, ASP, Ruby on rails, Python, Perl. | 6. | Examples: JavaScript, VBScript |
| 7. | It does not depend on client. Any server side technology can be used. | 7. | It depends on browser and version of the browser. |
The Internet is the global system of interconnected computer networks that uses the Internet protocol suite to communicate between networks and devices. It is a network of networks that consists of private, public, academic, business, and government networks of local to global scope, linked by a broad array of electronic, wireless, and optical networking technologies. The Internet carries a vast range of information resources and services, such as the inter-linked hypertext documents and applications of the World Wide Web, electronic mail, telephony, and file sharing.
Static Web pages are very simple. It is written in languages such as HTML, CSS, etc. Static websites are the websites that doesn’t change the content or layout dynamically with every request to the web server. Static websites display exactly the same information whenever anyone visits it. User sees the updated content of Static Website only when a web author manually updates them with a text editor or any web editing tool used for creating websites. Static web pages do not have to be simple plain text. They can feature multiple design and even videos.

Features of Static Websites:
❏ Static websites are the simplest kind of website that you can build.
❏ Every viewer will see the exactly same text, multimedia design or video every time he/she visits the website until you alter that page’s source code.
❏ Static websites are written with the help of HTML and CSS.
❏ The only form of interactively on a static website is hyperlink.
❏ Static website can be used for the information that doesn’t change substantially over months or even years.
❏ Static pages are easy and simple to understand, secure, less prone to technology errors and breakdown and easily visible by search engines.
❏ HTML was the first tool with which people had begun to create static web pages. Static websites provide flexibility.
❏ Lightweight.
❏ Static websites perform faster and well than dynamic ones.
Advantages of Static websites:
Disadvantages of Static Websites:
Dynamic websites are those websites that changes the content or layout with every request to the webserver. These websites have the capability of producing different content for different visitors from the same source code file. There are two kinds of dynamic web pages i.e. client side scripting and server side scripting. The client-side web pages changes according to your activity on the web page. On the server-side, web pages are changed whenever a web page is loaded.
Example: login & signup pages, application & submission forms, inquiry and shopping cart pages. A Typical Architecture of dynamic website

There are different languages used to create dynamic web pages like PHP, ASP, .NET and JSP.
Whenever a dynamic page loads in browser, it requests the database to give information depending upon user’s input. On receiving information from the database, the resulting web page is applied to the user after applying the styling codes.
Features of dynamic webpage:
❏ These websites are very flexible.
❏ In these websites the content can be quickly changed on the user’s computer without new page request to the web browser.
❏ In these websites the owner have the ability to simply update and add new content to the site.
❏ These websites are featured with content management system, e-commerce system and intranet or extranet facilities.
❏ Most of the dynamic web content, is assembled on the web using server-scripting languages.
Advantages of dynamic webpage:
Disadvantages of dynamic web pages:
Application of Dynamic Website:
➢ Online booking system:
➢ E-commerce website.
➢ Voting or polls,
➢ Forums
➢ E-newsletter.
JavaScript is a lightweight, interpreted programming language. It is designed for creating network-centric applications. It is complementary to and integrated with Java. JavaScript is very easy to implement because it is integrated with HTML. It is open and cross-platform.

This tutorial has been prepared for JavaScript beginners to help them understand the basic functionality of JavaScript to build dynamic web pages and web applications.
Features:
⮚ JavaScript is a lightweight, interpreted programming language.
⮚ Designed for creating network-centric applications.
⮚ Complementary to and integrated with Java.
⮚ Complementary to and integrated with HTML.
⮚ It is case sensitive language.
⮚ JavaScript is supportable in operating system.
⮚ It provides good control to the users over the web browsers.
Advantages of JavaScript:
Uses of JavaScript:
⮚ Client side validation
⮚ Dynamic drop down menus.
⮚ Displaying date and time.
⮚ Displaying pop-up windows and dialog boxes
⮚ Displaying clocks.
⮚ Event handling.
⮚ Developing Mobile applications
⮚ Creating web browser based games.
⮚ Building web servers
⮚ Adding interactivity to website.
JavaScript, also known as JS, is one of the scripting (client-side scripting) languages, that is usually used in web development to create modern and interactive web-pages. The term “script” is used to refer to the languages that are not standalone in nature and here it refers to JavaScript which run on the client machine.
In other words, we can say that the term scripting is used for languages that require the support of another language to get executed. For example, JavaScript programs cannot get executed without the help of HTML or without integrated into HTML code.

Output:

We can also define the JavaScript code in the <body> tags or body section.
Let’s understand through an example.

Let’s look at the example.

Output:

In this example, we will see how we can include an external JavaScript file in an HTML document. Let’s understand through a simple example.

Output:

Now let’s create separate JavaScript file = Hello.js

JavaScript statements are written within <script>…..</script>. The <script> tag alerts the browser program to start interpreting all the statements between these tags as a script. A simple syntax of your JavaScript will appear as follows:
Syntax:
<script>
block of Statements
</script>
Statements:
JavaScript statements are composed of Values, Operators, Expressions, Keywords, and Comments. The program consists of many statements. The statements are executed, one by one, in the same order as they are written. It is often called JavaScript code.
var area = l*b;
The JavaScript comments are meaningful way to deliver message. It is used to add information about the code, warnings or suggestions so that end user can easily interpret the code.
The JavaScript comment is ignored by the JavaScript engine i.e. embedded in the browser. There are two types of comments in JavaScript.
It is represented by double forward slashes (//). It can be used before and after the statement. Let’s see the example of single-line comment i.e. added before the statement.

Output:

Let’s see the example of single-line comment i.e. added after the statement.

Output:

It can be used to add single as well as multi line comments. So, it is more convenient. It is represented by forward slash with asterisk the asterisk with forward slash. For example:
/* your comment here */
It can be used before, after and middle of the statement.


Output:

JavaScript ignores spaces, tabs, and newlines that appear in JavaScript programs. To make a code readable and understandable, formatting and indenting the code by using several spaces, tabs, and newlines can be used freely in the program.
JavaScript is a case-sensitive language. The keywords, variables, functions names, and any other identifiers must always be typed with a consistent capitalization of letters. So the identifiers Time and TIME will convey different meanings in JavaScript.
JavaScript can “display” data in different ways: It defines the ways to display the output of a given code. The output can be display by using four different ways which are listed below:
Using document.write( ), the output can be displayed in browser page.

Output:

Innerhtml
Using innerHTML, the output can be displayed into the HTML element. The innerHTML property sets or returns the HTML content (innerHTML) of an element.

Output:

Using window.alert( ), the output can be displayed into an alert box. window.confirm() and window.prompt() are also other method to output into an alert box.

Output:

Using console.log( ), the output can be displayed into the browser console. To use console of web browser, right click in web browser and select inspect. The console will display.

Output:

Lists of all the reserved words in JavaScript are given in the following table. They cannot be used as JavaScript variables, functions, methods, loop labels, or any object names.

JavaScript provides different data types to hold different types of values. There are two types of data types in JavaScript.
JavaScript is a dynamic type language, means you don’t need to specify type of the variable because it is dynamically used by JavaScript engine. You need to use var here to specify the data type. It can hold any type of values such as numbers, strings etc. For example:
var a=40; //holding number
var b=”Rahul”; //holding string
There are five types of primitive data types in JavaScript. They are as follows:
| Data Type | Description |
| 1. String | represents sequence of characters e.g. var str=”hello”; |
| 2. Number | represents numeric values e.g. var a=100; |
| 3. Boolean | represents Boolean value either false or true |
| 4. Undefined | represents undefined value. E.g. var address=”Bharaptur” address= undefined |
| 5. Null | represents null i.e. no value at all. |
The non-primitive data types are as follows:
| Data Type | Description |
| 1. Object | represents instance through which we can access members |
| 2. Array | represents group of similar values |
| 3. RegExp | represents regular expression |
A JavaScript variable is simply a name of storage location. There are two types of variables in JavaScript: local variable and global variable.
There are some rules while declaring a JavaScript variable (also known as identifiers).
Correct JavaScript variables
Incorrect JavaScript variables
Example of JavaScript variable
Let’s see a simple example of JavaScript variable.

Output:

JavaScript operators are symbols that are used to perform operations on operands. For example:
var sum=10+20;
Here, + is the arithmetic operator and = is the assignment operator.
There are following types of operators in JavaScript.
Arithmetic operators are used to perform arithmetic operations on the operands. The following operators are known as JavaScript arithmetic operators.
| Operator | Description | Example |
| + | Addition | 10+20 = 30 |
| – | Subtraction | 20-10 = 10 |
| * | Multiplication | 10*20 = 200 |
| / | Division | 20/10 = 2 |
| % | Modulus (Remainder) | 20%10 = 0 |
| ++ | Increment | var a=10; a++; Now a = 11 |
| — | Decrement | var a=10; a–; Now a = 9 |
Example:

Output:

The JavaScript comparison operator compares the two operands. The comparison operators are as follows:
| Operator | Description | Example |
| == | Is equal to | 10==20 = false |
| != | Not equal to | 10!=20 = true |
| > | Greater than | 20>10 = true |
| >= | Greater than or equal to | 20>=10 = true |
| < | Less than | 20<10 = false |
| <= | Less than or equal to | 20<=10 = false |
Example:


The bitwise operators perform bitwise operations on operands. The bitwise operators are as follows:
| Operator | Description | Example |
| 1) & | Bitwise AND | (10==20 & 20==33) = false |
| 2) | | Bitwise OR | (10==20 | 20==33) = false |
| 3) ^ | Bitwise XOR | (10==20 ^ 20==33) = false |
| 4) ~ | Bitwise NOT | (~10) = -10 |
| 5) << | Bitwise Left Shift | (10<<2) = 40 |
| 6) >> | Bitwise Right Shift | (10>>2) = 2 |
| 7) >>> | Bitwise Right Shift with Zero | (10>>>2) = 2 |
The following operators are known as JavaScript logical operators.
| Operator | Description | Example |
| && | Logical AND | (10==20 && 20==33) = false |
| || | Logical OR | (10==20 || 20==33) = false |
| ! | Logical Not | !(10==20) = true |
The following operators are known as JavaScript assignment operators.
| Operator | Description | Example |
| = | Assign | 10+10 = 20 |
| += | Add and assign | var a=10; a+=20; Now a = 30 |
| -= | Subtract and assign | var a=20; a-=10; Now a = 10 |
| *= | Multiply and assign | var a=10; a*=20; Now a = 200 |
| /= | Divide and assign | var a=10; a/=2; Now a = 5 |
| %= | Modulus and assign | var a=10; a%=2; Now a = 0 |
The following operators are known as JavaScript special operators.
| Operator | Description |
| (?:) | Conditional Operator returns value based on the condition. It is like if-else. |
| , | Comma Operator allows multiple expressions to be evaluated as single statement. |
| Delete | Delete Operator deletes a property from the object. |
| In | In Operator checks if object has the given property |
| Instanceof | checks if the object is an instance of given type |
| new | creates an instance (object) |
| typeof | checks the type of object. |
| Void | it discards the expression’s return value. |
Bit operators work on 32 bits numbers.
Any numeric operand in the operation is converted into a 32 bit number. The result is converted back to a JavaScript number.
| Operator | Description | Example | Same as | Result | Decimal |
| & | AND | 5 & 1 | 0101 & 0001 | 0001 | 1 |
| | | OR | 5 | 1 | 0101 | 0001 | 0101 | 5 |
| ~ | NOT | ~ 5 | ~0101 | 1010 | 10 |
| ^ | XOR | 5 ^ 1 | 0101 ^ 0001 | 0100 | 4 |
| << | left shift | 5 << 1 | 0101 << 1 | 1010 | 10 |
| >> | right shift | 5 >> 1 | 0101 >> 1 | 0010 | 2 |
A JavaScript function is a block of code designed to perform a particular task. A function is a go of reusable code which can be called anywhere in your program. This eliminates the need of writing the same code again and again. It helps programmers in writing modular codes. Function allow a programmer to divide a big program into a number of small and manageable function.
Advantages of Using Function:
⮚ You can’t do anything in JavaScript without function.
⮚ Functions increases code reusability.
⮚ Function helps to structure the code properly.
⮚ Functions make code less complex.
⮚ Functions make code more readable and extendable.
⮚ Functions can be called anywhere in the program.
⮚ Functions helps program developers to write the modular codes.
⮚ Function also allows a programmer to divide a big program into a number of small and manageable functions.
Before we use a function, we need to define it. The most common way to define a function in JavaScript is by using the function keyword, followed by a unique function name, a list di parameters (that might be empty), and a statement block surrounded by curly braces.
Syntax:
<script type=”text/javascript”>
function function_name (parameter-list)
{
//statements
}
</script>
The code written inside a function does not execute unless it is called. To call a function somewhere later in the script, you would simply need to write the name of that function as shown in the following code.
Example 1:

Output:

Example 2:

Output:

A function can take multiple parameters separated by comma. The function parameters can have value of any data type.
Example:

The return statement is used to return a particular value from the function to the function caller. The function will stop executing when the return statement is called. The return statement should be the last statement in a function because the code after the return statement will be unreachable.
Example:

Output:

Above program is a simple example of using the return statement. Here, returning the result of the product of two numbers and returned the value to the function caller.
The variable res is the function caller; it calls the function fun() and passes two parameters as the arguments of the function.
The result will be store in the res variable. Final output 240 is the product of arguments 12 and 20.
Control Structures
The JavaScript if-else statement is used to execute the code whether condition is true or false. There are three forms of if statement in JavaScript.
It evaluates the content only if expression is true. The signature of JavaScript if statement is given below.
if(expression)
{
//content to be evaluated
}
Let’s see the simple example of if statement in JavaScript.

Output:

It evaluates the content whether condition is true of false. The syntax of JavaScript if-else statement is given below.
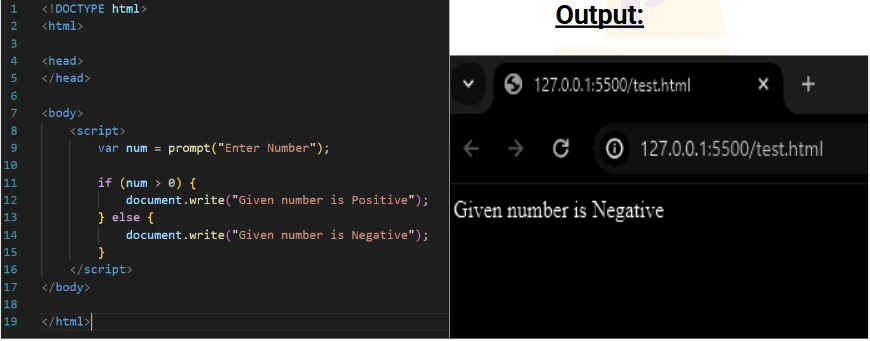
Let’s see the example of if-else statement in JavaScript to find out the even or odd number.

Output:

It evaluates the content only if expression is true from several expressions. The signature of JavaScript if else if statement is given below.
if(expression1)
{
//content to be evaluated if expression1 is true
}
else if(expression2)
{
//content to be evaluated if expression2 is true
}
else if(expression3)
{
//content to be evaluated if expression3 is true
}
else
{
//content to be evaluated if no expression is true
}
Let’s see the simple example of if else if statement in JavaScript.

Write a program to input a number and check that is positive, negative or not.

The JavaScript switch statement is used to execute one code from multiple expressions. It is just like else if statement that allow us to choose only one option among the many given options. But it is convenient than if..else..if because it can be used with numbers, characters etc.
The signature of JavaScript switch statement is given below.
switch(expression)
{
case value1:
code to be executed;
break;
case value2:
code to be executed;
break;
……
default:
code to be executed if above values are not matched; }
Let’s see the simple example of switch statement in JavaScript.


Output:

The processing of repeatedly executing the block of statements is called iteration or looping. Loops are used to repeat the execution of a block of code. The JavaScript loops are used to iterate the piece of code using for, while, do while. It makes the code compact. It is mostly used in array. There are four types of loops in JavaScript.
For loop is used to execute a set of statements for given number of times. The JavaScript for loop iterates the elements for the fixed number of times. It should be used if number of iteration is known. The syntax of for loop is given below.
for (initialization; condition; increment)
{
code to be executed
}
Let’s see the simple example of for loop in JavaScript.

Output:

The while loop is an entry controlled loop in which condition is checked before the execution of loop.
Syntax
while (condition)
{
// code block to be executed
}
Example, Write a program to display even number from 1 to 20.

Output:

The JavaScript do while loop iterates the elements for the infinite number of times like while loop. But, code is executed at least once whether condition is true or false. The syntax of do while loop is given below.
do
{
code to be executed
}while (condition);
Example:

Output:


Or,

Object is a non-primitive data type in JavaScript. Object is like any other variable but it is quite differ from variable. The variable can hold only one value but object can hold multiple values. The object holds multiple values in terms of properties and methods. Properties can hold values of primitive data types and methods are functions.
An object is defined simple way as like a variable. The object is defined with a unique object name and the curly brackets { } is used to include properties and methods. The variables within the object is known as properties and the function within the object is known as methods. The properties or method are written as name: value pairs. The name and value separated by a colon. The period ‘.’ is used to access value to object.
Syntax:
var object_name = { name: value1, name2: value2, nameN: valueN };
Example
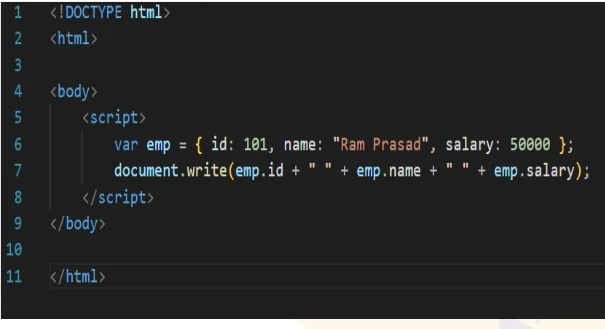
Output:

In the above example, object name is defined as emp and it has three properties id, name and salary. The value of object can be accessed easily using object name period and properties name.
There are 3 ways to create objects.
1) JavaScript Object by object literal
The syntax of creating object using object literal is given below:
object={property1:value1,property2:value2…..propertyN:valueN}
As you can see, property and value is separated by : (colon). Let’s see the simple example of creating object in JavaScript.


⮚ In the above example, method is defined as move. The method can be accessed easily using object name period and method name.
2) By creating instance of Object
The syntax of creating object directly is given below:
| var objectname=new Object(); |
Here, new keyword is used to create object. Let’s see the example of creating object directly.

Output:

3) By using an Object constructor
Here, you need to create function with arguments. Each argument value can be assigned in the current object by using this keyword.
The this keyword refers to the current object.
The example of creating object by object constructor is given below.

Output:

The document object represents the whole html document. When html document is loaded in the browser, it becomes a document object. It is the root element that represents the html document. It has properties and methods. By the help of document object, we can add dynamic content to our web page. As mentioned earlier, it is the object of window. So window.document is same as a document.
Let’s see the properties of document object that can be accessed and modified by the document object.

JavaScript gets all the power it needs to create dynamic HTML:
⮚ JavaScript can change all the HTML elements in the page
⮚ JavaScript can change all the HTML attributes in the page
⮚ JavaScript can change all the CSS styles on the page
⮚ JavaScript can remove existing HTML elements and attributes
⮚ JavaScript can add new HTML elements and attributes
⮚ JavaScript can react to all existing HTML events in the page
⮚ JavaScript can create new HTML events in the page
We can access and change the contents of document by its methods. The important methods of document object are as follows:
| Method | Description |
| write(“string”) | writes the given string on the document. |
| writeln(“string”) | writes the given string on the document with newline character at the end. |
| getElementById() | returns the element having the given id value. |
| getElementsByName() | returns all the elements having the given name value. |
| getElementsByTagName() | returns all the elements having the given tag name. |
| getElementsByClassName() | returns all the elements having the given class name. |
In this example, we are going to get the value of input text by user. Here, we are using document.form1.name.value to get the value of name field. Here, document is the root element that represents the html document. form1 is the name of the form. name is the attribute name of the input text. value is the property, that returns the value of the input text.
Let’s see the simple example of document object that prints name with welcome message.
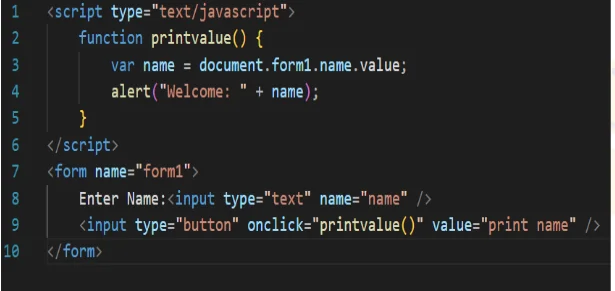
Output:

The document.getElementById() method returns the element of specified id. We can use document.getElementById() method to get value of the input text. But we need to define id for the input field.
Example;
In the example above, getElementById is a method, while innerHTML is a property.

In the example above, getElementById is a method, while innerHTML is a property.
Let’s see the simple example of document.getElementById() method that prints cube of the given number.

The document.getElementsByName() method returns all the element of specified name. The syntax of
the getElementsByName() method is given below:
| document.getElementsByName(“name”) Here, name is required. |
Example of document.getElementsByName() method
In this example, we going to count total number of genders. Here, we are using getElementsByName() method to get all the genders.

Output:

The document.getElementsByTagName() method returns all the element of specified tag name. The syntax of the getElementsByTagName() method is given below:
| document.getElementsByTagName(“name”) |
Example of document.getElementsByTagName() method
In this example, we going to count total number of paragraphs used in the document. To do this, we have
called the document.getElementsByTagName(“p”) method that returns the total paragraphs.

Another example of document.getElementsByTagName() method
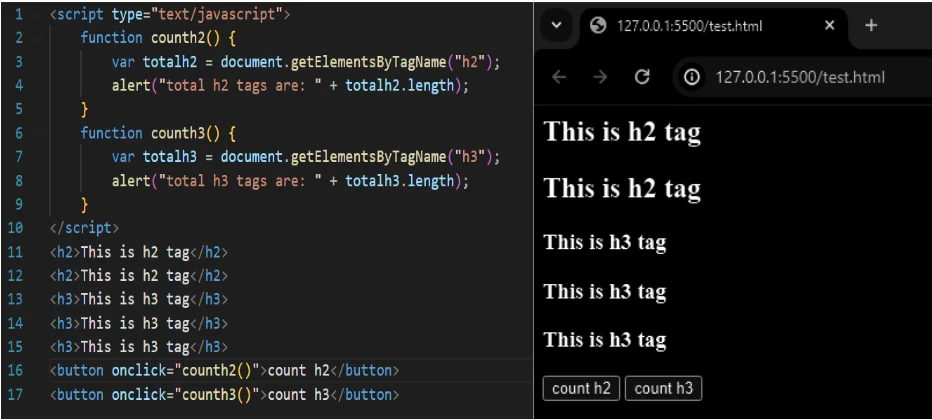
The innerHTML property can be used to write the dynamic html on the html document. It is used mostly in the web pages to generate the dynamic html such as registration form, comment form, links etc.
Example of innerHTML property
In this example, we are going to create the html form when user clicks on the button. In this example, we are dynamically writing the html form inside the div name having the id mylocation. We are identifying this position by calling the document.getElementById() method.

Output:

The change in the state of an object is known as an Event. In html, there are various events which represents that some activity is performed by the user or by the browser. When JavaScript code is included in HTML, JavaScript react over these events and allow the execution. This process of reacting over the events is called Event Handling. Thus, JavaScript handles the HTML events via Event Handlers.
For example, when a user clicks over the browser, add js code, which will execute the task to be performed on the event.
Some of the HTML events and their event handlers are:
Mouse events:
| Event Performed | Event Handler | Description |
| Click | Onclick | When mouse click on an element |
| Mouseover | Onmouseover | When the cursor of the mouse comes over the element |
| Mouseout | Onmouseout | When the cursor of the mouse leaves an element |
| Mousedown | Onmousedown | When the mouse button is pressed over the element |
| Mouseup | Onmouseup | When the mouse button is released over the element |
| Mousemove | Onmousemove | When the mouse movement takes place. |
Keyboard events:
| Event Performed | Event Handler | Description |
| Keydown & Keyup | onkeydown & onkeyup | When the user press and then release the key |
Form events:
| Event Performed | Event Handler | Description |
| Focus | onfocus | When the user focuses on an element |
| Submit | onsubmit | When the user submits the form |
| Blur | Onblur | When the focus is away from a form element |
| Change | onchange | When the user modifies or changes the value of a form element |
Window/Document events:
| Event Performed | Event Handler | Description |
| Load | Onload | When the browser finishes the loading of the page |
| Unload | onunload | When the visitor leaves the current webpage, the browser unloads it |
| Resize | Onresize | When the visitor resizes the window of the browser |
Let’s discuss some examples over events and their handlers.
Click Event

Output:

Mouse Over Event:

Output:

Focus Event:

Output:

Keydown Event:

Output:

Load event:
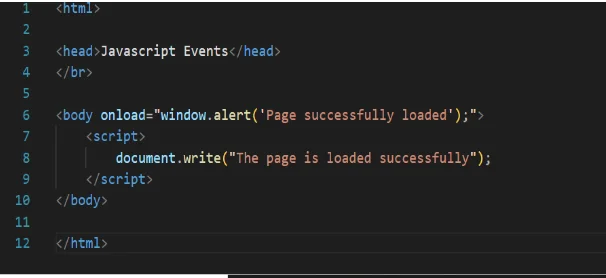
Output:

It is important to validate the form submitted by the user because it can have inappropriate values. So, validation is must to authenticate user.
JavaScript provides facility to validate the form on the client-side so data processing will be faster than server-side validation. Most of the web developers prefer JavaScript form validation.
Through JavaScript, we can validate name, password, email, date, mobile numbers and more fields.
In this example, we are going to validate the name and password. The name can’t be empty and password can’t be less than 6 characters long.
Here, we are validating the form on form submit. The user will not be forwarded to the next page until given values are correct.

Output:

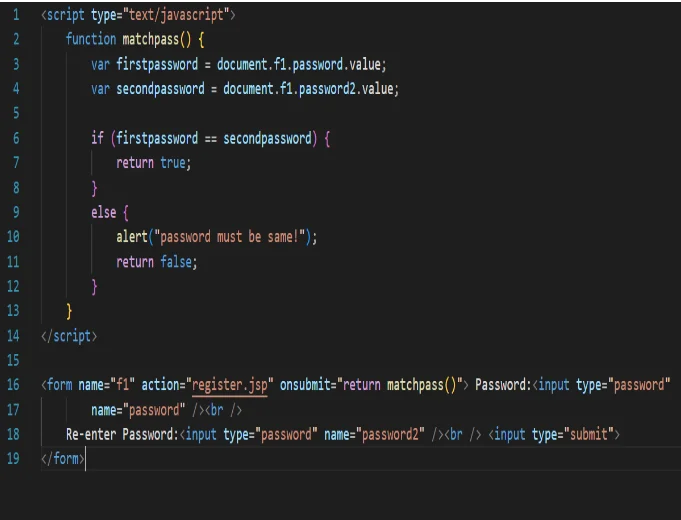
Output:

Let’s validate the text field for numeric value only. Here, we are using isNaN() function.

Output:

Let’s see an interactive JavaScript form validation example that displays correct and incorrect image if input is correct or incorrect.

Output:

We can validate the email by the help of JavaScript.
There are many criteria that need to be follow to validate the email id such as:
o Email id must contain the @ and . character
o There must be at least one character before and after the @.
o There must be at least two characters after. (Dot).
Let’s see the simple example to validate the email field.

Output:



Secondly, the data that is entered must be checked for correct form and value. Your code must include appropriate logic to test the correctness of data.

Output:

JQuery is a fast, small, lightweight, “write less, do more”, and feature-rich JavaScript library. It makes things like HTML document traversal and manipulation, event handling animation, and Ajax much simpler with an easy-to-use API (Application Programming Interface) that works across browsers. With a combination of versatility and extensibility, jQuery has changed the way that millions of people write JavaScript.
JQuery is a JavaScript library. The purpose of jQuery is to make it much easier to use JavaScript on your website. JQuery simplifies a lot of the complicated things from JavaScript like AJAX (Asynchronous JavaScript and XML) calls and DOM (Document Object Model) manipulation. Some of the biggest companies which uses jQuery on the Web are
Features of jQuery:
Some of important feature of jQuery are listed as follows:
Server side script are discrete blocks of program code that execute on a web server (as opposed to a web client) computer. They are generally used to create Dynamic web pages.This means that the page displayed to the user does not exist as a document on the server in its own right, and is only brought into existence in response to a user request. Often, a server-side script provides the interface between a web-based user interface and a database that resides on a web server. PHP is a server side scripting language used to create dynamic web pages. PHP is well suited for web development. PHP stands for hypertext preprocessor. It is an interpreted language. It is embedded in HTML. It is an open source language.

Some important points need to be notice about PHP are as followed:
Features of PHP
Characteristics of PHP
Advantages of PHP / what problem does it solve.
Introduction to PHP:
PHP is an open-source, interpreted, and object-oriented scripting language that can be executed at the server-side. PHP is well suited for web development. Therefore, it is used to develop web applications (an application that executes on the server and generates the dynamic page.).
Before learning PHP, you must have the basic knowledge of HTML, CSS, and JavaScript. So, learn these technologies for better implementation of PHP.
HTML – HTML is used to design static web page.
CSS – CSS helps to make the webpage content more effective and attractive.
JavaScript – JavaScript is used to design an interactive website.
PHP is widely used in web development nowadays. PHP can develop dynamic websites easily. But you must have the basic the knowledge of following technologies for web development as well.
Why use PHP / Strengths of PHP
PHP is a server-side scripting language, which is used to design the dynamic web applications with MySQL database.
Weaknesses of PHP
Common uses of PHP
Object Oriented is an approach to software development that models application around real world objects such as employees, cars, bank accounts, etc. A class defines the properties and methods of a real world object. An object is an occurrence of a class. There are three major principles of OOP are:
PHP in Object oriented programming PHP is an object oriented scripting language. It supports all of the above principles. The above principles are achieved via:
Encapsulation – using “get” and “set” methods.
Inheritance – using extends keyword.
Polymorphism – using implements keyword
Hardware requirement are not much, we just need a laptop or desktop computer. PHP 5.5+ require a computer with at least window 2008/vista.
The computer with Pentium IV processor, RAM 2GB, hard disk 256 GB, color monitor or above is more than enough.
To run PHP code, we need the following software on our local machine.
To run PHP a web development is needed. This needs a PHP compatible web server and interpreter. Package like WAMP, LAMP, and XAMPP etc. can be used which includes a web server.
PHP scripts are plain text. A PHP script begins with <?php and ends with ?>. The PHP code is saved with extension. PHP and is saved in the root directory of web server.
A PHP script can be placed anywhere in the document. A PHP script starts with <?php and ends with ?>:
<?php
// PHP code goes here
?>
⮚ The default file extension for PHP files is “.php”.
⮚ A PHP file normally contains HTML tags, and some PHP scripting code.
⮚ Below, we have an example of a simple PHP file, with a PHP script that uses a built-in PHP function “echo” to output the text “Hello World!” on a web page:

Output:

Note: PHP statements end with a semicolon (;).
In PHP, keywords (e.g. if, else, while, echo, etc.), classes, functions, and user-defined functions are not case-sensitive.
In the example below, all three echo statements below are equal and legal:

Output:

Comments are used to make code more readable. There are two types of comments –single line and multi line comments. A single line comments starts with // while multi-line comment begins with /* and end with */.

Loosely typed language: PHP is a loosely typed language, it means PHP automatically converts the variable to its correct data type.
A variable can have a short name (like x and y) or a more descriptive name (age, carname,
total_volume).
Rules for PHP variables:
∙ A variable starts with the $ sign, followed by the name of the variable
∙ A variable name must start with a letter or the underscore character
∙ A variable name cannot start with a number
∙ A variable name can only contain alphanumeric characters and underscores (A-z, 0-9, and _ )
∙ Variable names are case-sensitive ($age and $AGE are two different variables)
Let’s see the example to store string, integer, and float values in PHP variables.

Output:

The scope of a variable is defined as its range in the program under which it can be accessed. In other words, “The scope of a variable is the portion of the program within which it is defined and can be accessed.”
PHP has three types of variable scopes:
The variables that are declared within a function are called local variables for that function. These local variables have their scope only in that particular function in which they are declared. This means that these variables cannot be accessed outside the function, as they have local scope. A variable declaration outside the function with the same name is completely different from the variable declared inside the function. Let’s understand the local variables with the help of an example:
The global variables are the variables that are declared outside the function. These variables can be accessed anywhere in the program. To access the global variable within a function, use the GLOBAL keyword before the variable. However, these variables can be directly accessed or used outside the function without any keyword. Therefore there is no need to use any keyword to access a global variable outside the function.
Let’s understand the global variables with the help of an example:

Output:

We frequently use the echo statement to display the output. There are two basic ways to get the output in PHP:
o echo
o print
echo and print are language constructs, and they never behave like a function. Therefore, there is no requirement for parentheses. However, both the statements can be used with or without parentheses. We can use these statements to output variables or strings.

Output:

echo
o echo is a statement, which is used to display the output.
o echo can be used with or without parentheses.
o echo does not return any value.
o We can pass multiple strings separated by comma (,) in echo.
o echo is faster than print statement.
o print is also a statement, used as an alternative to echo at many times to display the output.
o print can be used with or without parentheses.
o print always returns an integer value, which is 1.
o Using print, we cannot pass multiple arguments.
o print is slower than echo statement.
Variables can store data of different types, and different data types can do different things. PHP supports the following data types:
It can hold multiple values. There are 2 compound data types in PHP.
There are 2 special data types in PHP.
Booleans are the simplest data type works like switch. It holds only two values: TRUE (1) or FALSE (0). It is often used with conditional statements. If the condition is correct, it returns TRUE otherwise FALSE.
Example:

Output:

Integer means numeric data with a negative or positive sign. It holds only whole numbers, i.e., numbers without fractional part or decimal points.
Rules for integer:
o An integer can be either positive or negative.
o An integer must not contain decimal point.
o Integer can be decimal (base 10), octal (base 8), or hexadecimal (base 16).
o The range of an integer must be lie between 2,147,483,648 and 2,147,483,647 i.e., -2^31 to 2^31.
Example:

Output:

A floating-point number is a number with a decimal point. Unlike integer, it can hold numbers with a fractional or decimal point, including a negative or positive sign.
Example:

Output:

A string is a non-numeric data type. It holds letters or any alphabets, numbers, and even special characters. String values must be enclosed either within single quotes or in double quotes. But both are treated differently. To clarify this, see the example below:
Example:

Output:

An array is a compound data type. It can store multiple values of same data type in a single variable.
Example:

Output:

Objects are the instances of user-defined classes that can store both values and functions. They must be explicitly declared.
Example:

Output:

Resources are not the exact data type in PHP. Basically, these are used to store some function calls or references to external PHP resources.
For example – a database call. It is an external resource. This is an advanced topic of PHP, so we will discuss it later in detail with examples.
Null is a special data type that has only one value: NULL. There is a convention of writing it in capital letters as it is case sensitive.
The special type of data type NULL defined a variable with no value.
Example:

PHP Operator is a symbol i.e used to perform operations on operands. In simple words, operators are used to perform operations on variables or values. For example:
$num=10+20; //+ is the operator and 10,20 are operands
In the above example, + is the binary + operator, 10 and 20 are operands and $num is variable. PHP Operators can be categorized in following forms:
The PHP arithmetic operators are used to perform common arithmetic operations such as addition, subtraction, etc. with numeric values.
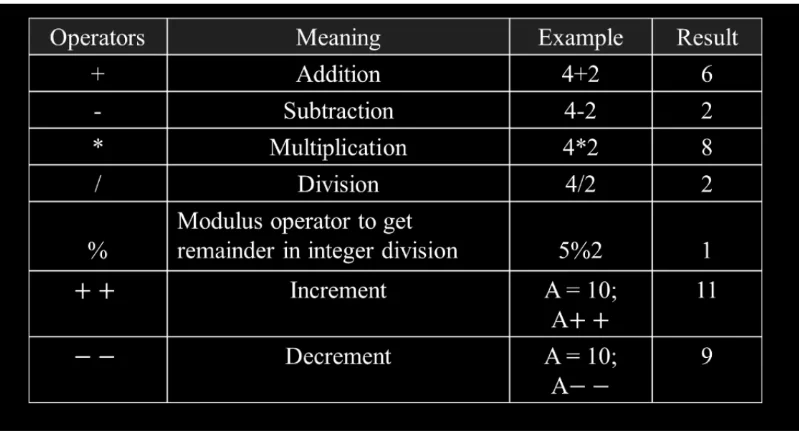
The assignment operators are used to assign value to different variables. The basic assignment operator is “=”.

The bitwise operators are used to perform bit-level operations on operands. These operators allow the evaluation and manipulation of specific bits within the integer.

Comparison operators allow comparing two values, such as number or string. Below the list of comparison operators are given:

The increment and decrement operators are used to increase and decrease the value of a variable.

The logical operators are used to perform bit-level operations on operands. These operators allow the evaluation and manipulation of specific bits within the integer.

We can create and use forms in PHP. To get form data, we need to use PHP super global $_GET and $_POST. The form request may be get or post. To retrieve data from get request, we need to use $_GET, for post request $_POST.
Get request is the default form request. The data passed through get request is visible on the URL browser so it is not secured. You can send limited amount of data through get request.
Let’s see a simple example to receive data from get request in PHP.
File: form1.html

File: welcome.php

Post request is widely used to submit form that have large amount of data such as file upload, image upload, login form, registration form etc.
The data passed through post request is not visible on the URL browser so it is secured. You can send large amount of data through post request.
Let’s see a simple example to receive data from post request in PHP.
File: form1.html

File: login.php

| S.N. | GET Method | S.N. | POST Method |
| 1 | Only limited amount of data can be sent because is sent in header. | 1 | Large amount of data can be sent because data is sent in body. |
| 2 | GET request is not secured because data is exposed in URL bar. | 2 | POST request is secured because data is not exposed in URL bar. |
| 3 | GET request can be bookmarked. | 3 | POST request cannot be bookmarked. |
| 4 | GET is essentially used for fetching the information. | 4 | The purpose of POST method is to update the data. |
| 5 | It can be cached. | 5 | It cannot be cached. |
| 6 | GET method is the default method if the method is not specified in the form. | 6 | POST method must be specified in the form. It is not default method. |

Output:


Output:


Output:


Output:

Database: To organize the data in systematic and manageable form, the database is required. The database is the system where data and information are stored and organized systematically. ⮚ The stored data can be retrieved easily when required.
⮚ Data are stored in tabular form.
⮚ The number of columns and rows forms the table.
The column of the table is known as a field that has a unique field name and the row of the table is known as records which represent individual information. Each table has a unique field known as a primary key. Each of the records of the primary field is different which make distinct from other records for identification.
MySQL is the most popular database system used with PHP. With PHP, we can connect to and manipulate MYSQL databases. It is a database system used on the web that runs on a server. It can be used for organized databases for both small and large applications. It is comparatively more fast, reliable, and easy to use than other databases. It uses standard SQL and compiles on a number of platforms.

A communication system is a set of interconnected components or devices that facilitate the transfer of information from one point to another. The fundamental purpose of a communication system is to convey meaningful data or messages from a source to a destination. Telephone, radio and television are the main and popular media of telecommunication.
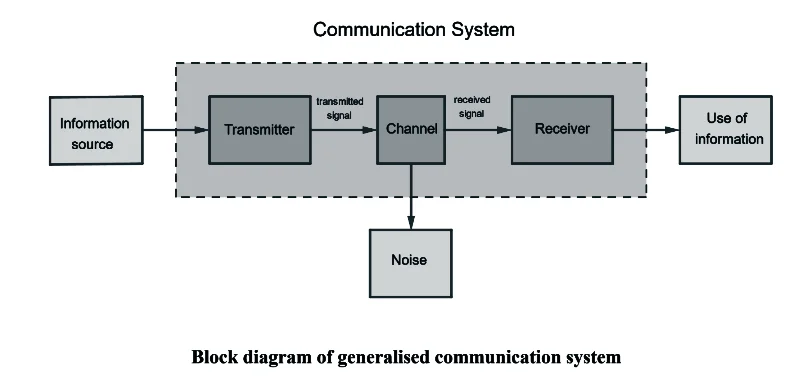
Information Source:
❖What it is: The starting point of communication.
❖Example: Your friend sharing a funny story with you.
❖In simple terms: Where the message or story originates.
Transmitter:
❖What it is: Converts the message into a suitable form for sending.
❖Example: Your friend speaking the words of the funny story.
❖In simple terms: Changes the message so it can be sent effectively.
Channel:
❖What it is: The pathway through which the message travels.
❖Example: The air carrying the sound waves of your friend’s voice.
❖In simple terms: The route the message takes to reach you.
Receiver:
❖What it is: Grabs the message and turns it back into something understandable.
❖Example: You listening to your friend’s words and understanding the story.
❖In simple terms: Catches and makes sense of the message.
Noise:
❖What it is: Unwanted disturbances that can mess up the message.
❖Example: Background chatter making it hard to hear your friend’s story.
❖In simple terms: Anything that makes it difficult to understand the message.
Use of Information:
❖What it is: Putting the received message to some purpose.
❖Example: Laughing at the punchline of your friend’s funny story.
❖In simple terms: Doing something with the information you received.
Data may be transferred from one device to another by means of some communication media. The electromagnetic or light waves that transfer data from one device to another device in encoded form are called signals. Data transmissions across the network can occur in two forms i.e.:
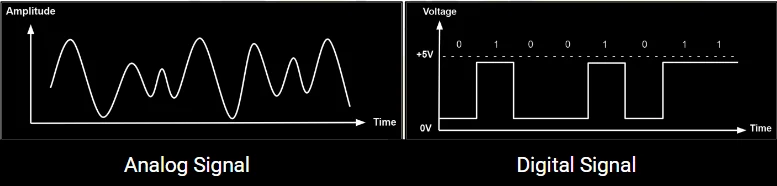
Analog Signal:
The transfer of data in the form of electrical signals or continuous waves is called analog signal or analog data transmission. An analog signal is measured in volts and its frequency is in hertz (Hz).
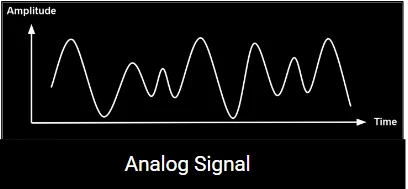
Digital Signal:
The transfer of data in the form of digit is called digital signal or digital data transmission. Digital signals consist of binary digits 0 & 1. Electrical pulses are used to represent binary digits. Data transmission between computers is in the form of digital signals.
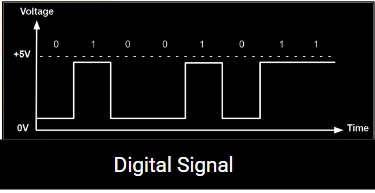
Modulation means to change. It is the process of changing or encoding the carrier wave at certain amplitude (height) and frequency (timing).
OR
The process of changing some characteristics (amplitude, frequency or phase) of a carrier wave in accordance with the intensity of the signal is known as modulation.
There are three types of modulation:
Data communication is the process of exchanging data among the computing devices. Data may be in different form like file, text, image, sound etc. These data are transmitted between a source and a destination. Source device is responsible for generating data and destination device is responsible for receiving the data generated by source. Communication like, email, IRC, VOIP etc. are examples of data communication. Data communication is the transmission of electronic from one computing device to another. The data communication comprises of following elements:
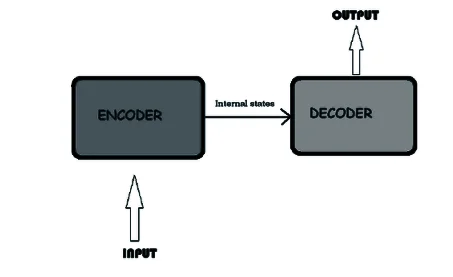
Mode of communication normally refers to the ways in which communication takes place or data gets transmitted between source and destination nodes. Modes of data transmission direct the direction, mechanism of data flow between devices.
a. Half Duplex
b. Full Duplex
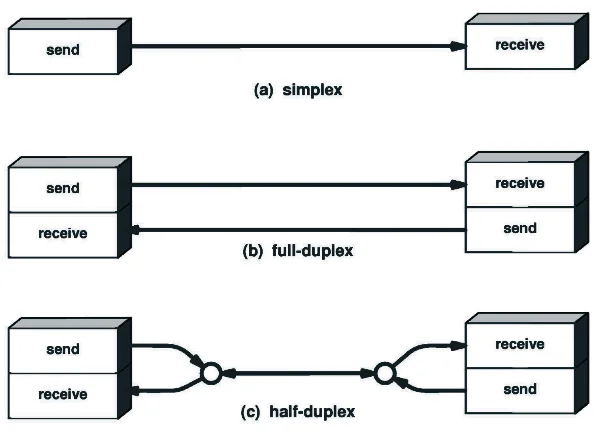
In this type of communication data transmission takes place only in one direction. It is also called a unidirectional communication mode. Radio, Television, Newspaper and keyboard to CPU Communication are some of the most common example of simplex communication.
Features:
⮚ Data are transmitted in only one direction.
⮚ The sender sends data and receiver receives only.
⮚ There is not bidirectional communication.
⮚ Listeners cannot reply immediately.
⮚ Radio and television broadcast are its examples.
In duplex communication mode data transmission is possible from both directions. The receiver can immediately respond to the sender. The duplex communication can be categorized into two groups.
Half Duplex:
In this type of communication mode data can be transmitted in both directions, but only in one direction at a time. Both sender and receiver cannot transfer the data at a time. While sending data it cannot receive it and while receiving data it cannot send.
Features:
⮚ Data are transmitted in both direction but single direction at one time.
⮚ Receiving end acts as mere listener while sender sends data and vice versa.
⮚ The communication is slower.
⮚ Walkie Talkie used by the police man is the best example of half-duplex communication mode.
Full Duplex
Full Duplex communications allows data to flow the information at the same time. Speaking on telephone of full Duplex communication mode in which both the sender and receiver can speak simultaneously. Bidirectional communication at the same time is called full duplex communication mode.
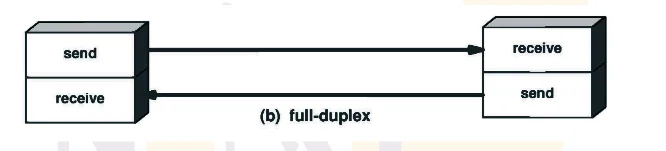
Features:
⮚ Data are transmitted in both direction at the same time.
⮚ When one end sends data other end can receive as well as send data.
⮚ Communication is faster.
⮚ Telephone is an example of full duplex mode.
| S.N. | Simple | Half Duplex | Full Duplex |
| 1. | It is a uni-directional communication. | It is a two way directional communication but one at a time. | It is a two way directional communication simultaneously. |
| 2. | Sender can send the data but can’t receive the data in it. | Sender can send the data and also can receive the data but one at time in it. | Sender can send the data and also can receive the data simultaneously in it. |
| 3. | It provides less performance than half duplex and full duplex. | It provides less performance than full duplex. | It provides better performance than simple and half duplex mode. |
| 4. | Examples: radio, newspaper | Examples: Walky-talky and wireless handset | Example: smart phone and landline phones. |
⮚ Computer Network is defined as the collection of two or more autonomous computers which are interconnected together for sharing resources with the help of transmission media and set of protocols.

⮚ Data sharing
⮚ Print service
⮚ File service
⮚ Database service
⮚ Application service
Advantages of Computer Network:
Disadvantages of Computer Network:
On the basis of size computer networks can be classified into three categories:
⮚ It is personal device network within a limited area.
⮚ It consists of a computer, mobile, Personal Digital Assistant (PDA). It can be used for communication among these personal devices for connecting to a digital network and the internet.
Advantages
Disadvantages
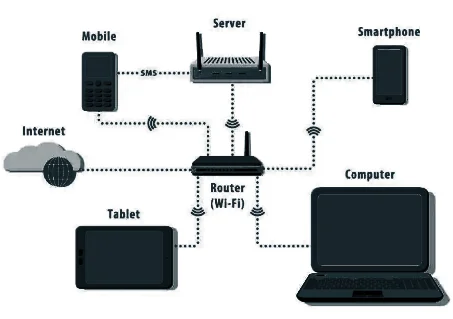
Advantages of LAN
Disadvantages of LAN
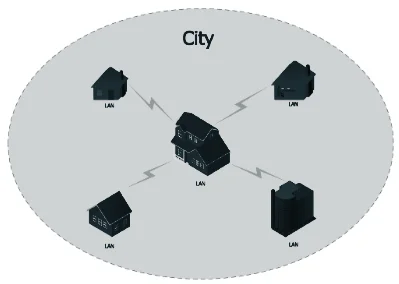
Advantages of MAN
Disadvantages of MAN

Advantage of WAN
Disadvantage of WAN
| S.N. | Local Area Network (LAN) | S.N. | Wide Area Network (WAN) |
| 1. | Area covered within a local site. | 1. | Distance up to thousands of K.M. |
| 2. | Higher data transfer rates (10 Mbps to 1Gbps even more). | 2. | Data transfer rate is less |
| 3. | It has low error rates. | 3. | It has higher error rates. |
| 4. | It uses simple protocol, low cost devices and low cost installation. | 4. | It uses complex protocols, expensive devices and high cost installation. |
| 5. | It can support limited number of hosts. | 5. | It can support large number of hosts. |
| 6. | Eg. Star, cellular topologies etc. | 6. | Eg. Internet and intranet |
| S.N. | LAN | MAN | WAN |
| 1. | The computer network limited over small geographical area such as building or room. | The computer network spread over the city or country is known as MAN . | The computer network spread over the world is known as WAN. |
| 2. | It is owned by an private organization. | It can be owned by private or public organizations. | There is no single ownership or WAN . |
| 3. | The bandwidth of LAN is high. i.e. data transmission rate. | The data transmission rate is slower in comparison to LAN. | The data transmission rate is slowest in comparison to LAN and MAN. |
| 4. | There is less congestion in LAN. | There is more congestion in MAN. | There is more congestion in comparison to LAN and WAN. |
| 5. | It is easy to design and maintain. | It’s design and maintenance is difficult than LAN. | It’s design and maintenance is difficult than LAN and MAN. |
| 6. | There is more fault tolerance. | There is less fault tolerance. | There is also less fault tolerance. |
| 7. | It is used in school, college, hospital…etc. | It is used in city, towns. | It is used for countries, continent and globe. |
| 8. | Transmission channels are normally twisted pair cables. | Transmission channel are fiber optics, coax cable. | Communication channel ranges from fiber optics cables to communication satellites. |
| 9. | It Stands for Local Area Network | It stands of Wide Area Network | It stands for Metropolitan Area Network. |
A transmission media is defined as the means of communication between two networking devices that helps to transfer data from sender to receiver and vice versa.
⮚ Transmission channel is the path through which data are transmitted from source to destination.
⮚ The path through which data transmit from source to destination is known as communication media.
Transmission media is broadly classified into two groups.
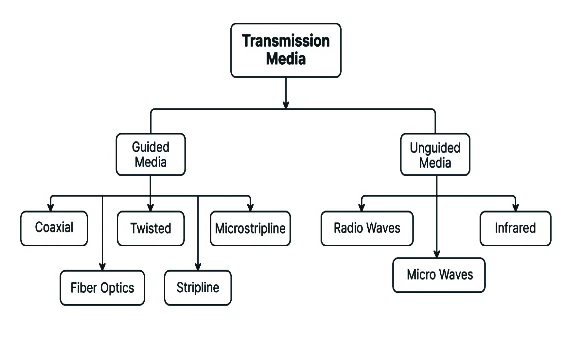
⮚ Guided Media are those communication channels that directly link with each other through cables or other physical media.
⮚ Data are transmitted in the closed path through transmission media.
⮚ Data gets transmitted through wires or cables in guided media.
⮚ In guided media, there is a direct connection between source and destination nodes.
⮚ Guided media has high bandwidth, low cost, and high security.
⮚ Data transmission is faster than wireless.
⮚ The most commonly used guided media are Twisted Pair cable, Coaxial Cable and Fiber Optics.

⮚ The data transmitted in this medium is through electromagnetic waves so that any physical wire or cable is not required for the transmission.
⮚ Unguided media transmission is bounded by geographical areas.
⮚ Different types of unguided media are: Microwave, Radio wave, satellite communication, Bluetooth, Infrared, Wi-Fi, Li-Fi.
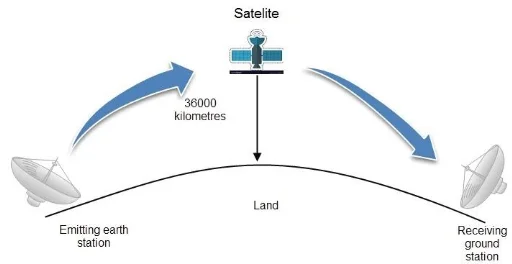
| S.N. | Guided Transmission Medium | S.N. | Unguided Transmission Medium |
| 1. | Signal is directed and contained by the physical limits of the medium. | 1. | It has no physical medium for the transmission of electromagnetic signals. |
| 2. | It is called wired communication or bounded transmission media. | 2. | It is called wireless communication or unbounded transmission media. |
| 3. | The signal energy propagates through wires in guided media. | 3. | The signal energy propagates through air in unguided media. |
| 4. | It types are twisted pair cable, coaxial cable and fiber optic cable. | 4. | It types are radio wave, microwave and infrared. |
| 5. | Examples: Twisted pair cable, coaxial cable and fiber optic cables. | 5. | Examples: Microwave or radio links and infrared light. |
The transmission of data and information from source to destination by using physical medium like wires are called bounded transmission media. Its types are as follows.
1) Twisted pair cable
i) Shielded Twisted pair cable (STP)
ii) Unshielded Twisted pair cable (UTP)
2) Coaxial Cable:
2.1. Thinnet
2.2. Thicknet
3) Fiber optics
A pair of copper wires is twisted to each other in a helical path making the same structure as a DNA molecule.
– The reason for twisting is to reduce electrical interference.
– It is the cheapest and easily available wire.
– It is mostly used in telephone systems.
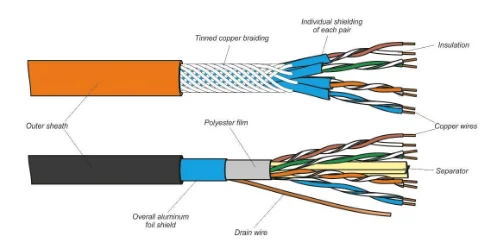
Advantages
Disadvantage
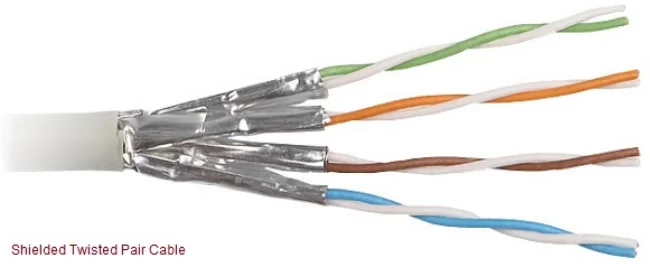
Features of STP Cable:
» Better performance and high data transfer rate.
» Eliminates cross talk
» Faster than UTP
» More expensive
Features:
▪ Less expensive.
▪ Easy to install.
▪ High speed capacity.
▪ Susceptible to external interference.
▪ Lower capacity and performance than STP.
▪ Short distance transmission.
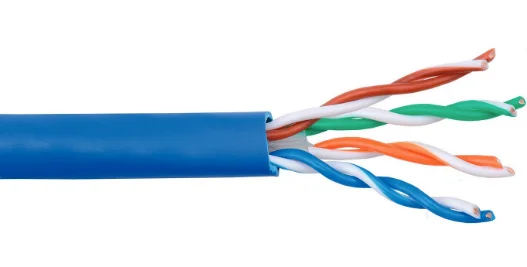
| S.N. | UTP | S.N. | STP |
| 1. | Electromagnetic interference and noise is more in UTP | 1. | STP cable reduce electrical noise within the cable and from outside of the cable. |
| 2. | It offers speed or throughput of about 10 to 1000 Mbps. | 2. | It offers speed or throughput of about 10 to 100 Mbps. |
| 3. | It offers maximum cable length of about 100 meters. | 3. | It supports maximum segment of length about 100 meters. |
| 4. | UTP is widely used for data transmission within short distance and is very popular for home network connecting. | 4. | STP is mainly used for connection of enterprises over a long distance. |
| 5. | The cost of UTP is less when compared to that of STP. | 5. | STP is costlier than UTP. |
Coaxial cable is a type of copper cable specially built with a metal shield and other components engineered to block signal interference. It is primarily used by cable TV companies to connect their satellite antenna facilities to customer homes and businesses.
Coaxial cable contains two conductors inner and outer, which are separated by an insulator. These two conductors lies parallel to each other. The inner conductor is made up of copper wire which is covered by an inner insulator. The inner insulator is again covered by outer conductor or metal foil. Outer metal wrapping is used as a protection against noise and as the second conductor which completes the circuit. The outer conductor is covered with an insulating cover.
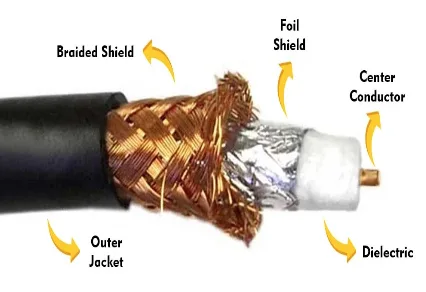
Advantages:
Disadvantages
Coaxial cable is of two types:
(a) Baseband transmission (Thin net): It is defined as the process of transmitting a single signal at high speed.
(b) Broadband transmission (Thick net): It is defined as the process of transmitting multiple signals simultaneously.
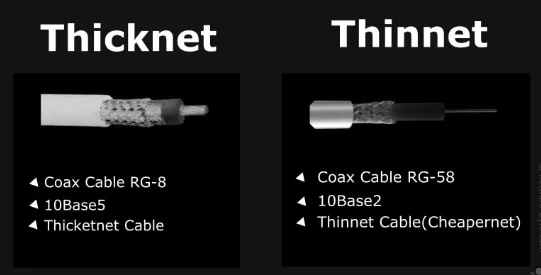
It is the most advanced media in communication, which uses light rather than electricity to transmit information. Optical fiber is very thin media, which is measured in microns and is very hard to identify with our naked eye. They’re designed for long-distance, high-performance data networking, and telecommunications. Fiber optic cables support much of the world’s internet, cable television, and telephone systems.
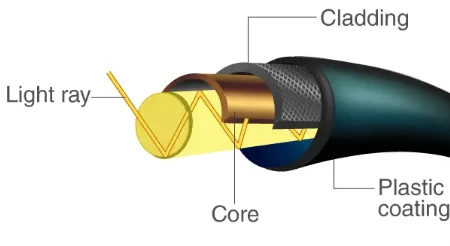
Features:
Advantages:
Disadvantages:
Unbound transmission is also called wireless or unguided media. If there is no physical connectors (wires) between the two communicating device is called wireless transmission media. Its types are as follows.
Radio wave are the signals ranging frequency in between 3 KHz and 1 GHz. When the antenna transmits the radio wave, they are propagated in all directions. Due to this the sending and receiving antenna doesn’t need to be in line of sight position. Antenna is responsible for converting outgoing data packets into radio waves and vice-versa.

Features:
⮚ It is wireless communication technology that transmits voice or data over the air using a lower frequency band than microwaves.
⮚ The signal is travel in up and down manner so that it can reach any place until the strength of waves falls.
⮚ AM and FM radios and cordless phones use radio waves for transmission.
Microwave, in contrast, have been used in data communications for a long time. They have a higher frequency than radio wave and therefore, they can handle larger amounts of data. There are, of course, problems with microwaves attenuation and environmental interference.
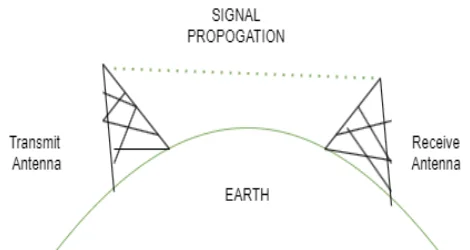
⮚ Microwave transmission is the line of sight transmission.
⮚ The transmit station must be in visible contact with the receive station.
⮚ The microwave is unidirectional.
⮚ This sets the limit on the distance between stations depending on the local geography.
⮚ The microwave is another type of electromagnetic waves that have a frequency range of 1 GHz to 300 GHz.
⮚ In this transmission, whenever the signals are transmitted through an antenna, proper alignment of sending antenna and receiving antenna should be maintained.
Infrared offers a great unbound photonic solution like fiber-optic cabling. Infrared communications use light. So, they are not bound by the limitations of electricity. They are normally used for short range communication such as in communication of remote and TV, AC etc.
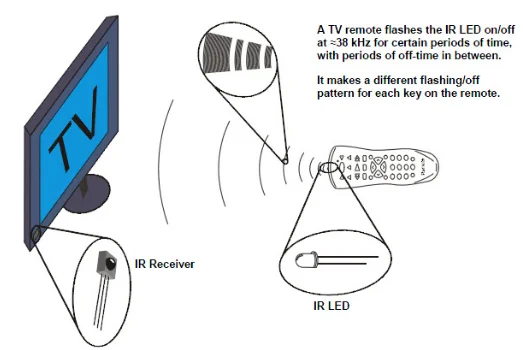
These are the artificial satellites which are placed in the space for the purpose of communication between different antennas available of on the earth. These artificial satellites facilitate the transmission of signals between stations of the earth. They relays and amplifies radio telecommunication by creating communication channel between source transmitter and destination transmitter.
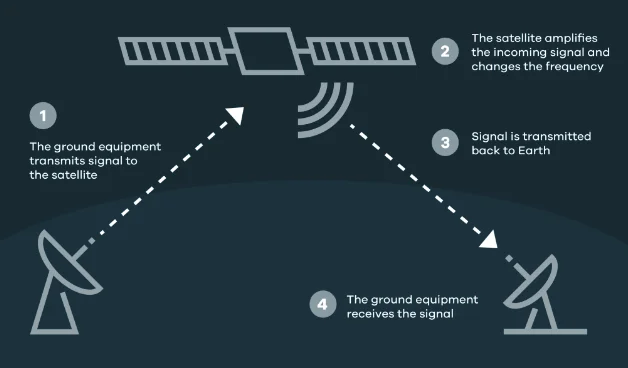
(Jitter, Singing, Echo, Crosstalk, Distortion, Noise, Bandwidth and Number of receivers)
Jitter:
⮚ When we make a call over internet with anyone and suddenly line drops and their voice starts breaking up, it’s called jitter.
⮚ Jitter is defined as a variation in the delay of received packets.
⮚ Jitter is when there is a time delay in the sending of these data packets over your network connection.
Singing:
⮚ Singing is the result of sustained oscillations due to positive feedback in telephone amplifiers or amplifying circuits.
⮚ Singing may be regarded as echo that is completely out of control. This can occur at the frequency at which the circuit is resonant.
Echo:
⮚ Echo in telephone systems is the return of a talker’s voice. It is most apparent to the talker himself or herself. Secondarily, it can also be an annoyance to the listener.
⮚ Echo is a major annoyance to the telephone user. It affects the talker more than the listener. Two factors determine the degree of annoyance of echo: its loudness and its length of delay.
Crosstalk:
⮚ Crosstalk is a disturbance caused by the electric or magnetic fields of one telecommunication signal affecting a signal in an adjacent circuit.
⮚ It is an effect of a wire on another. One wire acts as a sending antenna and the transmission medium acts as the receiving antenna. Just like in telephone system, it is a common experience to hear conversation of other people in the background. This is known as cross talk.
Distortion:
⮚ Distortion is the change in the form or shape of the signal. Signals are made up of different frequencies are composite signals.
⮚ Distortion occurs in these composite signals. Any change in a signal that alters the basic waveform or the relationship between various frequency components is called distortion. It is usually a degradation of the signal.
Noise:
⮚ Noise is another impairment in data communication. During data communication there are some random or unwanted signals mix up with the original signal is called noise.
⮚ Noises can corrupt the signals in many ways along with the distortion introduced by the transmission media.
Bandwidth:
⮚ Bandwidth is the amount of data transmitted through the transmission channel at certain period of time. High bandwidth means higher bits of data are transmitted and low bandwidth means less bits of data are transmitted through the communication channel.
⮚ The bandwidth of analog device is measured in Hertz (Hz) and bandwidth of digital device is measured in bps (bits per second). It is also known as data holding capacity of transmission channel.
Receiver:
⮚ Receiver, in electronics, any of various devices that accept signals, such as radio waves, and convert them (frequently with amplification) into a useful form. Examples are telephone receivers, which transform electrical impulses into audio signals, and radio or television receivers, which accept electromagnetic waves and convert them into sound or television pictures.
Network architecture refers to the various services provided by the network and it also deals with how data is transmitted from one computer to others.
⮚ The server is a high capacity high speed computer with a large memory.
⮚ Server contains the network operating system.
⮚ The central server manages, organize, and coordinate all network clients on the network.
⮚ The most common service is provided by different servers are file services, print services,
⮚ Message services and database services.
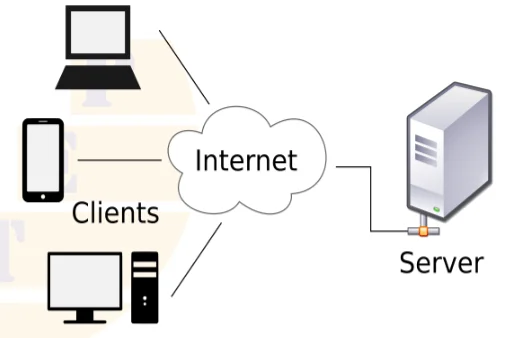
Advantages
Disadvantages
⮚ Each workstations act as both a client and a server.
⮚ There is no central repository for information and no central server to maintain.
⮚ Peer to peer network are generally simpler and less expensive.
⮚ A peer to peer network is also known as a distributed network.
⮚ Peer to peer computing or networking is a distributed application architecture that partitions task or workstations between peers.
⮚ Peers are equally privileged and equal participants in the application.
⮚ Each node shares its sources with other nodes in the network.
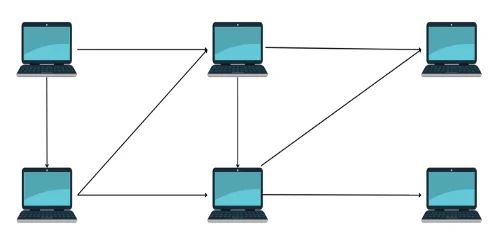
Advantages
Disadvantages
| Client Server | Peer to peer |
| 1. It is also known as centralized or server based network. | 1. It is also known as distributed network. |
| 2. It has central server computer. | 2. There is no central server computer. |
| 3. The central server manages, organize, and coordinate all network clients on the network. | 3. Peers are equally privileged and equal participants in the application. |
| 4. Client server network are more expensive. | 4. Peer to peer network are generally simpler and less expensive. |
| 5. It has high security. | 5. It is less security. |
| 6. If server crashes there is a chance of data loss. | 6. Data and information is shared around the network, so less chance of data loss. |
| 7. Example, Google server, Yahoo server and Bank etc. | 7. Example One to one computer and Bluetooth connectivity etc. |
Network topology refers to the physical layout of the network. It shows the geographical representation of all the links and linking devices, also called nodes. It is the shaped of Network. The main objectives of the network topology is to find out the most economical and efficient way of transmission channel.
Its types are as:
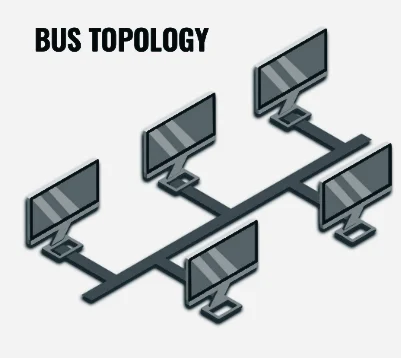
Advantages
Disadvantages
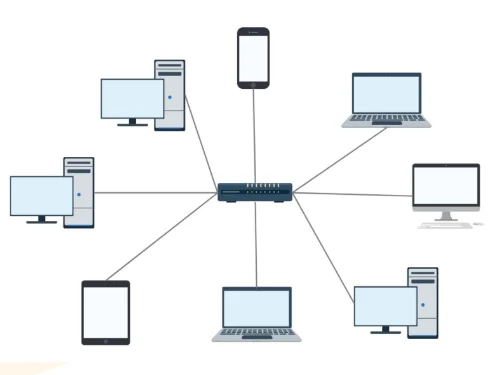
Advantages
– It is simple, reliable and easy to set up and re-configuration.
– It is flexible to connect new computer and remove existing computer in the network.
– It is very easy to find out fault.
– If any computer in the network goes down, then other computers can continue their functions.
Disadvantages
– It requires very large amount of cables.
– It is expensive topology.
– If there is any problem in central device hub or switch then the entire network will be down.
– The data traffic is high in central device hub.
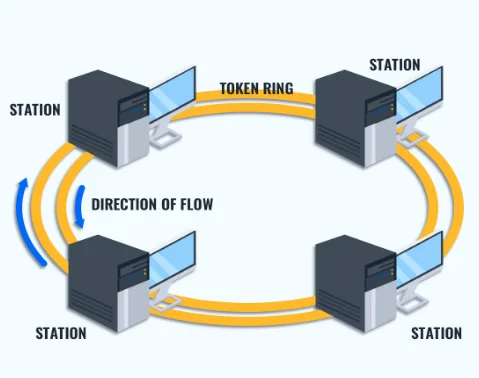
Advantages
– It is simple and inexpensive topology.
– There is less chance of data collision because of unidirectional data transmission.
– There is no server so each computer has equal access facilities to the resources.
– Its performance is better than bus topology for small size network.
Disadvantages
– It is not flexible topology so it is difficult for adding and removing new nodes.
– It is not suitable for large size network.
– If there is problem in any computer or connection then the entire network goes down.
– It is very difficult to find out the errors in the network.
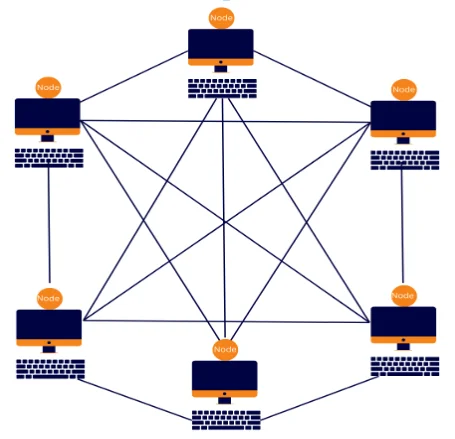
Advantages
– It is fastest and most reliable topology.
– Failure in any computer or transmission media does not affect the rest of the network.
– There is less amount of data traffic due to multiple paths.
Disadvantages
– It is very much complex and most expensive topology.
– It is difficult to find an error in the network.
– It is difficult to add and remove nodes in the network so it is not flexible.
– It requires maximum amount of cables and multiport connectors.
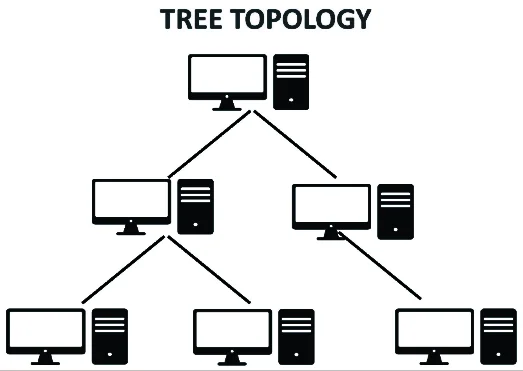
Advantages
– It is easy to manage network as per our needs.
– It is very flexible so we can add and remove any number of nodes.
– It is easier to find the fault nodes or hubs in the network.
Disadvantages
– The failure of root node will cause the failure of entire network.
– It is expensive because it needs large number of cable and network device.
– The data traffic is high at root nodes.
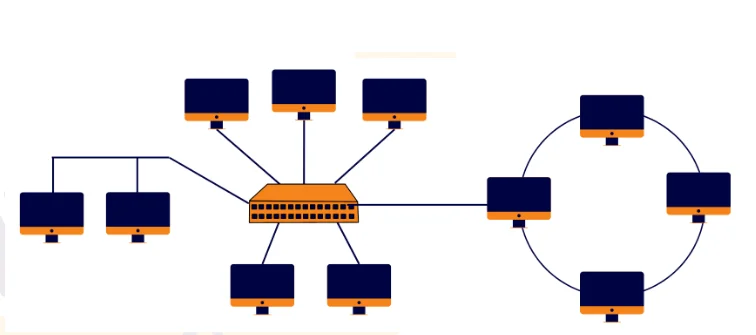
Advantages
⮚ Reliable
⮚ Scalable
⮚ Flexible
⮚ Effective
Disadvantages
⮚ Complexity of design
⮚ Costly connecting devices
⮚ Costly infrastructure
It is based on a proposal developed by the international organization for standardization (ISO). The model is called ISO OSI reference model, because it deals with connecting open system i.e. the system that are open for communication with other system.
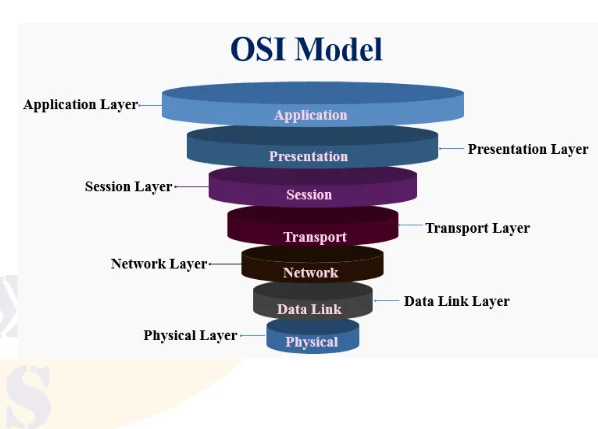
i. Logical Link Control
ii. Media Access Control
i. X.25 Protocol
ii. Internet Protocol
i. Port Addressing
ii. Segmentation & Reassemble
iii. Connection Control
The devices of computer network which are used to connect network is called the network connecting devices. We can connect two or more networks together to create larger network. A LANs can be connected others LANs, MANs or WAN.
The NIC contains the electronic circuitry needed to ensure the reliable communications between workstations and servers. The NIC is the electronic interface between the computer and the LAN cabling. The card itself uses a bus-specific edge connector to plug into the computer motherboard. On the exposed side of the NIC, there are cabling ports that plug directly into the LAN cabling.
As the name implies, repeaters repeat network data. In general, repeaters operate at the electronic level and contain no real intelligence. A repeater accepts weak signals, electrically regenerates them and then sends the messages on their way. There are two types of repeaters: amplifiers and signal-regenerating repeaters.
Technically speaking, a hub is simply a multiport repeater. In addition to regenerating network data, hubs add form and function to the layout of the LAN. In many topologies, the hub is the central component of the network transmission media. There are three types of hubs. They are the passive hub, active hub and intelligent hub.
It is a device, which connects different network segments and passes data with the same communication protocols. It is the connecting device between two or more hubs.
– It operates at layer 2 (Data Link Layer) of OSI Model.
– It reduces unnecessary traffic problem by controlling broadcasting.
– Bridges are more intelligent than hubs because they maintain MAC address tables in them and forward data looking on it.
A router transmits information from one network to another. The router selects the best path to route a message, based on the destination address and origin. The router can direct traffic to prevent head-on collisions and smart enough to know when to direct traffic along back roads and shortcuts.
– Direct signal traffic efficiently.
– Route message between any two protocols.
– Route message between different topologies.
– Route message across fiber optic, coaxial, and twisted-pair cabling.
Gateways are just like routers but much more complex and powerful than routers. They are slower than router and expensive. A gateway has all the features of router and bridges but it can translate instruction set on sending network into receiving network.
– Gateways make communication possible between different architecture and environments.
– Gateways having higher layer functionalities and works on multiple layer protocols.
The term Wi-Fi suggests Wireless Fidelity. It is hardware and software devices. It is wireless technology and network connecting device. Wi-Fi is not a technical term. The technical term of Wi-Fi is “IEEE802.11”
– It has limited range.
– Wi-Fi is used in many personal computers, video game consoles, MP3 players, smart phones, printers, digital camera, laptops computers and other devices.
– Wi-Fi is used to create wireless LAN to connect computer system.
Bluetooth is a wireless technology standard for exchange data over short distance from fixed and mobile devices. Bluetooth is used to create personal area networks (PANs) with high levels of security.
Infrared (IR) light is electromagnetic radiation with a wavelength longer than that of visible light and below the red light. These wavelengths correspond to a frequency range of approximately 100 GHz to 100 THz and include most of the thermal radiation emitted by objects near room.
The Internet is an interconnected network of thousands of networks and millions of computers linking business, educational institutions, government agencies, and individuals together.
Uses / Application of internet
The subnet mask number helps to define the relationship between the host (computers, routers switches, etc.) and the rest of the network. As the name indicates, the subnet mask is used to subdivide a network into smaller, more manageable chunks.
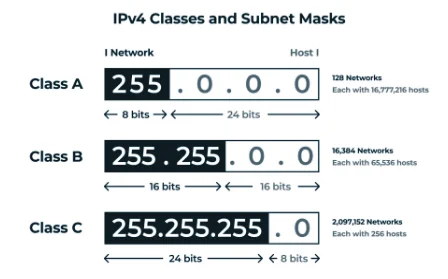
A gateway is a network node that serves as an access point to another network, often involving not only a change of addressing but also a different networking technology.
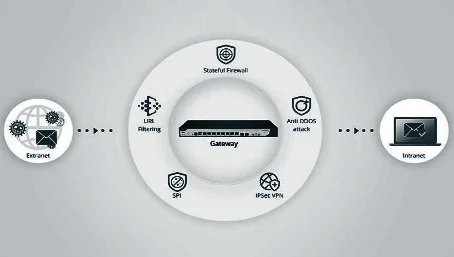
An Internet Protocol address (IP Address) is an unique identification number assigned to each devices connected in a network that uses Internet protocol for communication. The typical IP address looks like 216.27.67.137
IP address are expressed in decimal as above which is easier for us to remember, but computers communicate in binary. So same IP address looks like 11011000.00011011.00111101.10001001
IP address has four sets of number separated by a period ( . ), These sets are Called Octets. IP address perform mainly two functions. One is identification of Network and Identification of particular host in that network.
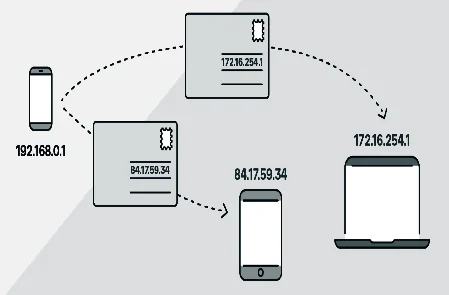
Media Access Control (MAC) address also known as hardware or physical address is unique number associated with a network adapter (NIC). It is used to uniquely identify each device (node) of a network. MAC address is usually assigned by the manufacturer of a network interface card (NIC) and are stored in its ROM. All NIC developed contains unique MAC address. It is a 12 digit hexadecimal number (48 bit in length) and are Written in following formats.
MM:MM:MM:SS:SS:SS or MM-MM-MM-SS-SS-SS
The first half of the address contains ID number of the adapter regulated by an Internet standards body and other half represent the number assigned by the manufacturer. For example: 00:A0:C9:14:C8:29 The prefix 00A0C9 indicates manufactures Intel Corporation and 14C829 indicates a particular host.
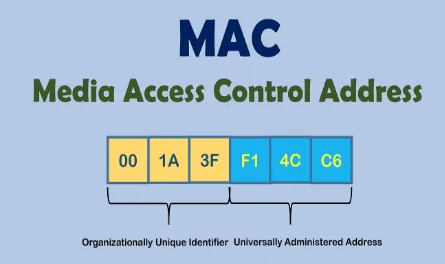
Intranet:
An intranet is a private network that uses internet protocols, to securely share part of an organization’s information between its employees. An intranet is a Local Area Network or Wide Area Network that uses TCP/IP protocol but, belongs to a corporation, school, or organization.
The intranet is accessible only to the organization’s workers. If the intranet is connected the Internet, then it is secured by a firewall to prevent unauthorized users from gaining access to it.
Advantages of an Intranet
1.Workforce productivity: Employees can easily access and share information in-between their workgroups which enhances productivity.
2.Time: With intranets, organizations can make more information available to employees in any time.
3.Communication: Intranets can serve as powerful tools for communication within an organization.
Extranet:
An extranet is a private intranet that can be accessed by outside users over the secure channel. To gain entrance to the extranet resource, an external user must log on to the networks by providing a valid user ID and password. The extranet is a combination of the public Internet and the closed intranet.
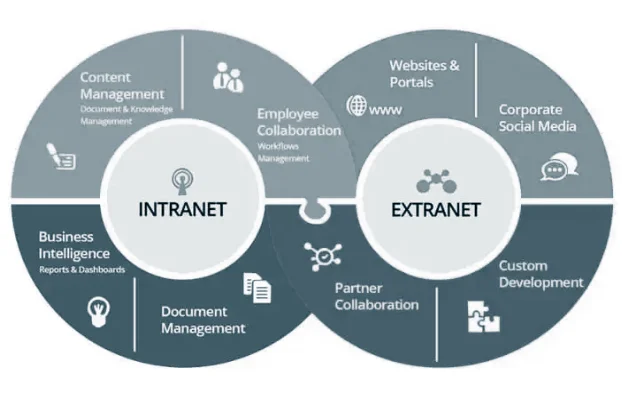
|
Intranet |
Internet |
| 1. It is a private network. | 1. It is a public network. |
| 2. Intranet users are your own employees who know a lot about the company, its organizational structure and special terminology. | 2. Internet user know much less about your company and also care less about it. |
| 3. The intranet is used for everyday work inside the company. | 3. The Internet is mainly used to find out information. |
| 4. The intranet will have many official draft reports, project progress reports, human resource information, and other detailed information. | 4. Internet have all types of information based on requirements. |
| 5. Intranet has less amount of information. | 5. Internet has tremendous amount of information. |
| 6. Intranet can work on low and mid-bandwidth. | 6. Internet requires higher bandwidth. |
Network tools are used for supporting easier and effective network connections. Some of the network tools are:
A communication protocol is a formal description of digital message formats and the rules for exchanging that message in between computer systems. Protocols define a set of formal rules describing how to transmit data especially across a network.
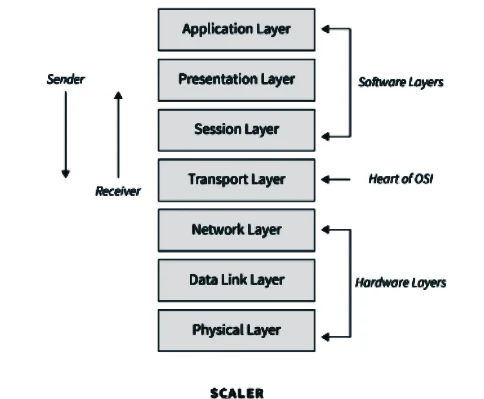
Data is defined as the raw facts and figures. It could be any number, pictures, sound, alphabet, or any combination of it which do not provide clear meaning. Examples, Ram, 12, 75, etc. Here, Ram, 12, 75 does not provide clear meaning. It could mean 12 GB RAM which costs $75 or 12 years old Ram which could give 75 kg of wool in its lifetime.
Sources of Data:
Data processing is the mechanism of converting unprocessed data into meaningful results or information.
When data are processed using a database program or software, they are converted to a meaningful result, called information. The information provides answers to “who”, “what”, “where”, and “when” questions.
Examples: Ram, roll no 12 and he scored 75 out of 100 in a test.
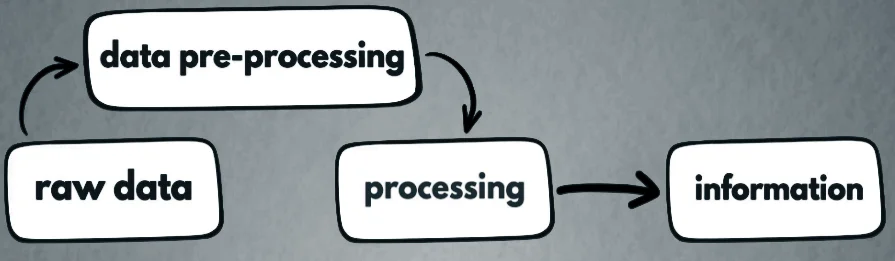
Difference between Data and Information
| S.N. | Data | S.N. | Information |
| 1 | It is raw or known facts. | 1 | It is processed or refined data. |
| 2 | It stores the facts. | 2 | It presents the facts. |
| 3 | It is inactive (they exist). | 3 | It is active (It enables doing). |
| 4 | It is technology-based. | 4 | It is business-based. |
| 5 | Data is gathered from various sources. | 5 | Information is transformed from data |
| 6 | Data do not have a fixed format. | 6 | Information is normally in the form of tables, graphs, curve lines, etc. |
Limitation of file-based/ Flat file system
A database system consists of a collection of interrelated data and a set of application programs to access, update and manage the data.
Database:
It is organized form of record about some person, organization or something store under certain media. It is a collection of related information about a subject organized in a useful manner that provides a base or foundation for procedure, such as retrieving information, drawing conclusion and make decision.
Advantage of database over flat file or file based system :
| S.N. | File Based System | S.N. | Electronic Database System |
| 1 | It provide detail of the data representation and storage of data. | 1 | Database System gives abstract view of data that hides details. |
| 2 | It doesn’t have a crash recovery mechanism. | 2 | It provides crash recovery mechanism using backup and other security measures. |
| 3 | It is difficult to reduce data redundancy. | 3 | Data redundancy can be done easily. |
| 4 | Searching of data requires a lot of time and effort. | 4 | Data can be easily searched. |
| 5 | Difficult to maintain the database. | 5 | Easy to maintain the database. |
Database Management System is software that manages the data stored in a database. This is a collection of software which is used to store data, records, process them and obtain desired information. Since, data are very important to the end users, we must have a good way of managing data. A DBMS is a collection of programs that manages the database structure and controls access to the data stored in the database. The DBMS make it possible to share the data in the database among multiple applications or users. The DBMS stands between the database and the user.
Examples: MS-Access, Oracle, FoxPro, dBase, SQL server, MySQL, Delphi, Sybase, etc.

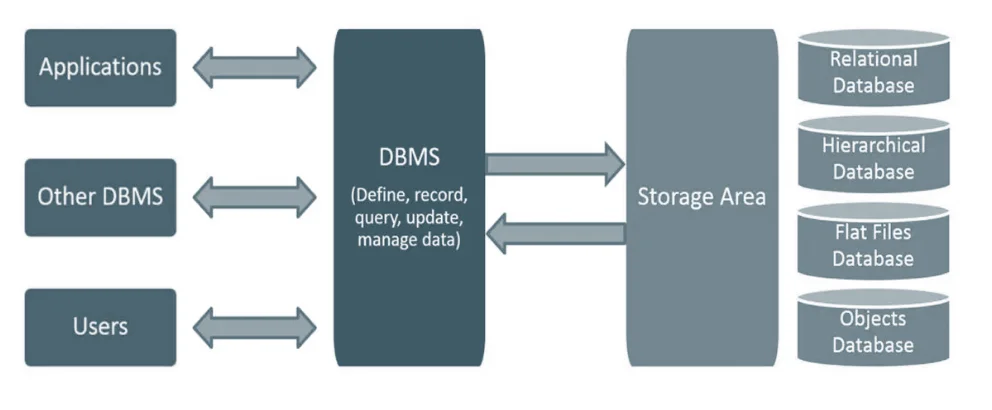
Some major database System activities are (Functions of DBMS)
Advantages of DBMS (Features/Objectives of DBMS)
Disadvantages of DBMS:
A field is a piece of information about an element. A field is represented by a column. Every field has got a title called the field title.
A record is information about an element such as a person, student, an employee, client, etc. A record can have much information in different heading or titles.
A table is the arrangements of rows and columns. Each table must have unique name and must be simple. It is the place where data and information are stored.
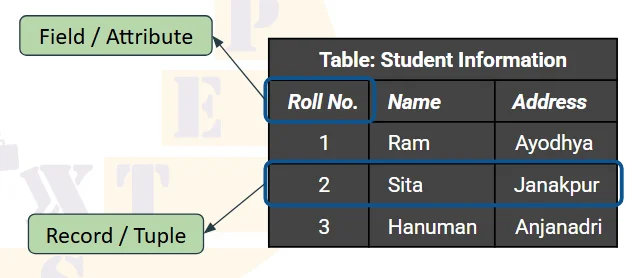
Database Objects are the essential tools of relational database. These database objects helps to store, view, edit and manipulate the data and information stored in database.
It can be used to hold and manipulate the data. Some of the examples of database objects are view, sequence, indexes, form, query report etc.
❖ Table: Basic unit of storage; composed rows and columns
❖ View: Logically represents subsets of data from one or more tables
❖ Sequence: Generates primary key values
❖ Index: Improves the performance of some queries
❖ Synonym: Alternative name for an object
❖ Schema: A schema is the structure of database which defines name of tables, data fields with data types, relationships and constraints.
❖ Instance: It defines data values in a record.
❖ Entity: An entity is a thing or object in the real world that is different from other objects.
❖ Attribute: Attribute is properties possessed by an entity or relationship.
❖ Index: It is used to create indexes in database. It helps searching and sorting operation faster and improves the performances of queries.
❖ Query: It is the object of DBMS which is mainly used to extract and upgrade the necessary records that are present in the database.
❖ Form: It is object of database which is mainly used for data entry. It is easy to add, modify and delete the records in form.
❖ Report: Report are the printed output that is created from table or query. We can’t add, modify and delete the records in report.
Key is a field that uniquely identifies the records, tables or data. Key in a table allows us to establish the relation between multiple tables. Keys are also useful for finding the unique records or combination of records from a large database tables.
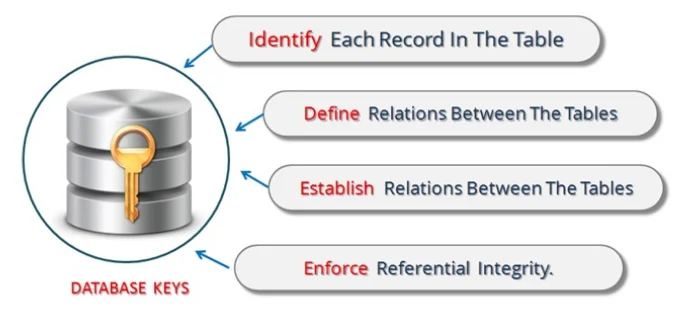
❖ Primary Key: A primary key is one or more columns in a table used to uniquely identify each row in the table. Primary key cannot contain Null value.
A primary key is a special relational database table column (or combination of columns) designated to uniquely identify each table record. A table cannot have more than one primary key.
A primary key’s main features are:
⮚ It must contain a unique value under the field.
⮚ It cannot contain null values.
⮚ Every row must have a primary key value.

❖ Foreign Key: Foreign keys represent relationships between tables. A foreign key is a column whose values are derived from the primary key of some other table.
❖ Candidate Key: If a relational schema has more than one key, that is called a candidate key. All the keys which satisfy the condition of primary key can be candidate key. There can be any number of candidate keys that can be used in place of the primary key if required.
❖ Alternate Key/ Secondary Key: Alternative keys are those candidate keys which are not the primary key. There can be only one primary key for a table. Therefore all the remaining candidate keys are known as alternative.
❖ Compound Key: It has two or more attributes that allow you to uniquely recognize specific record. It is possible that each column may not be unique by itself within the database.

It is an international standard database query language for accessing and managing data in the database.
Features of SQL

| » CREATE: Create is used to create the database or its objects (like table, index, function, views, store procedure and triggers). |
| » DROP: Drop is used to delete objects from the database. |
| » ALTER: Alter is used to alter the structure of the database. |
| » TRUNCATE: Truncate is used to remove all records from a table, including all spaces allocated for the records are removed |
| » COMMENT: Comment is used to add comments to the data dictionary. |
| » RENAME: Rename is used to rename an object existing in the database. |
| » SELECT: It is used to retrieve data from a database. |
| » INSERT: It is used to insert data into a table. |
| » UPDATE: it is used to update an existing data in table. |
| » DELETE: It is used to delete record from table. |
| ⮚ GRAND: It gives user’s access privileges to database. |
| ⮚ REVOKE: It is used withdraw users’ access privileges given by using the GRANT command. |
A Database model defines the logical design and structure of a database and are used to show how data will be stored, accessed and updated in a Database Management System. It refers to the layout of a database and helps in designing a database.
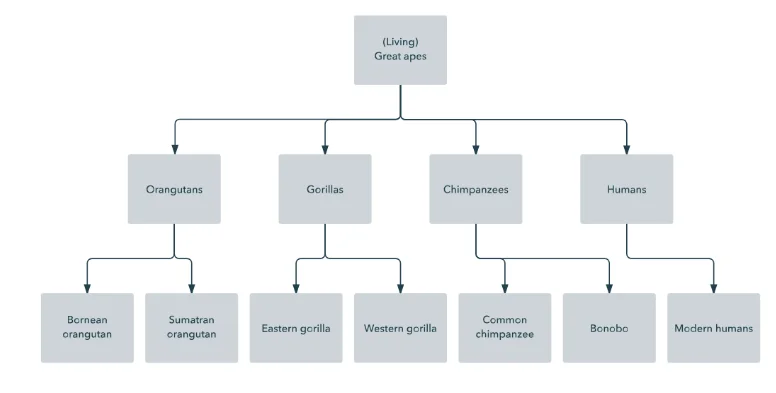
Advantages:
Disadvantages:
2. Network database model: It replaced hierarchical network database model due to some limitations on the model. Suppose, if an employee relates to two departments, then the hierarchical database model cannot arrange records in proper place. So a network database model was created to arrange a non-hierarchical database. The structure of the database is more like a graph rather than a tree structure. A network database model is a database model that allows multiple records to be linked to the same owner file. The network model allows each child to have multiple parents.

Advantages:
Disadvantages:
We notice from below table, here each student has a unique roll number and has marks of subject. Here Roll makes relation between these two tables.
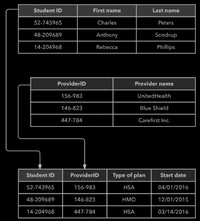
Advantages:
Disadvantages:
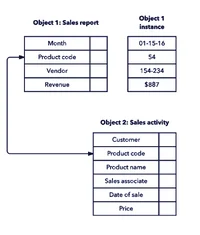
Advantages:
Disadvantages:
The diagrammatic representation of entities attributes and relationship is called E-R diagram. The E-R diagram is an overall logical structure of a database that can be expressed graphically. It was developed to facilitate database design. It is graphical representation of database.
Entity: An entity is defined as anything about which data to be collected and stored.
Relationships: Relationships describes associations among data. Most relationships describes associations between two entities.
Attribute: Attribute describes particular characteristics of the entity.
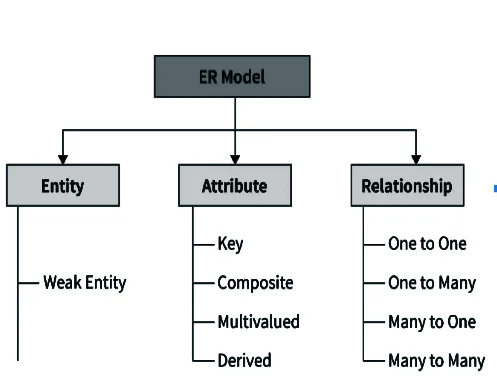
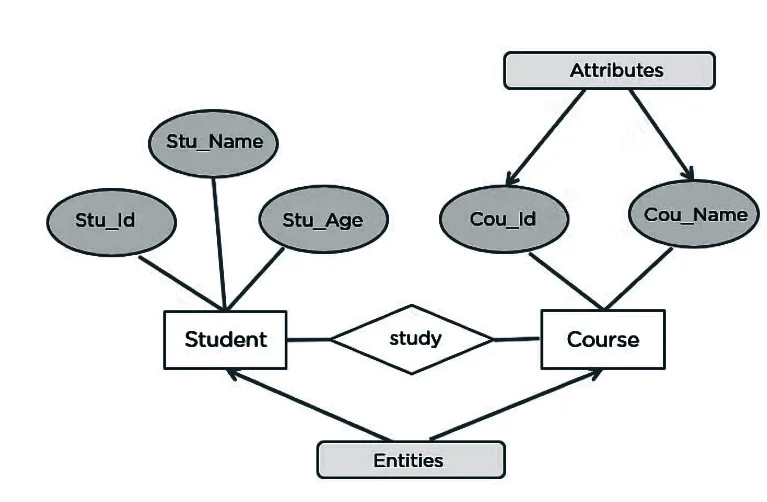
A relationship is an association among several entities and represents meaningful dependencies between them. It is represented by diamond. There are 3 types of relationship:
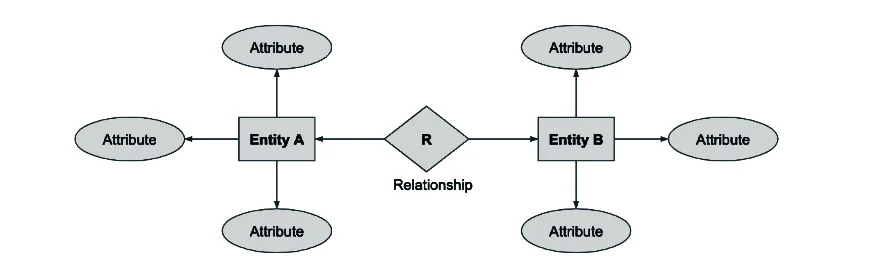
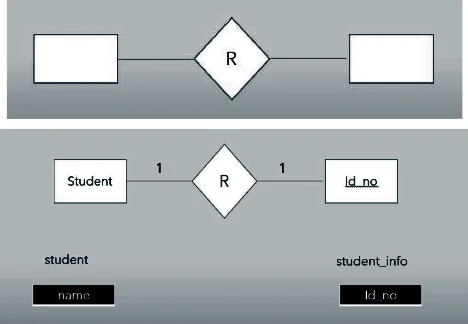
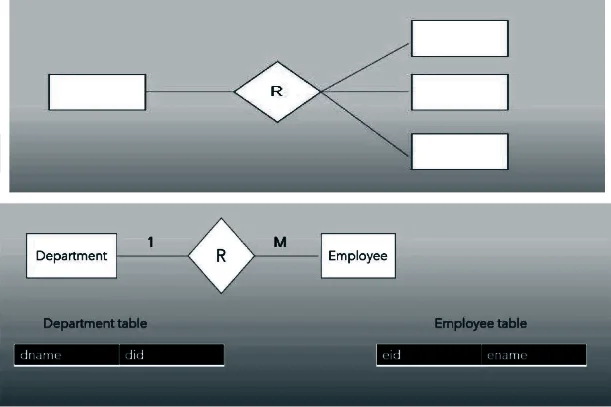
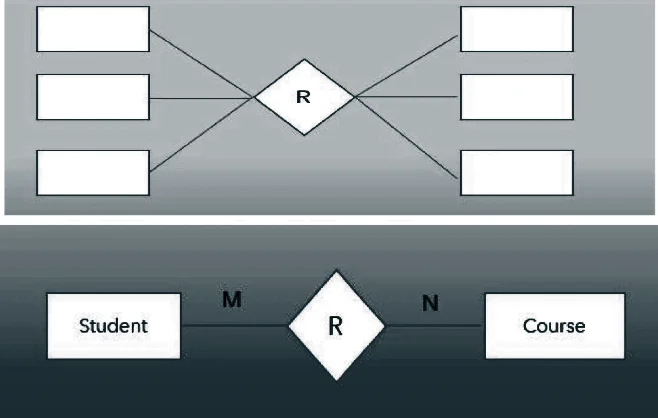
Normalization is a database design process in which complex database table is broken down into simple separate tables. It makes data model more flexible and easier to maintain.
⮚ Database Normalization is a technique of organizing the data in the database. It is a systematic approach of decomposing the tables to eliminate data redundancy and inconsistency. The data is said to be redundant if there is duplicate or repeated data in the table.
⮚ Normalization divides the larger table into the smaller table and links them using relationship. It increase clarity in organizing data in the database.
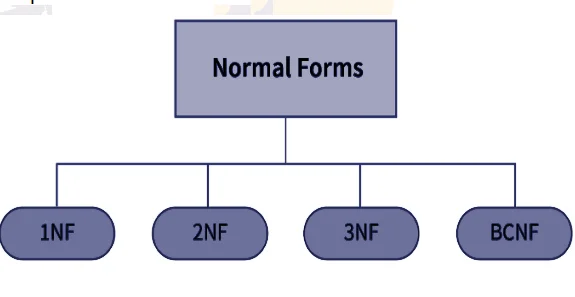
For example:
Below table shown is our database without normalized. Here in table we can see that for the large records of this table, there would be multiple data row of same values especially in the country and city column. So, we can normalize the table by splitting it into two tables where one table only stores the location area of each person name and could be referenced by some unique id. Say Area code.
| Id | Name | Country | City |
| 101 | Alex | Nepal | Kathmandu |
| 102 | Martin | India | Delhi |
| 103 | Melman | Nepal | Kathmandu |
| 104 | Gloria | Japan | Tokyo |
The above table can be normalized in two tables as below:
| Country | City | Area Code |
| Nepal | Kathmandu | N1 |
| India | Delhi | I1 |
| Japan | Tokyo | J1 |
| Id | Area Code | Name |
| 101 | N1 | Alex |
| 102 | I1 | Martin |
| 103 | N1 | Melman |
| 104 | J1 | Gloria |
Advantages of Normalization:
Disadvantages of Normalization:
A table is said to be in first normal form if it has atomic values. There shouldn’t be any repeating groups of attribute in the table. First normal form sets the very basic rules for an organized database.
A table is said to be in 2NF if it is a First normal form and it doesn’t have the partial dependency. Second normal form further addresses the concept of removing duplicate data. o It should be in the first normal form.
Third normal form goes one large step further.
A table is said to be un-normalized when there is repetition of data in a table. In un-normalized table records are not atomic. Let’s take an example of unnormalized table.
Un-normalized table:
Table No.1
| Roll No. | Name | Faculty | Subject |
| 1 | Sundar | ICT | Java, OS |
| 2 | Mukesh | ICT | Network |
| 3 | Ganesh | ICT | C, Web |
A table is said to be in first normal form if it has atomic values. There shouldn’t be any repeating groups of attribute in the table. Following are the main rules for table to be in 1NF:
⮚ Table should have single (atomic) valued attributes/columns.
⮚ Values stored in columns should be of same domain.
⮚ Columns name should not be repeated in table.
⮚ The order of column names doesn’t matter.
The table given above in un-normalized data meets the three requirements among four to be in first normal form. In the subject column more than one subject are stored in a single column for two students. But, each column must contain atomic value to be in first normal form. And the problem is solved in the table given below:
Example of 1NF for above table No.1
Table No.2
| Roll No. | Name | Faculty | Subject |
| 1 | Sundar | ICT | Java |
| 1 | Sundar | ICT | OS |
| 2 | Mukesh | ICT | Network |
| 3 | Ganesh | ICT | Web |
| 3 | Ganesh | ICT | C |
Though, some values are repeated but all columns are atomic for each record /row.
A table is said to be in 2NF if it is in First normal form and it doesn’t have the partial dependency. i.e. each attributes should functionally depend on primary key. Rules for 2 NF:
⮚ A table should be in first normal form.
⮚ There must not be partial dependency.
⮚ Partial dependency exists when any attribute of a table depends on only one part of a composite primary key (primary key combining more than one field) and not on the complete primary key.
⮚ To remove partial dependency, a table can be divided and attributes creating partial dependency are removed in some other tables.
Let’s take an example of table student with student_id, name, address and age as its columns.
| Student_id | Name | Address | age |
Here student_id is the primary key which can identify each records uniquely and can be used to fetch any row of data from this table.
| Student_id | Name | Address | Age |
| 15 | Ganesh | KTM | 17 |
| 16 | Janaki | BKT | 17 |
Here we can get name, address and age of the student easily from their student_id. Which means each column can be fetched using primary key. So, all needed is student_id and every other column depends on it or can be fetched using it.
This is called dependency or functional dependency. And this kind of dependency must be in table to be in second normal form.
In above table a single filed student_id uniquely identifies the all the records of the table. But in some cases combination of two or more columns or fields makes the primary key. Where more than one field acts as primary key. Lets create a table named subject with fields subject_id and subjectname.
| Subject_id | Subjectname |
| 101 | Math |
| 102 | Science |
| 103 | Nepali |
Above we have two tables: student and subject for storing student’s and subject’s information. Now, let’s make a table named Mark storing student’s mark in respective subjects with subject teacher.
| Score_id | Student_id | Subject_id | Marks | Teacher |
| 1 | 15 | 101 | 55 | Bishnu |
| 2 | 15 | 102 | 65 | Umesh |
| 3 | 16 | 103 | 88 | Janvi |
Note: the above table is not in 2nd normal form.
In above table student_id is used to get student’s information where as subject_id is used to get subject name. The combination of student_id and subject_id is the primary in above table. It is because if we want to get mark of student with id 15 then we cannot get because we don’t know which subject. Here we have to give sudent_id and subject_id to uniquely identify any row.
Is there a partial dependency in above table? Obviously, yes. In the given table Mark column name teacher is only dependent on the subject, for math there is Bishnu for science Umesh and so on. But the primary key is the combination of student_id and subject_id, teacher’s name depend only on subject, i.e. subject_id not on the student id.
This situation is known as partial dependency, where an attribute/ column in table depends on only a part of primary key not on the whole key.
Above table can be normalized in second normal form by removing teacher’s name from the Mark table adding it to Subject table.
Subject:
| Subject_id | Subjectname | Teacher |
| 101 | Math | Bishnu |
| 102 | Science | Umesh |
| 103 | Nepali | Janvi |
Mark:
| Score_id | Student_id | Subject_id | Marks |
| 1 | 15 | 101 | 55 |
| 2 | 15 | 102 | 65 |
| 3 | 16 | 103 | 88 |
⮚ For table to be in second normal form, it should be in first normal form.
⮚ Partial dependency exists, when non primary key attribute depends only on a part of primary key instead of complete primary key.
⮚ Partial dependency can be removed by breaking a table and removing attributes causing partial dependency.
A table is said to be in third normal form, if it is second normal form and it doesn’t have any transitive dependency in primary key. The elements that are not dependent on primary key are removed. Transitive dependency occurs in table when a non-primary key attribute depends upon another non primary key attribute. All non-primary key attribute must dependent on primary key attribute or attributes.
Transitive Dependency?
Transitive Dependency occurs when a non-primary key attribute depends upon another non primary key attribute instead of primary key attribute or primary key.
For instance:
In the above table Mark, let’s add some more information such as Exam_name and Full_mark.
| Score_id | Student_id | Subject_id | Marks | Exam_name | Full_marks |
| 1 | 15 | 101 | 55 | First Term | 500 |
| 2 | 15 | 102 | 65 | First Term | 500 |
| 3 | 16 | 103 | 88 | Second Term | 300 |
In above table, student_id and subject_id are the primary key. The column exam_name depends on both student_id and subject_id. But, the Full_marks depends on the Exam_name. The first term exam might have 500 full mark but the second term may have 300 or others. Here exam_name is neither primary key nor the part of primary key still, Full_mark depends on it. So, here full_mark which is non-primary key attribute depends on another nonprimary key attribute known as Exam_name. This situation is known as transitive dependency.
Again, table should be broken into small individual tables to remove it. So we need to remove those fields which are creating transitive dependency. Which looks like.
Score Table
| Score_id | Student_id | Subject_id | Marks | Exam_Id |
| 1 | 15 | 101 | 55 | 11 |
| 2 | 15 | 102 | 65 | 12 |
| 3 | 16 | 103 | 88 | 13 |
Exam Table
| Exam_id | Exam_Name | Full_Marks |
| 11 | First Term | 500 |
| 12 | Second term | 300 |
Benefits of removing transitive dependency:
⮚ Amount of data duplication is reduced.
⮚ Data integrity is achieved.
Note: Normalization does not eliminate data redundancy. Instead, it reduces the redundancy.
Un-normalized Table:
| Employee Id | Name | Address | Department |
| 101 | Ram | Kathmandu | Sales |
| 102 | Bikky | Bhaktapur | Marketing, Export |
| 103 | Anusha | Lalitpur | import |
First Normal Form:
| Employee Id | Name | Address | Department |
| 101 | Ram | Kathmandu | Sales |
| 102 | Bikky | Bhaktapur | Marketing |
| 102 | Bikky | Bhaktapur | Export |
| 103 | Anusha | Lalitpur | import |
Second Normal Form:
Let’s take a table employee having more than one department.
| Employee Id | Department | Salary |
| 101 | Sales | 20000 |
| 102 | Marketing | 25000 |
| 102 | Export | 25000 |
| 103 | Import | 20000 |
Here the non-primary key attribute salary dependent on the employee id only. Here Employee id and department are the candidate key. This violates the rule that “no non primary attribute is dependent on the part of primary key or on the subset of candidate key.”
To make table in 2NF we can break it as:
| Employee Id | Salary |
| 101 | 20000 |
| 102 | 25000 |
| 102 | 25000 |
| 103 | 20000 |
| Employee Id | Department |
| 101 | Sales |
| 102 | Marketing |
| 102 | Export |
| 103 | Import |
Third Normal Form:
| Employee Id | Name | Department | HoD |
| 101 | Rikesh | HR | Mukesh |
| 102 | Binita | Marketing | Mukesh |
| 102 | Jagdish | Store | Bikash |
Here, Employee Id is the primary key and all other are non-primary key attributes. The non- primary key attribute HoD is dependent on non-primary key attribute Department. Here, transitive dependency occurs. To remove it we can decompose table as:
| Employee Id | Department Id | Name |
| 101 | A10 | Rikesh |
| 102 | A11 | Binita |
| 102 | A12 | Jagdish |
| Department Id | Department | Name |
| A10 | HR | Mukesh |
| A11 | Marketing | Mukesh |
| A12 | Store | Bikash |
Example 1
Unnormalized database
| Emp_code | January |
| Emp_name | February |
| Address | March |
| Contact no. | April |
| Date of Birth | May |
| Department | June |
| Designation | July |
| Basic_salary | Daily_allowance |
| Travel_Allownace | Gross_salary |
| Tax | Provident_fund |
Normalized database
| Employee | Salary | Month |
| Emp_code | Basic salary | January |
| Emp_name | Travel allowance | February |
| Address | Daily allowance | March |
| Contact no. | Gross salary | April |
| Date of birth | Provident Fund | May |
| Department | Tax | June |
| Designation | July |
Example 2
| Name | Roll | Class | Sub_name | Sub_marks | Sub_name | Sub_marks |
| Ram | 1 | 11 | Computer | 95 | Account | 78 |
| Sita | 1 | 12 | Computer | 98 | Account | 80 |
| Hari | 2 | 11 | Computer | 80 | Account | 82 |
| Shyam | 2 | 12 | Computer | 92 | Account | 83 |
In above table, we can see that column of subject nome and marks are repeated which are eliminated in 1NF.
| Name | Roll | Class | Sub_name | Sub_marks |
| Ram | 1 | 11 | Computer | 95 |
| Ram | 1 | 11 | Account | 78 |
| Sita | 1 | 12 | Computer | 98 |
| Sita | 1 | 12 | Account | 80 |
| Hari | 2 | 11 | Computer | 80 |
| Hari | 2 | 11 | Account | 82 |
| Shyam | 2 | 12 | Computer | 92 |
| Shaym | 2 | 13 | Account | 83 |
In above table name depends upon roll no and class, subject name only depends upon class, subject marks depends upon name and subject_name. Hence, above table can be decomposed as 2NF:
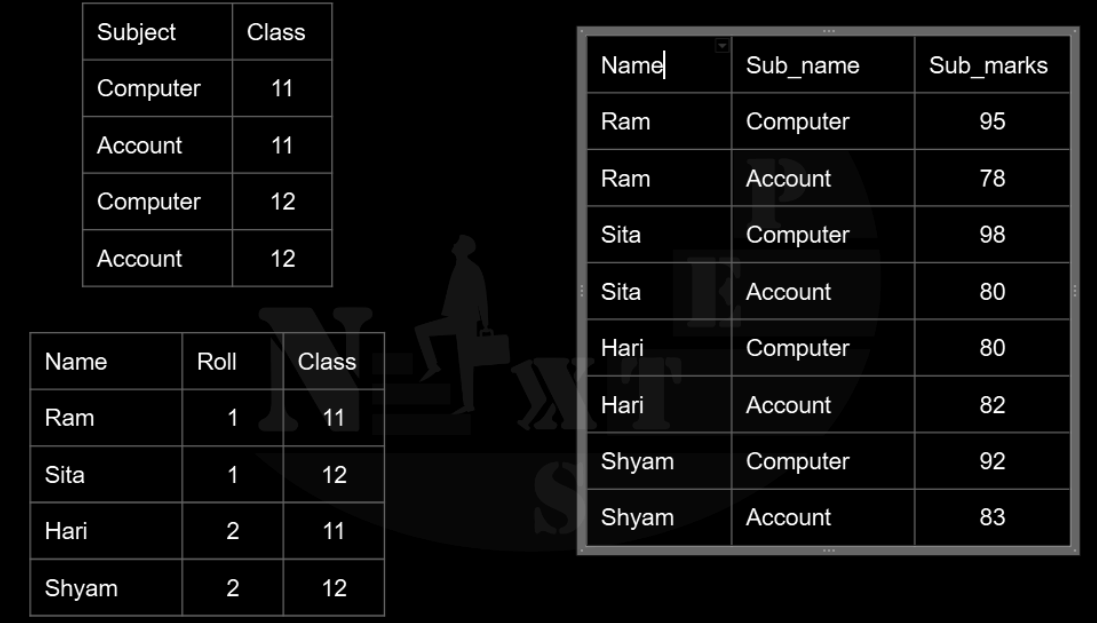
It removes the column that are not dependent on primary key using 3NF above table can be decomposed as:
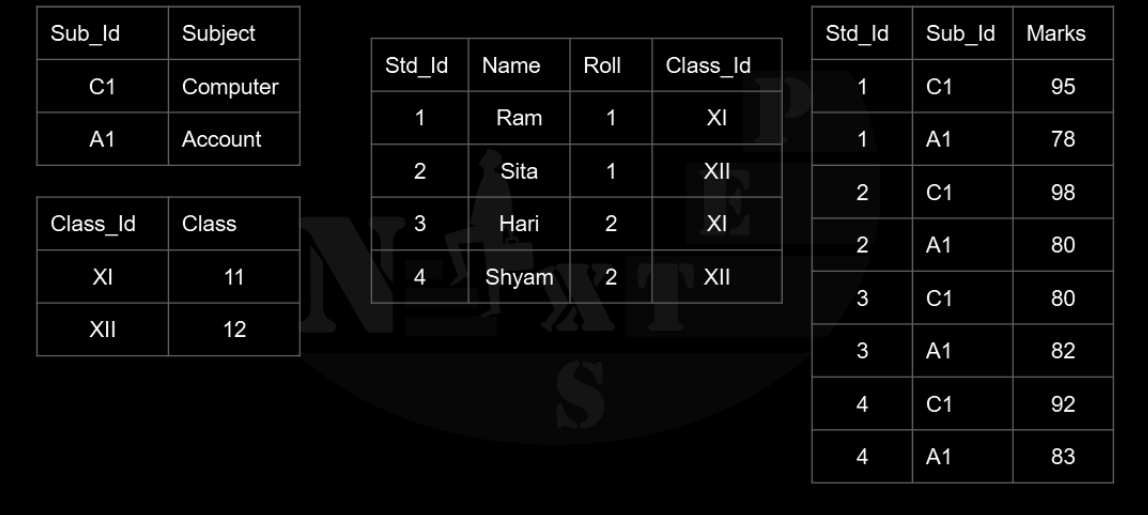
⮚ The database system where data and information are stored in the centralized server or centralized database system.
⮚ The data stored in database are accessed from different locations through several applications. The information (data) is stored at a centralized location and the users from different locations can access this data.
⮚ This type of database contains application procedures that help the users to access the data even from a remote location.
Advantages:
⮚ It decreases risk of data manipulation. i.e. manipulation of data will not affect the core data.
⮚ Data consistency is maintained as it manages data in a central repository.
⮚ It provides better data quality, which enables organizations to establish data standards.
⮚ It is less costly as fewer vendors are required to handle the data sets.
Disadvantages:
⮚ The size of centralized database is large which increases the response time of fetching data.
⮚ It is difficult to update the centralized database.
⮚ If server gets damaged entire data will be lost.
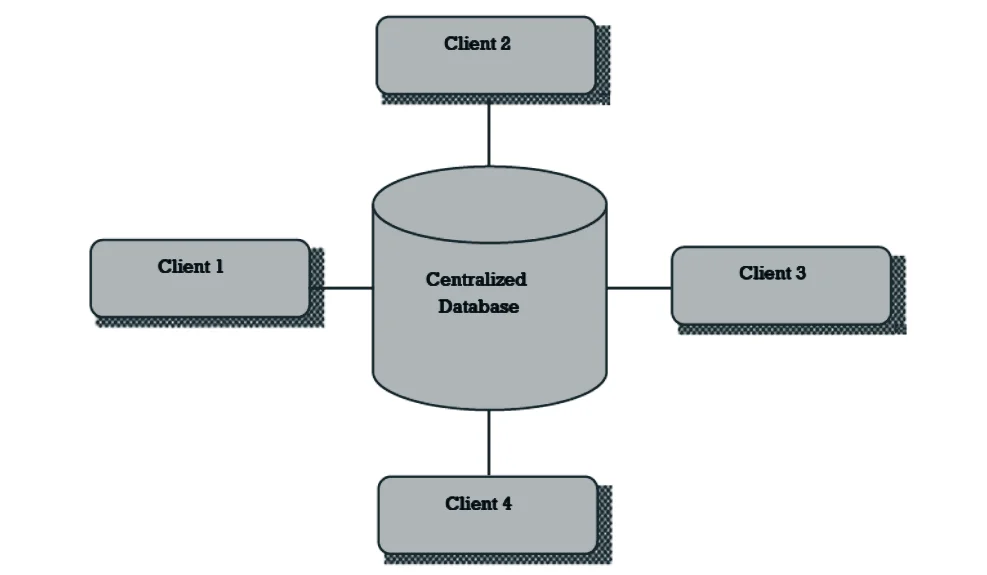
⮚ Distributed database doesn’t store all data and information in the single but store on various sites or places, which are connected by the help of communication, links which helps them to access the distributed data easily.
⮚ In distributed database various portions of a database are stored in multiple different locations along with the application procedures which are replicated and distributed among various points in a network.
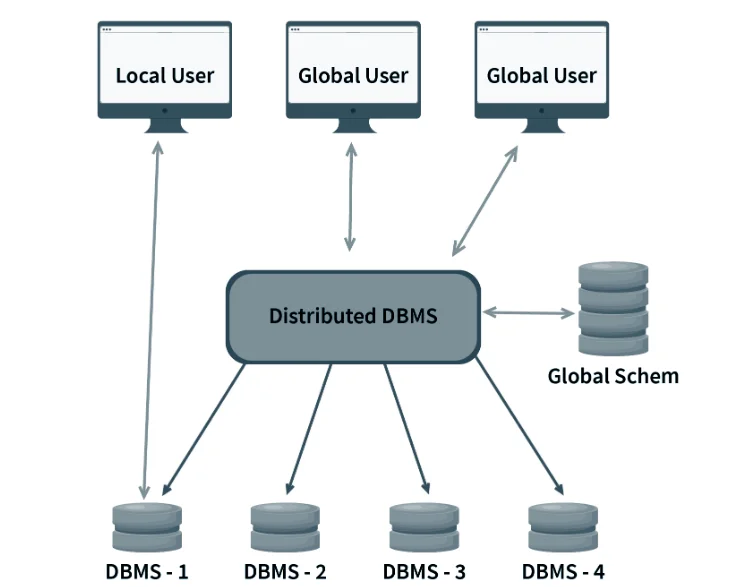
Advantages:
⮚ The system can be expanded by including new computers and connecting them to the distributed system.
⮚ Distributed database is more reliable than centralized database.
⮚ The performance and service are better.
⮚ Large numbers of users are supported.
⮚ One server failure will not affect the entire data set.
Disadvantages:
⮚ It is difficult to administrate and manage the database
⮚ It is expensive to set up.
⮚ This database has high risk of hacking and data theft.
| Centralized database | Distributed database system |
| 1. Simple type. | 1. Complex type. |
| 2. Located on particular location. | 2. Located in many geographical locations. |
| 3. Consists of only one server. | 3. Contains servers in several locations. |
| 4. Suitable for small organizations. | 4. Suitable for large organizations. |
| 5. Less chance of data lost. | 5. More chances of data hacking, lost. |
| 6. Maintenance is easy and security is high. | 6. Maintenance is not easy and security is low. |
| 7. Failure of system makes whole system down. | 7. Failure of one server does not make the whole system down. |
| 8. There is no feature of load balancing. | 8. There is feature of load balancing. |
| 9. Data traffic rate is high. | 9. Data traffic rate is low. |
| 10. Cost of centralized database system is low. | 10. Cost of distributed database system is high. |
A data dictionary is a file which contains meta-data that is data about data. It also called information system catalogue. It keeps all the data information about the database system such as location, size of the database, tables, records, fields, user information, recovery system, etc.
Data integrity referees to the validity or consistency of data in database. It ensures that the data should be accurate and consistent.
Mainly there are 3 types of data integrity constraints used in the database system. They are as:
Data security is protection of data in database system against unauthorized access, modification, failure, losses or destruction. The authorized access means only right people can get the right access to the right data.
DBA is the most responsible person in an organization with sound knowledge of DBMS. He/she is the overall administrator of the program. He/she has the maximum amount of privileges for accessing database and defining the role of the employee which use the system. The main goal of DBA is to keep the database server up to date, secure and provide information to the user on demand.
Qualities of good DBA:
Responsibilities:
XAMPP provides a GUI environment to perform any operations on the database. However, it also provides an option to use SQL statements to perform any operations SQL statements are used in the SQL menu in phpMyAdmin. The SQL statements used in XAMPP also work well with most of the databases.
Syntax: CREATE DATABASE databasename;
Example: CREATE DATABASE School;
Syntax: DROP DATABASE databasename:
Example: DROP DATABASE School:
Syntax: CREATE TABLE table_name (column1 datatype, column2 datatype, column3 datatype….)
Example: CREATE TABLE Students (StudentID int, FName varchar(255), LName varchar(255), Address varchar(255), Class varchar(255));
Syntax: ALTER TABLE table name ADD column_name datatype
Example: ALTER TABLE Students ADD Email varchar(255));
Syntax: ALTER TABLE table name DROP COLUMN column_name;
Example: ALTER TABLE Students DROP COLUMN Email;
Syntax: ALTER TABLE table name MODIFY COLUMN column_name datatype;
Example: ALTER TABLE Students MODIFY COLUMN Class int;
Syntax: DROP TABLE table_name;
Example: DROP TABLE Students;
Syntax: INSERT INTO table name (column1, column2 column3,…) VALUES (valuel, value2, value3);
Example: INSERT INTO Students (StudentID, FName, LName, Address, Class) VALUES (‘101’, ‘Ram’, Sharma’, Pokhara’, 7);
Syntax: SELECT column1, FROM table name column2.
Example:
SELECT * FROM Students; (This will select all the columns from the table Students]
SELECT FNAME, LNAME FROM Students: [This will select only the First Name and Last Name from the table Students.]
Syntax: SELECT column1, column2…. FROM table_name WHERE condition;
Example: SELECT Roll_No, FName FROM Students WHERE Roll_No>10 AND Roll_No<100;
Syntax: SELECT DISTINCT column_name FROM table_name;
Example: SELECT DISTINCT address FROM Students;
Syntax: SELECT column1, column2, … FROM table_name ORDER BY column1 [ASC|DESC];
Example: SELECT Fname, Lname FROM Students ORDER BY Score;
Syntax: DELETE FROM table_name WHERE condition;
Example: DELETE FROM customers WHERE customer_id = 123;
Syntax: UPDATE table_name SET column1 = value1, column2 = value2, … WHERE condition;
Example: UPDATE Students SET LName = “Sharma” WHERE Roll_No = 121;