Basic Concept of Communication System
A communication system is a set of interconnected components or devices that facilitate the transfer of information from one point to another. The fundamental purpose of a communication system is to convey meaningful data or messages from a source to a destination. Telephone, radio and television are the main and popular media of telecommunication.
Communication System Block Diagram
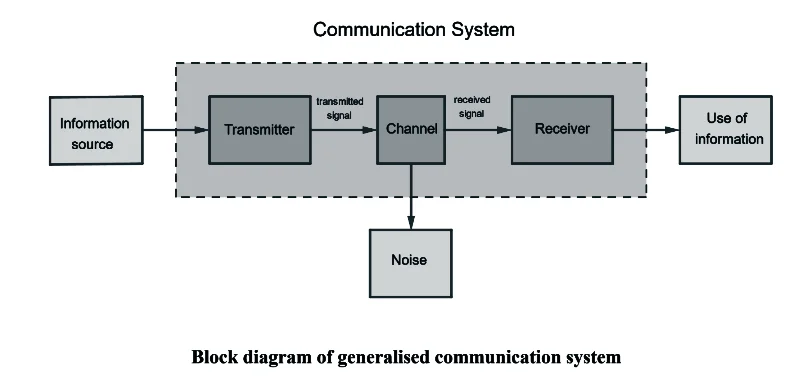
Information Source:
❖What it is: The starting point of communication.
❖Example: Your friend sharing a funny story with you.
❖In simple terms: Where the message or story originates.
Transmitter:
❖What it is: Converts the message into a suitable form for sending.
❖Example: Your friend speaking the words of the funny story.
❖In simple terms: Changes the message so it can be sent effectively.
Channel:
❖What it is: The pathway through which the message travels.
❖Example: The air carrying the sound waves of your friend’s voice.
❖In simple terms: The route the message takes to reach you.
Receiver:
❖What it is: Grabs the message and turns it back into something understandable.
❖Example: You listening to your friend’s words and understanding the story.
❖In simple terms: Catches and makes sense of the message.
Noise:
❖What it is: Unwanted disturbances that can mess up the message.
❖Example: Background chatter making it hard to hear your friend’s story.
❖In simple terms: Anything that makes it difficult to understand the message.
Use of Information:
❖What it is: Putting the received message to some purpose.
❖Example: Laughing at the punchline of your friend’s funny story.
❖In simple terms: Doing something with the information you received.
Data Transmission
Data may be transferred from one device to another by means of some communication media. The electromagnetic or light waves that transfer data from one device to another device in encoded form are called signals. Data transmissions across the network can occur in two forms i.e.:
- Analog signal
- Digital signal
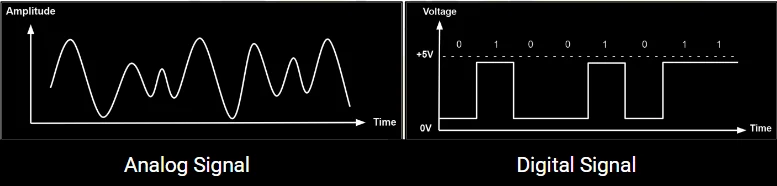
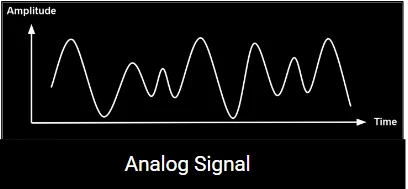
Analog Signal:
The transfer of data in the form of electrical signals or continuous waves is called analog signal or analog data transmission. An analog signal is measured in volts and its frequency is in hertz (Hz).
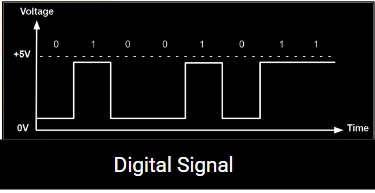
Digital Signal:
The transfer of data in the form of digit is called digital signal or digital data transmission. Digital signals consist of binary digits 0 & 1. Electrical pulses are used to represent binary digits. Data transmission between computers is in the form of digital signals.
Modulation
Modulation means to change. It is the process of changing or encoding the carrier wave at certain amplitude (height) and frequency (timing).
OR
The process of changing some characteristics (amplitude, frequency or phase) of a carrier wave in accordance with the intensity of the signal is known as modulation.
There are three types of modulation:
- Amplitude Modulation (AM): Amplitude modulation is an increase or decrease of the carrier voltage (ec), will all other factors remaining constant.
- Frequency Modulation (FM): Frequency modulation is a change in the carrier frequency (fc) with all other factors remaining constant.
- Phase Modulation (PM): Phase modulation is a change in the carrier phase angle (θ). The phase angle cannot change without also affecting a change in frequency. Therefore, phase modulation is in reality a second form of frequency modulation.
Elements of Data communication System
Data communication is the process of exchanging data among the computing devices. Data may be in different form like file, text, image, sound etc. These data are transmitted between a source and a destination. Source device is responsible for generating data and destination device is responsible for receiving the data generated by source. Communication like, email, IRC, VOIP etc. are examples of data communication. Data communication is the transmission of electronic from one computing device to another. The data communication comprises of following elements:
- Sender (Source)
- Medium
- Receiver
- Data
- Protocol
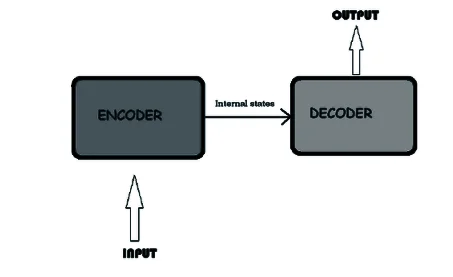
- Encoder
- Decoder
- Sender (Source): It is the device that generates and sends that message.
- Medium: It is the channel or physical path through which the message is carried from the sender to the receiver. The medium can be wired like twisted pair wire, coaxial cable, fiber-optic cable or wireless like laser, radio waves, and microwaves.
- Receiver (Sink): It is the device that receives the message.
- Data: It is the information or data to be communicated. It can consist of text, numbers, pictures, sound or video or any combination of these.
- Protocol: It is a set of rules that govern the communication between the devices. Both the sender and the receiver follow same protocols to communicate with each other. The data communication takes place between two devices connected together either by wired or wireless media. The sender device generates the data message and send it through the communication channel using some protocol. After the message is sent the receiver receives the message using the similar protocol.
- Encoder: The computer works with digital signals. The communicational channels usually use analog signals. Therefore, to send data through a communication channel, the digital signals are encoded into analog signals or into a form which can be transmitted through transmission medium. This is called encoding. The device that carries out this function is called encoder.
- Decoder: The Computer works with digital signals. The communication channels usually use analog signals. Therefore, to receive data from a communication channel, the coded analog signals or any other encoded form is converted back to digital signals. This is called decoding. The device that carries out this function is called decoder.
Mode of Communication
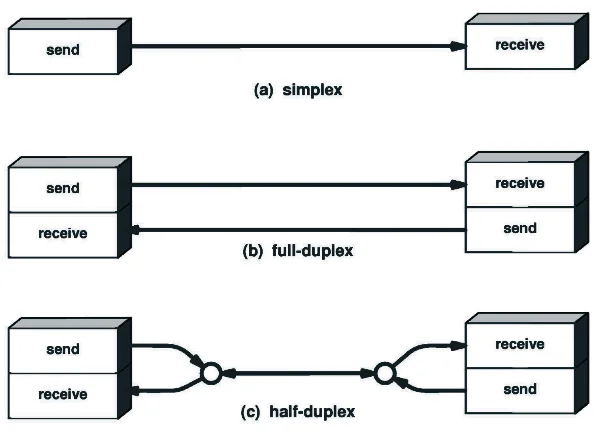
Mode of communication normally refers to the ways in which communication takes place or data gets transmitted between source and destination nodes. Modes of data transmission direct the direction, mechanism of data flow between devices.
- Simplex Communication
- Duplex Communication
a. Half Duplex
b. Full Duplex
-
Simplex Communication:
In this type of communication data transmission takes place only in one direction. It is also called a unidirectional communication mode. Radio, Television, Newspaper and keyboard to CPU Communication are some of the most common example of simplex communication.
Features:
⮚ Data are transmitted in only one direction.
⮚ The sender sends data and receiver receives only.
⮚ There is not bidirectional communication.
⮚ Listeners cannot reply immediately.
⮚ Radio and television broadcast are its examples.
-
Duplex Communication:
In duplex communication mode data transmission is possible from both directions. The receiver can immediately respond to the sender. The duplex communication can be categorized into two groups.
Half Duplex:
In this type of communication mode data can be transmitted in both directions, but only in one direction at a time. Both sender and receiver cannot transfer the data at a time. While sending data it cannot receive it and while receiving data it cannot send.
Features:
⮚ Data are transmitted in both direction but single direction at one time.
⮚ Receiving end acts as mere listener while sender sends data and vice versa.
⮚ The communication is slower.
⮚ Walkie Talkie used by the police man is the best example of half-duplex communication mode.
Full Duplex
Full Duplex communications allows data to flow the information at the same time. Speaking on telephone of full Duplex communication mode in which both the sender and receiver can speak simultaneously. Bidirectional communication at the same time is called full duplex communication mode.
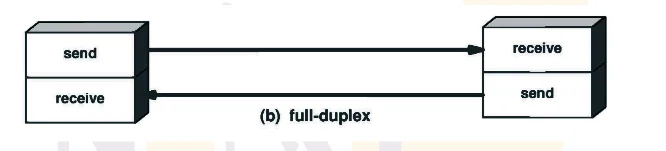
Features:
⮚ Data are transmitted in both direction at the same time.
⮚ When one end sends data other end can receive as well as send data.
⮚ Communication is faster.
⮚ Telephone is an example of full duplex mode.
Difference between simple, half and full duplex
| S.N. | Simple | Half Duplex | Full Duplex |
| 1. | It is a uni-directional communication. | It is a two way directional communication but one at a time. | It is a two way directional communication simultaneously. |
| 2. | Sender can send the data but can’t receive the data in it. | Sender can send the data and also can receive the data but one at time in it. | Sender can send the data and also can receive the data simultaneously in it. |
| 3. | It provides less performance than half duplex and full duplex. | It provides less performance than full duplex. | It provides better performance than simple and half duplex mode. |
| 4. | Examples: radio, newspaper | Examples: Walky-talky and wireless handset | Example: smart phone and landline phones. |
Computer Network:
⮚ Computer Network is defined as the collection of two or more autonomous computers which are interconnected together for sharing resources with the help of transmission media and set of protocols.

Services provided by the computer network:
⮚ Data sharing
⮚ Print service
⮚ File service
⮚ Database service
⮚ Application service
Advantages of Computer Network:
- Sharing resources: Software and hardware resources such as processor, storage devices, printers, scanner, etc. can be shared among us using computer network. It helps to minimize the operational cost of an organization.
- Saving Cost: Sharing of hardware and software resource avoids duplication, helps in optimal utilization of all types of resource like printer, disks, database etc.
- Faster and cheaper communication: Communication in modern days has become very faster and cheaper to send information to a long distance through network.
- Centralized control: All network resources such as computers, printer file, database, etc can be managed and controlled by a central connecting computer also known as the server.
- Enterprises and chain organization developed: One office or head of the organization can easily visualize and monitor offices and staffs geographically located in different places through videoconference, CC camera etc.
- Backup and recovery: Server is used to keep data as backup. It maintains backup of all individual computer information.
- Remote and mobile access: A remote user can access resources from the distance using computer network.
Disadvantages of Computer Network:
- Expensive: In order to install computer network, we require some extra cost to purchase networking devices such as hubs, switch, cables, etc.
- Security problems: Network security is the most challenging job for network administrator in order to protect network resources from authorized users and physical destructions.
- Needs technical person: It is very difficult to install and operate good computer network without the help of technical person.
Types of Computer Network
On the basis of size computer networks can be classified into three categories:
- PAN (Personal Area Network): The computer network formed around a person is called Personal Area Network (PAN).
⮚ It is personal device network within a limited area.
⮚ It consists of a computer, mobile, Personal Digital Assistant (PDA). It can be used for communication among these personal devices for connecting to a digital network and the internet.
Advantages
- It can be relatively secure and safe.
- It offers short-range up to ten meters.
Disadvantages
- It may establish a bad connection to other network
- It is limited within shorter distances.
- Local Area Network (LAN): A LAN is privately owned small size network. It spans only in small geographical area such as within a room, office, buildings or up to few kilometers (2 to 3 Km). It connects the network resources such as computers, faxes, printers and various networking devices.
Advantages of LAN
- It is cheaper to establish.
- Data transmission is faster than MAN and WAN.
- It has higher security to resources of the network
- It is easier to establish, manages of the network and operate
Disadvantages of LAN
- It is limited only to a small area.
- It can connect less number of computers comparatively.
- Cannot be used as distributed network.
- Metropolitan Area Network (MAN): A MAN can be either public or privately owned network. Its size is bigger than LAN and smaller than WAN. It spans within one metropolitan city or larger geographical area. It can connect large number of computers and heterogeneous multiple LANs within a city maximum, up to 100Km.
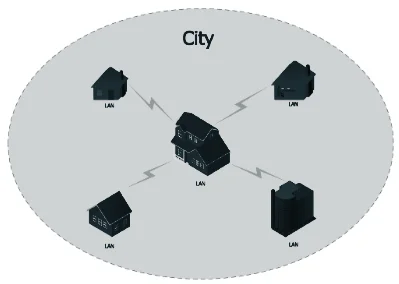
Advantages of MAN
- It covers larger geographical area than LAN.
- It can connect large number of computer than LAN.
- We can use guided as well as unguided type of transmission media.
Disadvantages of MAN
- It is expensive to set up then LAN.
- Transmission speed slower compared to LAN.
- It is complex to establish, manage and provides security.
- Wide Area Network (WAN): A WAN is basically public type heterogeneous network. It is the largest sized network and connects millions of computers, thousands of LANs, hundreds of MANs around the countries, continents and even the whole world.

Advantage of WAN
- It covers larger geographical area than LAN and MAN.
- It can connect large number of computer compared to LAN and MAN.
- Using WAN communication can be done over a large distance.
Disadvantage of WAN
- It is expensive to establish, manage and operate.
- It is the slowest type of network compared to that of LAN and MAN.
- Highly qualified manpower are required to establish and run these type of network.
Differentiate between LAN and WAN
| S.N. | Local Area Network (LAN) | S.N. | Wide Area Network (WAN) |
| 1. | Area covered within a local site. | 1. | Distance up to thousands of K.M. |
| 2. | Higher data transfer rates (10 Mbps to 1Gbps even more). | 2. | Data transfer rate is less |
| 3. | It has low error rates. | 3. | It has higher error rates. |
| 4. | It uses simple protocol, low cost devices and low cost installation. | 4. | It uses complex protocols, expensive devices and high cost installation. |
| 5. | It can support limited number of hosts. | 5. | It can support large number of hosts. |
| 6. | Eg. Star, cellular topologies etc. | 6. | Eg. Internet and intranet |
Comparison of LAN, MAN and WAN
| S.N. | LAN | MAN | WAN |
| 1. | The computer network limited over small geographical area such as building or room. | The computer network spread over the city or country is known as MAN . | The computer network spread over the world is known as WAN. |
| 2. | It is owned by an private organization. | It can be owned by private or public organizations. | There is no single ownership or WAN . |
| 3. | The bandwidth of LAN is high. i.e. data transmission rate. | The data transmission rate is slower in comparison to LAN. | The data transmission rate is slowest in comparison to LAN and MAN. |
| 4. | There is less congestion in LAN. | There is more congestion in MAN. | There is more congestion in comparison to LAN and WAN. |
| 5. | It is easy to design and maintain. | It’s design and maintenance is difficult than LAN. | It’s design and maintenance is difficult than LAN and MAN. |
| 6. | There is more fault tolerance. | There is less fault tolerance. | There is also less fault tolerance. |
| 7. | It is used in school, college, hospital…etc. | It is used in city, towns. | It is used for countries, continent and globe. |
| 8. | Transmission channels are normally twisted pair cables. | Transmission channel are fiber optics, coax cable. | Communication channel ranges from fiber optics cables to communication satellites. |
| 9. | It Stands for Local Area Network | It stands of Wide Area Network | It stands for Metropolitan Area Network. |
Transmission media:
A transmission media is defined as the means of communication between two networking devices that helps to transfer data from sender to receiver and vice versa.
⮚ Transmission channel is the path through which data are transmitted from source to destination.
⮚ The path through which data transmit from source to destination is known as communication media.
Transmission media is broadly classified into two groups.
- Bound (guided)/ Wired media
- Unbound ( unguided) / Wireless media
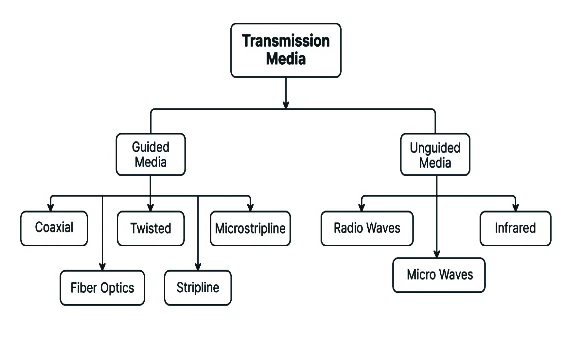
1) Bound (guided)/ Wired media
⮚ Guided Media are those communication channels that directly link with each other through cables or other physical media.
⮚ Data are transmitted in the closed path through transmission media.
⮚ Data gets transmitted through wires or cables in guided media.
⮚ In guided media, there is a direct connection between source and destination nodes.
⮚ Guided media has high bandwidth, low cost, and high security.
⮚ Data transmission is faster than wireless.
⮚ The most commonly used guided media are Twisted Pair cable, Coaxial Cable and Fiber Optics.

2) Unbound ( unguided) / Wireless media
⮚ The data transmitted in this medium is through electromagnetic waves so that any physical wire or cable is not required for the transmission.
⮚ Unguided media transmission is bounded by geographical areas.
⮚ Different types of unguided media are: Microwave, Radio wave, satellite communication, Bluetooth, Infrared, Wi-Fi, Li-Fi.
Difference between Guided Transmission and Unguided Transmission Medium
| S.N. | Guided Transmission Medium | S.N. | Unguided Transmission Medium |
| 1. | Signal is directed and contained by the physical limits of the medium. | 1. | It has no physical medium for the transmission of electromagnetic signals. |
| 2. | It is called wired communication or bounded transmission media. | 2. | It is called wireless communication or unbounded transmission media. |
| 3. | The signal energy propagates through wires in guided media. | 3. | The signal energy propagates through air in unguided media. |
| 4. | It types are twisted pair cable, coaxial cable and fiber optic cable. | 4. | It types are radio wave, microwave and infrared. |
| 5. | Examples: Twisted pair cable, coaxial cable and fiber optic cables. | 5. | Examples: Microwave or radio links and infrared light. |
-
Wired or Guided Media or Bound Transmission Media:
The transmission of data and information from source to destination by using physical medium like wires are called bounded transmission media. Its types are as follows.
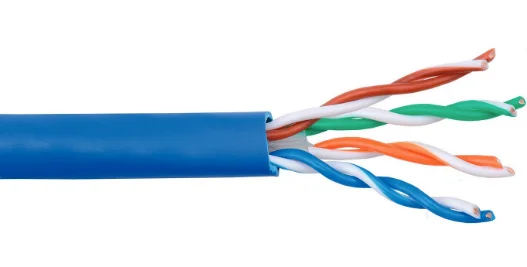
1) Twisted pair cable
i) Shielded Twisted pair cable (STP)
ii) Unshielded Twisted pair cable (UTP)
2) Coaxial Cable:
2.1. Thinnet
2.2. Thicknet
3) Fiber optics
-
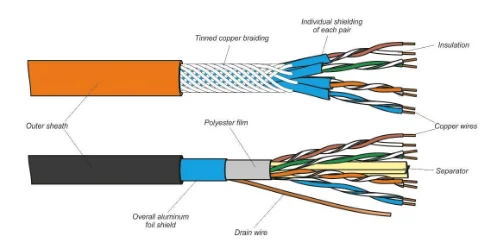
Twisted pair cable:
A pair of copper wires is twisted to each other in a helical path making the same structure as a DNA molecule.
– The reason for twisting is to reduce electrical interference.
– It is the cheapest and easily available wire.
– It is mostly used in telephone systems.
Advantages
- It is cheaper than other cables.
- It is light and thin. So, it is flexible for LAN.
- It can travel data in short distance with higher bandwidth.
Disadvantage
- It is only used for short distance transmission.
- It can be affected by electrical and magnetic field.
- It is slower type of transmission media compared to other cables.
- STP (Shielded Twisted Pair): Shielded Twisted Pair cable is identical to UTP but it contains the extra shield covering the each pairs of cables. The installation of STP is comparatively difficult than UTP and they are more expensive than UTP but has high bandwidth.
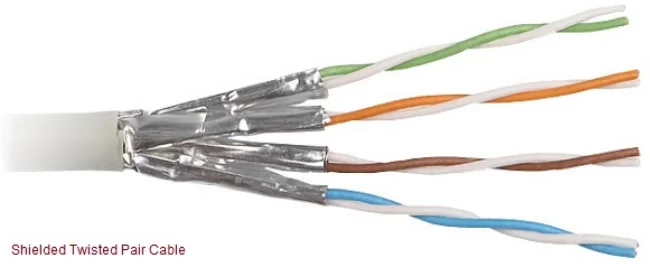
Features of STP Cable:
» Better performance and high data transfer rate.
» Eliminates cross talk
» Faster than UTP
» More expensive
- UTP (Unshielded Twisted Pair): UTP is a commonly used cable because it is easy to install and is suitable for data and voice transmission. Unlike STP, UTP cable doesn’t have the extra protection shield.
Features:
▪ Less expensive.
▪ Easy to install.
▪ High speed capacity.
▪ Susceptible to external interference.
▪ Lower capacity and performance than STP.
▪ Short distance transmission.
Difference between UTP and STP
| S.N. | UTP | S.N. | STP |
| 1. | Electromagnetic interference and noise is more in UTP | 1. | STP cable reduce electrical noise within the cable and from outside of the cable. |
| 2. | It offers speed or throughput of about 10 to 1000 Mbps. | 2. | It offers speed or throughput of about 10 to 100 Mbps. |
| 3. | It offers maximum cable length of about 100 meters. | 3. | It supports maximum segment of length about 100 meters. |
| 4. | UTP is widely used for data transmission within short distance and is very popular for home network connecting. | 4. | STP is mainly used for connection of enterprises over a long distance. |
| 5. | The cost of UTP is less when compared to that of STP. | 5. | STP is costlier than UTP. |
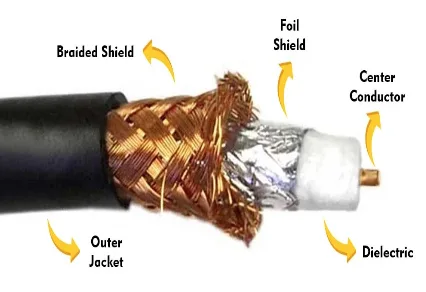
2. Coaxial Cable:
Coaxial cable is a type of copper cable specially built with a metal shield and other components engineered to block signal interference. It is primarily used by cable TV companies to connect their satellite antenna facilities to customer homes and businesses.
Coaxial cable contains two conductors inner and outer, which are separated by an insulator. These two conductors lies parallel to each other. The inner conductor is made up of copper wire which is covered by an inner insulator. The inner insulator is again covered by outer conductor or metal foil. Outer metal wrapping is used as a protection against noise and as the second conductor which completes the circuit. The outer conductor is covered with an insulating cover.
Advantages:
- It is faster and reliable than twisted pair cable.
- It can transfer data over medium range of distance.
Disadvantages
- It is not appropriate for relatively larger distance.
- It is expensive than twisted pair cable.
- It is rarely used in computer network.
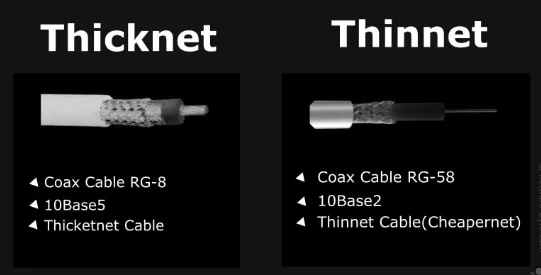
Coaxial cable is of two types:
(a) Baseband transmission (Thin net): It is defined as the process of transmitting a single signal at high speed.
(b) Broadband transmission (Thick net): It is defined as the process of transmitting multiple signals simultaneously.
3. Fiber Optics:
It is the most advanced media in communication, which uses light rather than electricity to transmit information. Optical fiber is very thin media, which is measured in microns and is very hard to identify with our naked eye. They’re designed for long-distance, high-performance data networking, and telecommunications. Fiber optic cables support much of the world’s internet, cable television, and telephone systems.
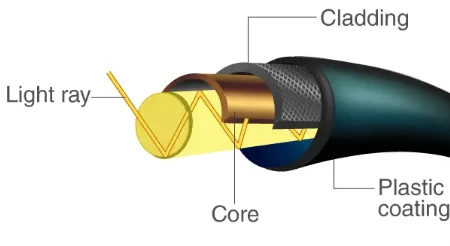
Features:
- Data are transmitted in the form of light signals.
- It is made up of glasses or plastics cover with fiber to protect.
- It is difficult to install.
- It has high bandwidth.
- Data can transfer longer and faster than twisted pair and coax cable.
Advantages:
- It has higher bandwidth that means it can handle large volume of data.
- This medium can be used for long distance transmission.
- It is the most secured and error free transmission medium.
Disadvantages:
- It is one of the expensive type of transmission media.
- It is not used for short distance transmission.
- Highly qualified and technical manpower are required to operate on fiber optics.
- Difficult to install and Fragile in nature.
-
Wireless or Unguided Media or Unbound Transmission Media:
Unbound transmission is also called wireless or unguided media. If there is no physical connectors (wires) between the two communicating device is called wireless transmission media. Its types are as follows.
- Radio Wave
- Microwave
- Infrared
- Satellite Communication:
- Radio wave:
Radio wave are the signals ranging frequency in between 3 KHz and 1 GHz. When the antenna transmits the radio wave, they are propagated in all directions. Due to this the sending and receiving antenna doesn’t need to be in line of sight position. Antenna is responsible for converting outgoing data packets into radio waves and vice-versa.

Features:
⮚ It is wireless communication technology that transmits voice or data over the air using a lower frequency band than microwaves.
⮚ The signal is travel in up and down manner so that it can reach any place until the strength of waves falls.
⮚ AM and FM radios and cordless phones use radio waves for transmission.
- Microwave:
Microwave, in contrast, have been used in data communications for a long time. They have a higher frequency than radio wave and therefore, they can handle larger amounts of data. There are, of course, problems with microwaves attenuation and environmental interference.
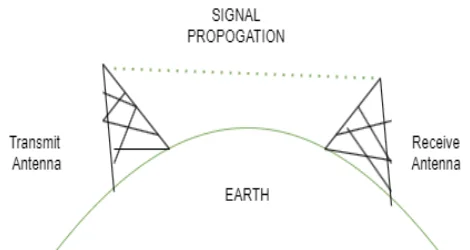
⮚ Microwave transmission is the line of sight transmission.
⮚ The transmit station must be in visible contact with the receive station.
⮚ The microwave is unidirectional.
⮚ This sets the limit on the distance between stations depending on the local geography.
⮚ The microwave is another type of electromagnetic waves that have a frequency range of 1 GHz to 300 GHz.
⮚ In this transmission, whenever the signals are transmitted through an antenna, proper alignment of sending antenna and receiving antenna should be maintained.
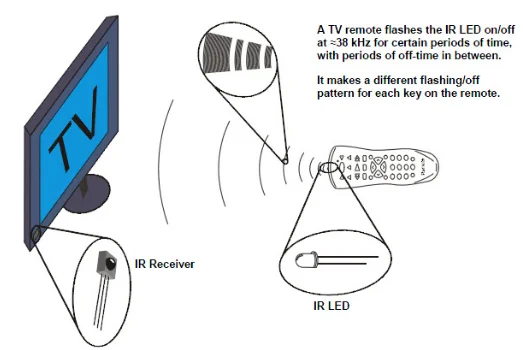
- Infrared:
Infrared offers a great unbound photonic solution like fiber-optic cabling. Infrared communications use light. So, they are not bound by the limitations of electricity. They are normally used for short range communication such as in communication of remote and TV, AC etc.
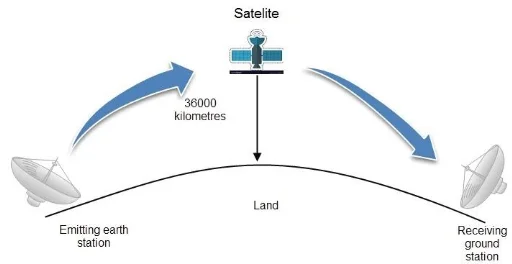
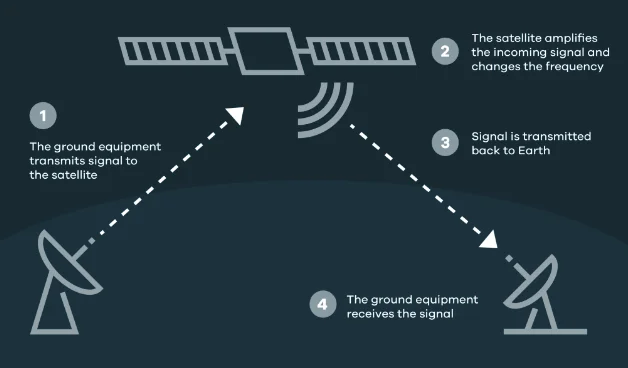
Satellite Transmission:
These are the artificial satellites which are placed in the space for the purpose of communication between different antennas available of on the earth. These artificial satellites facilitate the transmission of signals between stations of the earth. They relays and amplifies radio telecommunication by creating communication channel between source transmitter and destination transmitter.
Transmission Impairments Terminologies
(Jitter, Singing, Echo, Crosstalk, Distortion, Noise, Bandwidth and Number of receivers)
Jitter:
⮚ When we make a call over internet with anyone and suddenly line drops and their voice starts breaking up, it’s called jitter.
⮚ Jitter is defined as a variation in the delay of received packets.
⮚ Jitter is when there is a time delay in the sending of these data packets over your network connection.
Singing:
⮚ Singing is the result of sustained oscillations due to positive feedback in telephone amplifiers or amplifying circuits.
⮚ Singing may be regarded as echo that is completely out of control. This can occur at the frequency at which the circuit is resonant.
Echo:
⮚ Echo in telephone systems is the return of a talker’s voice. It is most apparent to the talker himself or herself. Secondarily, it can also be an annoyance to the listener.
⮚ Echo is a major annoyance to the telephone user. It affects the talker more than the listener. Two factors determine the degree of annoyance of echo: its loudness and its length of delay.
Crosstalk:
⮚ Crosstalk is a disturbance caused by the electric or magnetic fields of one telecommunication signal affecting a signal in an adjacent circuit.
⮚ It is an effect of a wire on another. One wire acts as a sending antenna and the transmission medium acts as the receiving antenna. Just like in telephone system, it is a common experience to hear conversation of other people in the background. This is known as cross talk.
Distortion:
⮚ Distortion is the change in the form or shape of the signal. Signals are made up of different frequencies are composite signals.
⮚ Distortion occurs in these composite signals. Any change in a signal that alters the basic waveform or the relationship between various frequency components is called distortion. It is usually a degradation of the signal.
Noise:
⮚ Noise is another impairment in data communication. During data communication there are some random or unwanted signals mix up with the original signal is called noise.
⮚ Noises can corrupt the signals in many ways along with the distortion introduced by the transmission media.
Bandwidth:
⮚ Bandwidth is the amount of data transmitted through the transmission channel at certain period of time. High bandwidth means higher bits of data are transmitted and low bandwidth means less bits of data are transmitted through the communication channel.
⮚ The bandwidth of analog device is measured in Hertz (Hz) and bandwidth of digital device is measured in bps (bits per second). It is also known as data holding capacity of transmission channel.
Receiver:
⮚ Receiver, in electronics, any of various devices that accept signals, such as radio waves, and convert them (frequently with amplification) into a useful form. Examples are telephone receivers, which transform electrical impulses into audio signals, and radio or television receivers, which accept electromagnetic waves and convert them into sound or television pictures.
Network architecture:
Network architecture refers to the various services provided by the network and it also deals with how data is transmitted from one computer to others.
- Client server network: An arrangement of computers to resource sharing and communicate each other through a central device (server) to all workstations (clients) is called client server architecture. One or more computers in the network act as server which provides services to other computers which are called clients.
⮚ The server is a high capacity high speed computer with a large memory.
⮚ Server contains the network operating system.
⮚ The central server manages, organize, and coordinate all network clients on the network.
⮚ The most common service is provided by different servers are file services, print services,
⮚ Message services and database services.
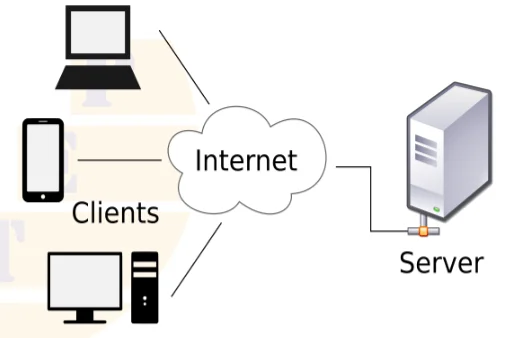
Advantages
- Centralized administration is possible through this network.
- High security can be provided by suing appropriate server.
- It is appropriate for large organization.
- Data recovery and backup process is easier.
Disadvantages
- If server fails whole network is affected.
- It is expensive due to use of dedicated server.
- It is complex to establish and manage.
- Experienced administrator is required to operate.
- Peer-peer network: In peer-to-peer architecture computers are connected individually in pair (one to-one connection). A peer-to-peer network is the type of network in which all computers in the network act as both a client and a server i.e. all computers can both request and provide services.
⮚ Each workstations act as both a client and a server.
⮚ There is no central repository for information and no central server to maintain.
⮚ Peer to peer network are generally simpler and less expensive.
⮚ A peer to peer network is also known as a distributed network.
⮚ Peer to peer computing or networking is a distributed application architecture that partitions task or workstations between peers.
⮚ Peers are equally privileged and equal participants in the application.
⮚ Each node shares its sources with other nodes in the network.
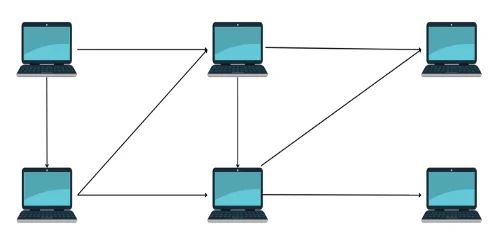
Advantages
- It is simple, cheap and easier to set up.
- Since there is no dedicated server, user can manage their own server.
- Failure of a computer in a network doesn’t effect the other computer in a network.
Disadvantages
- Data security is very poor in this type of architecture.
- Data recovery and backup is difficult.
- It is not appropriate for large scale organization.
- Network administration is difficult it without dedicated Server.
Difference between Client Server and Peer to peer
| Client Server | Peer to peer |
| 1. It is also known as centralized or server based network. | 1. It is also known as distributed network. |
| 2. It has central server computer. | 2. There is no central server computer. |
| 3. The central server manages, organize, and coordinate all network clients on the network. | 3. Peers are equally privileged and equal participants in the application. |
| 4. Client server network are more expensive. | 4. Peer to peer network are generally simpler and less expensive. |
| 5. It has high security. | 5. It is less security. |
| 6. If server crashes there is a chance of data loss. | 6. Data and information is shared around the network, so less chance of data loss. |
| 7. Example, Google server, Yahoo server and Bank etc. | 7. Example One to one computer and Bluetooth connectivity etc. |
Network or LAN topology and its types
Network topology refers to the physical layout of the network. It shows the geographical representation of all the links and linking devices, also called nodes. It is the shaped of Network. The main objectives of the network topology is to find out the most economical and efficient way of transmission channel.
Its types are as:
- Bus Topology: Computers are connected to a single continuous cable that is called ‘bus’. It acts as backbone. It is based on client server network architecture.
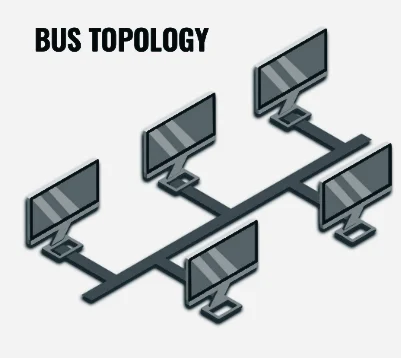
Advantages
- It is simple and easy to setup and extend the network.
- It required less cable.
- If any computer in the network downs, then it does not affect the whole network.
- We can easily connect and disconnect any number of computers in the bus.
Disadvantages
- Data traffic is very high in bus.
- If there is problem in main cable then entire network goes down.
- It is very difficult to find out the fault in the bus.
- Star Topology: Computers in the network are connected to each other with the help of central connecting device hub or switch or server. It is based on client server architecture. It is the most popular and widely used topology for LAN.
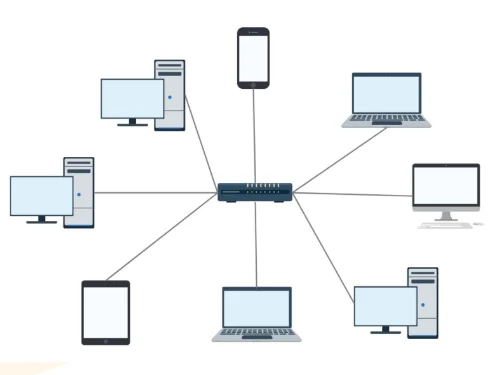
Advantages
– It is simple, reliable and easy to set up and re-configuration.
– It is flexible to connect new computer and remove existing computer in the network.
– It is very easy to find out fault.
– If any computer in the network goes down, then other computers can continue their functions.
Disadvantages
– It requires very large amount of cables.
– It is expensive topology.
– If there is any problem in central device hub or switch then the entire network will be down.
– The data traffic is high in central device hub.
- Ring Topology: Computers are interconnected to each other by making a closed circular structure that means each computer is connected to other two adjacent computer in either network architecture.
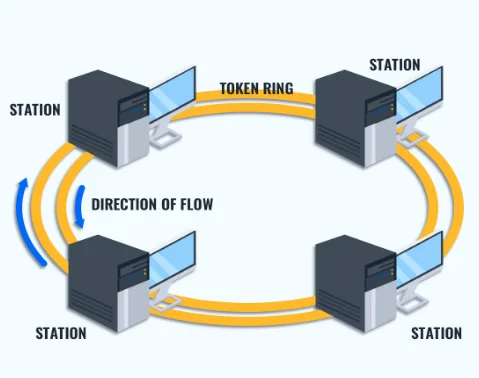
Advantages
– It is simple and inexpensive topology.
– There is less chance of data collision because of unidirectional data transmission.
– There is no server so each computer has equal access facilities to the resources.
– Its performance is better than bus topology for small size network.
Disadvantages
– It is not flexible topology so it is difficult for adding and removing new nodes.
– It is not suitable for large size network.
– If there is problem in any computer or connection then the entire network goes down.
– It is very difficult to find out the errors in the network.
- Mesh Topology: Every computer in the network has point to point connection to all other computers by using multiport connector. It is also based on peer to peer architecture.
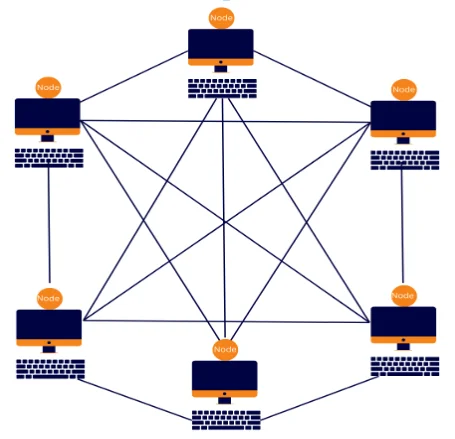
Advantages
– It is fastest and most reliable topology.
– Failure in any computer or transmission media does not affect the rest of the network.
– There is less amount of data traffic due to multiple paths.
Disadvantages
– It is very much complex and most expensive topology.
– It is difficult to find an error in the network.
– It is difficult to add and remove nodes in the network so it is not flexible.
– It requires maximum amount of cables and multiport connectors.
- Tree Topology: Tree topology is the extension of bus or star topology. Data can flow from top to bottom and vice versa.
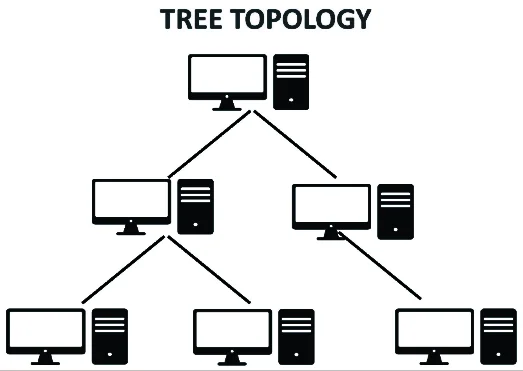
Advantages
– It is easy to manage network as per our needs.
– It is very flexible so we can add and remove any number of nodes.
– It is easier to find the fault nodes or hubs in the network.
Disadvantages
– The failure of root node will cause the failure of entire network.
– It is expensive because it needs large number of cable and network device.
– The data traffic is high at root nodes.
- Hybrid topology: If two or more topologies are combined together then it is called hybrid topology. So it is very difficult to design and to implement the hybrid topology. It is expensive too.
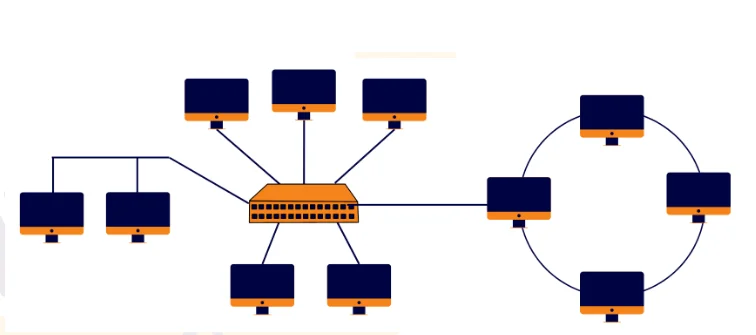
Advantages
⮚ Reliable
⮚ Scalable
⮚ Flexible
⮚ Effective
Disadvantages
⮚ Complexity of design
⮚ Costly connecting devices
⮚ Costly infrastructure
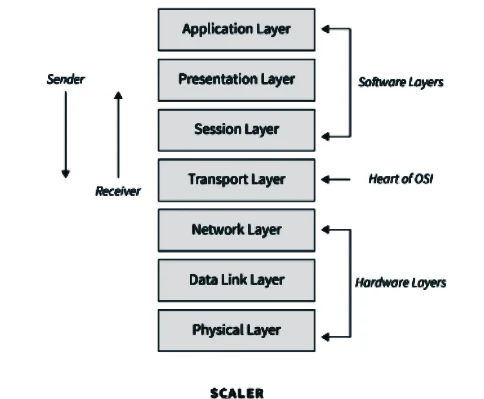
OSI (Open System Interconnection) reference model
It is based on a proposal developed by the international organization for standardization (ISO). The model is called ISO OSI reference model, because it deals with connecting open system i.e. the system that are open for communication with other system.
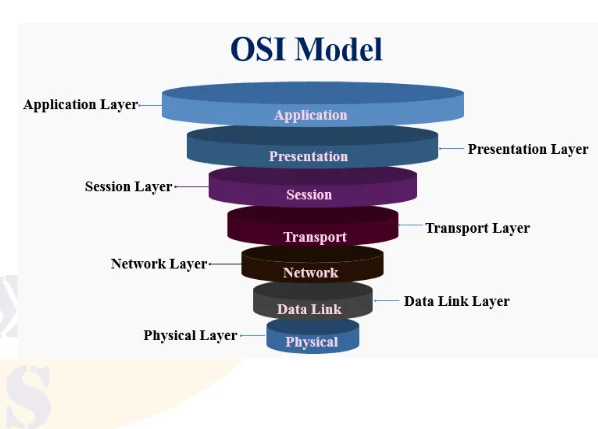
- Physical Layer: This layer concerned with transmission of bit it determines voltage level for 0 & 1. It also determines the data rate of the system. This layer involves standardized protocol dealing with electrical & signaling interface.
- Data Link Layer: It handles error in physical layer. This layer ensures the correct delivery of frame to the destination address. It consists of 2 parts or 2 sub-layers. i.e.
i. Logical Link Control
ii. Media Access Control
- Network Layer: This layer is concerned with transmission of packet. Network layer protocol chooses the best path to send a package called routing. Two protocols are widely used in network layer.
i. X.25 Protocol
ii. Internet Protocol
- Transport Layer: It provides the mechanism for the exchange of data between end systems. It ensures that the data received is in fact in order. Following jobs are performed by this layer.
i. Port Addressing
ii. Segmentation & Reassemble
iii. Connection Control
- Session Layer: It is responsible for requesting logical connection to be established for communication process. This logical connection is termed as session. It also provides data synchronization between two communication terminals.
- Presentation layer: This layer translates format data to adapt to the needs of the application layer & nodes at both receiving & sending end of communication process. It handles data communication, formatting, encryption, decryption, etc.
- Application Layer: It is the top-most layer of OSI model & provides user access to the network. It provides services that support user application, such as database access, email & file transfer, etc.
Network Connecting devices:
The devices of computer network which are used to connect network is called the network connecting devices. We can connect two or more networks together to create larger network. A LANs can be connected others LANs, MANs or WAN.
- Network Interface Boards or Network Interface Card (NIC):
The NIC contains the electronic circuitry needed to ensure the reliable communications between workstations and servers. The NIC is the electronic interface between the computer and the LAN cabling. The card itself uses a bus-specific edge connector to plug into the computer motherboard. On the exposed side of the NIC, there are cabling ports that plug directly into the LAN cabling.
- Repeaters:
As the name implies, repeaters repeat network data. In general, repeaters operate at the electronic level and contain no real intelligence. A repeater accepts weak signals, electrically regenerates them and then sends the messages on their way. There are two types of repeaters: amplifiers and signal-regenerating repeaters.
- Hubs:
Technically speaking, a hub is simply a multiport repeater. In addition to regenerating network data, hubs add form and function to the layout of the LAN. In many topologies, the hub is the central component of the network transmission media. There are three types of hubs. They are the passive hub, active hub and intelligent hub.
- Bride:
It is a device, which connects different network segments and passes data with the same communication protocols. It is the connecting device between two or more hubs.
– It operates at layer 2 (Data Link Layer) of OSI Model.
– It reduces unnecessary traffic problem by controlling broadcasting.
– Bridges are more intelligent than hubs because they maintain MAC address tables in them and forward data looking on it.
- Router:
A router transmits information from one network to another. The router selects the best path to route a message, based on the destination address and origin. The router can direct traffic to prevent head-on collisions and smart enough to know when to direct traffic along back roads and shortcuts.
– Direct signal traffic efficiently.
– Route message between any two protocols.
– Route message between different topologies.
– Route message across fiber optic, coaxial, and twisted-pair cabling.
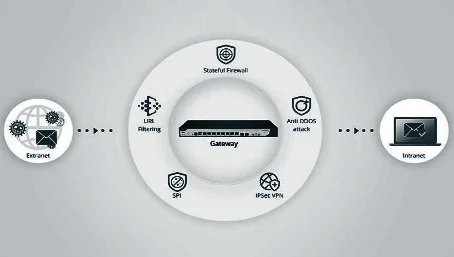
- Gateways:
Gateways are just like routers but much more complex and powerful than routers. They are slower than router and expensive. A gateway has all the features of router and bridges but it can translate instruction set on sending network into receiving network.
– Gateways make communication possible between different architecture and environments.
– Gateways having higher layer functionalities and works on multiple layer protocols.
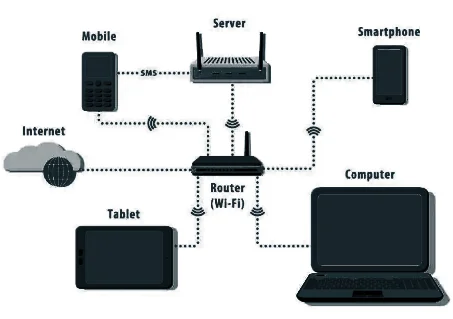
- Wi-Fi:-
The term Wi-Fi suggests Wireless Fidelity. It is hardware and software devices. It is wireless technology and network connecting device. Wi-Fi is not a technical term. The technical term of Wi-Fi is “IEEE802.11”
– It has limited range.
– Wi-Fi is used in many personal computers, video game consoles, MP3 players, smart phones, printers, digital camera, laptops computers and other devices.
– Wi-Fi is used to create wireless LAN to connect computer system.
- Bluetooth:
Bluetooth is a wireless technology standard for exchange data over short distance from fixed and mobile devices. Bluetooth is used to create personal area networks (PANs) with high levels of security.
- Infrared (IR):
Infrared (IR) light is electromagnetic radiation with a wavelength longer than that of visible light and below the red light. These wavelengths correspond to a frequency range of approximately 100 GHz to 100 THz and include most of the thermal radiation emitted by objects near room.
Some basic terms:
Internet
The Internet is an interconnected network of thousands of networks and millions of computers linking business, educational institutions, government agencies, and individuals together.
Uses / Application of internet
- Search information
- Email service
- Communication
- File Transfer
- Remote login
- Publishing of articles, reports, and newsletter.
- Online education
- Online shopping
- Entertainment.
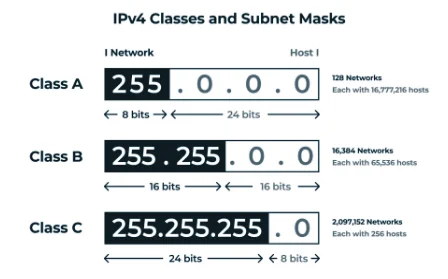
Subnet Mask
The subnet mask number helps to define the relationship between the host (computers, routers switches, etc.) and the rest of the network. As the name indicates, the subnet mask is used to subdivide a network into smaller, more manageable chunks.
Gateway
A gateway is a network node that serves as an access point to another network, often involving not only a change of addressing but also a different networking technology.
IP Address
An Internet Protocol address (IP Address) is an unique identification number assigned to each devices connected in a network that uses Internet protocol for communication. The typical IP address looks like 216.27.67.137
IP address are expressed in decimal as above which is easier for us to remember, but computers communicate in binary. So same IP address looks like 11011000.00011011.00111101.10001001
IP address has four sets of number separated by a period ( . ), These sets are Called Octets. IP address perform mainly two functions. One is identification of Network and Identification of particular host in that network.
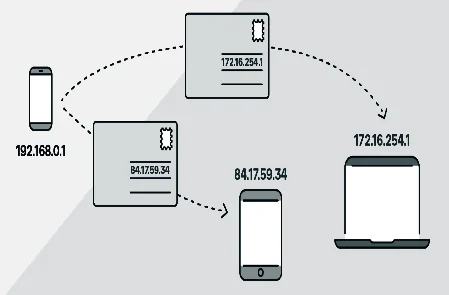
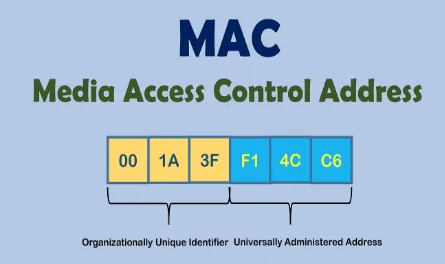
MAC address
Media Access Control (MAC) address also known as hardware or physical address is unique number associated with a network adapter (NIC). It is used to uniquely identify each device (node) of a network. MAC address is usually assigned by the manufacturer of a network interface card (NIC) and are stored in its ROM. All NIC developed contains unique MAC address. It is a 12 digit hexadecimal number (48 bit in length) and are Written in following formats.
MM:MM:MM:SS:SS:SS or MM-MM-MM-SS-SS-SS
The first half of the address contains ID number of the adapter regulated by an Internet standards body and other half represent the number assigned by the manufacturer. For example: 00:A0:C9:14:C8:29 The prefix 00A0C9 indicates manufactures Intel Corporation and 14C829 indicates a particular host.
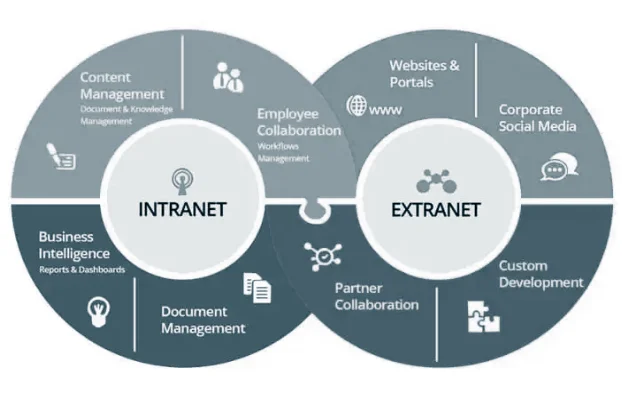
Intranet:
An intranet is a private network that uses internet protocols, to securely share part of an organization’s information between its employees. An intranet is a Local Area Network or Wide Area Network that uses TCP/IP protocol but, belongs to a corporation, school, or organization.
The intranet is accessible only to the organization’s workers. If the intranet is connected the Internet, then it is secured by a firewall to prevent unauthorized users from gaining access to it.
Advantages of an Intranet
1.Workforce productivity: Employees can easily access and share information in-between their workgroups which enhances productivity.
2.Time: With intranets, organizations can make more information available to employees in any time.
3.Communication: Intranets can serve as powerful tools for communication within an organization.
Extranet:
An extranet is a private intranet that can be accessed by outside users over the secure channel. To gain entrance to the extranet resource, an external user must log on to the networks by providing a valid user ID and password. The extranet is a combination of the public Internet and the closed intranet.
Difference between Intranet and Internet
|
Intranet |
Internet |
| 1. It is a private network. | 1. It is a public network. |
| 2. Intranet users are your own employees who know a lot about the company, its organizational structure and special terminology. | 2. Internet user know much less about your company and also care less about it. |
| 3. The intranet is used for everyday work inside the company. | 3. The Internet is mainly used to find out information. |
| 4. The intranet will have many official draft reports, project progress reports, human resource information, and other detailed information. | 4. Internet have all types of information based on requirements. |
| 5. Intranet has less amount of information. | 5. Internet has tremendous amount of information. |
| 6. Intranet can work on low and mid-bandwidth. | 6. Internet requires higher bandwidth. |
Network Tool
Network tools are used for supporting easier and effective network connections. Some of the network tools are:
- Packet tracer: Packet Tracer is an innovative and powerful network simulator that can be used for a practice build own network with routers, switches, wireless, and much more. It allows to experiment with network behavior, build models and to ask “what if” questions. It is used to trace the movement of data packets in data communication. Packet Tracer provides simulation, visualization, authoring, assessment, and collaboration capabilities to facilitate the teaching and learning of complex technology concepts.
- Remote login: Remote login allows a user terminal to connect to a host computer via a network or direct telecommunications link, and to interact with that host computer as if the user terminal were directly connected to that host computer. Remote Login is a process in which user can login into a remote site i.e. computer, and use services that are available on the remote computer. With the help of remote login a user can understand result of transferring result of processing from the remote computer to the local computer.
Protocols:
A communication protocol is a formal description of digital message formats and the rules for exchanging that message in between computer systems. Protocols define a set of formal rules describing how to transmit data especially across a network.
-
- TCP/IP (Transmission Control Protocol/Internet Protocol): TCP/IP is a layered set of protocols TCP is reliable, but complex transport-layer protocol. It is stream connection-oriented and reliable transport protocol. TCP/IP is the protocol used by Internet. It adds connection-oriented and reliability features. TCP is responsible for making sure that the data is transmitted to other end. It keeps track of what is sent, and retransmits any data that has not reached its destination. The Internet Protocol (IP) is the principal communication protocol used for transmitting data packets across and network using the Internet Protocol Suite. Internet exist due to TCP/IP.
- FTP (File Transfer Protocol): This protocol is used for transferring data between client and server over TCP/IP (Internet). Hence, it is responsible for uploading and downloading files to and from the server.
- UDP (User Datagram Protocol): UDP is simple, connection less, unreliable transport protocol. It performs very limited error checking. It is mainly used for transmitting multimedia data, which requires faster transmission and error checking is not used.
- SMTP (Simple Mail Transfer Protocol): SMTP is a standard protocol for transmitting electronic mail (email) by the internet. It is a Internet mail protocol. It is a TCP/IP protocol used to send emails.
- POP (Post Office Protocol): POP is also a protocol for transmitting email. It is simple but has limited functionality. It is an application layer Internet standard protocol used by clients to access e-mail from a server over a TCP/IP connection i.e. internet. POP3 (POP version 3) is used at present. POP3 is supported by most modern webmail services such as Gmail and Yahoo Mail.
- HTTP (Hypertext Transfer Protocol): HTTP networking protocol for distributed, collaborative, hypermedia information systems. It is used transmitting hypertext or HTML based document. It is the foundation of data communication for the World Wide Web used by web browser to communication with respective servers.
- HTTPS (Hypertext Transfer Protocol Secure): HTTPS is combination of Protocol with the SSL/TLS protocol to provide encrypted identification of a network. HTTPS connections are often used in World Wide Web for sensitive transactions. The main objective of HTTPS is to create a secure channel over an insecure network.